FAQ: CNAPP, CSPM, and cloud vulnerabilities
What is the difference between CNAPP and CSPM?
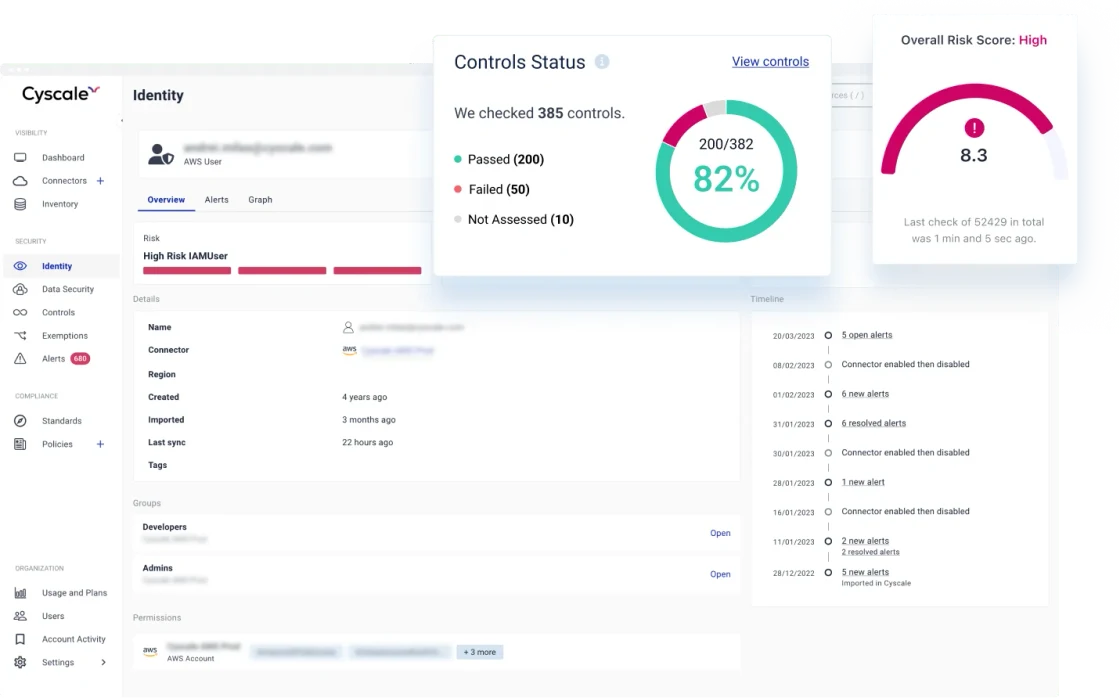
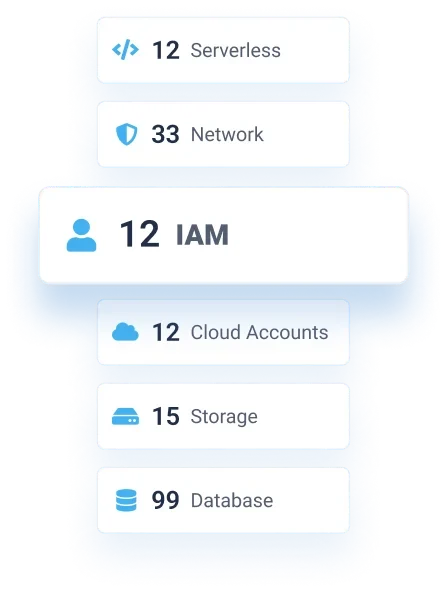
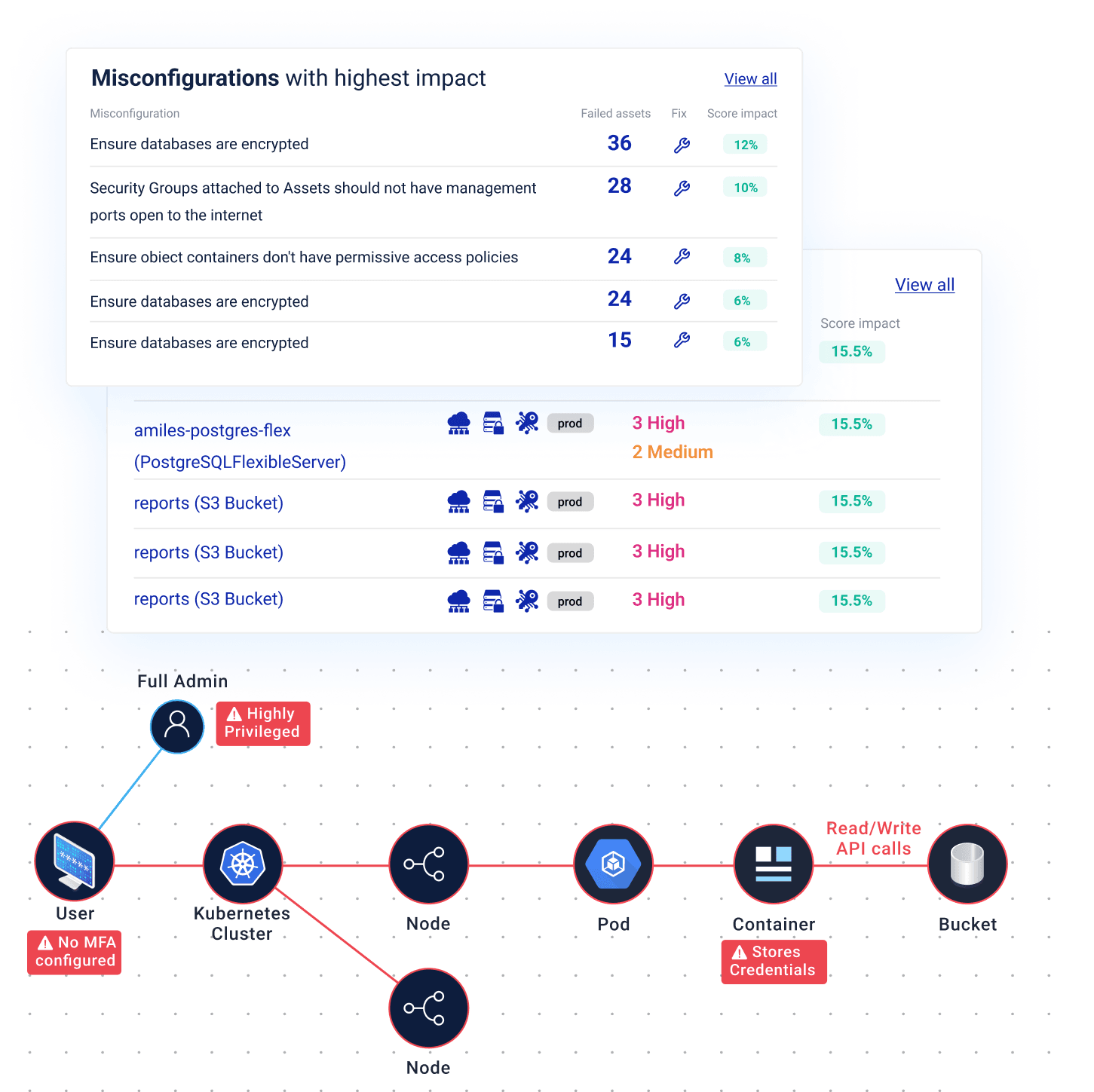
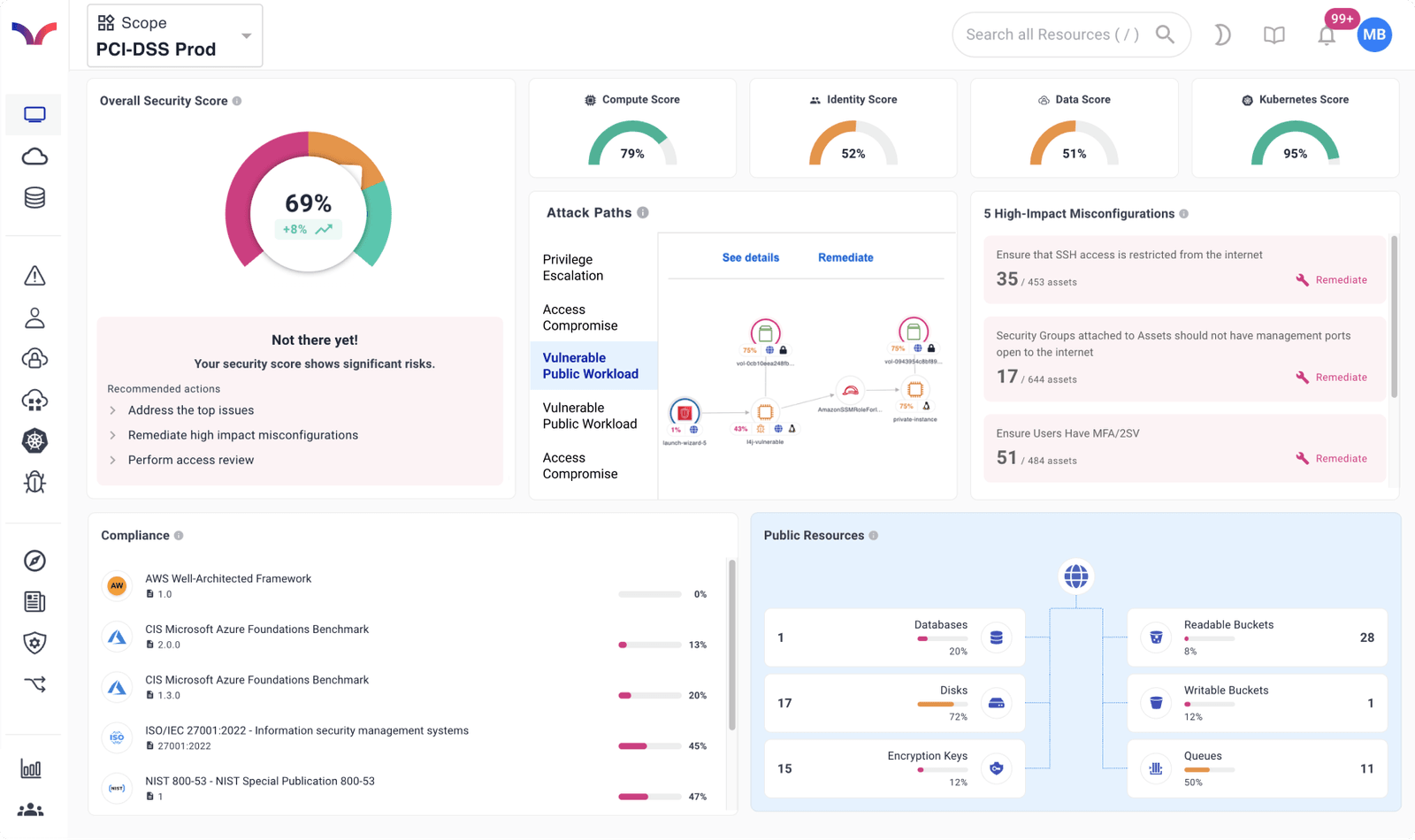
CSPM focuses on cloud misconfiguration detection, posture drift, and compliance checks. CNAPP is broader: it combines CSPM with vulnerability management, identity and entitlement risk, workload context, Kubernetes visibility, data security, AI Security, and remediation workflows in one platform.
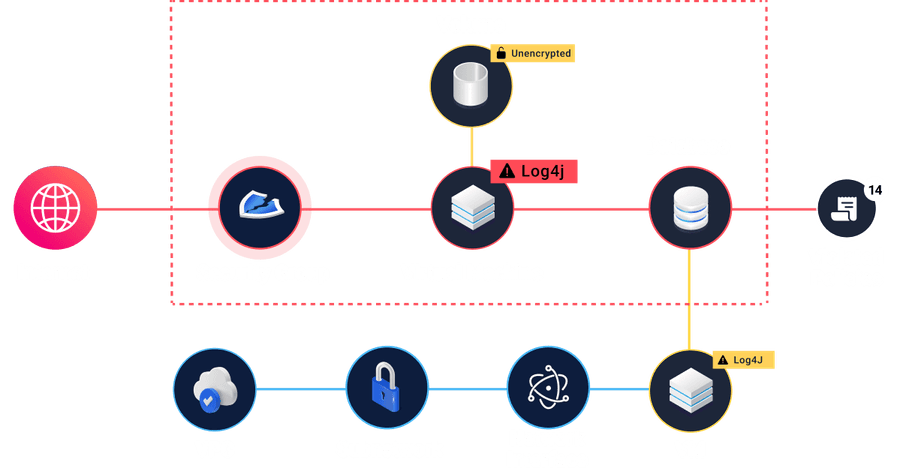
How does Cyscale prioritize cloud vulnerabilities?
Cyscale correlates vulnerabilities with internet exposure, identity reachability, asset criticality, affected workloads, data sensitivity, compliance impact, and attack paths so teams can fix the risks that are most likely to matter in production.
Is Cyscale agentless?
Most cloud connectors are agentless and use secure provider APIs. Kubernetes coverage uses the Cyscale Kubernetes agent because cluster runtime inventory, workload context, and package metadata require in-cluster collection.
Which cloud providers are supported?
Cyscale supports AWS, Microsoft Azure, Google Cloud, Alibaba Cloud, Kubernetes, Microsoft Entra ID, Google Workspace, Okta, GitHub, and GitLab workflows, with expanding coverage for AI services and Kubernetes-hosted AI workloads.
What is AI-SPM in Cyscale?
AI-SPM means AI Security Posture Management. Cyscale discovers AI services, AI workloads, models, endpoints, agents, datasets, vector stores, and AI BOM context, then connects them to cloud identities, data paths, public exposure, and remediation priority.
Can Cyscale help with compliance and custom controls?
Yes. Cyscale maps findings to frameworks such as ISO 27001, SOC 2, PCI DSS, NIST, CIS, NIS 2, DORA, and AI Best Practices. Teams can also define custom controls and policies that reflect their own cloud and AI security requirements.
How does Cyscale handle enabled modules and plans?
Cyscale is designed to expose product modules, such as Data Security and AI Security, based on the account or plan configuration. This keeps the UI, billing view, and connector behavior aligned with what the customer has enabled.