FAQ: CNAPP platform and risk prioritization
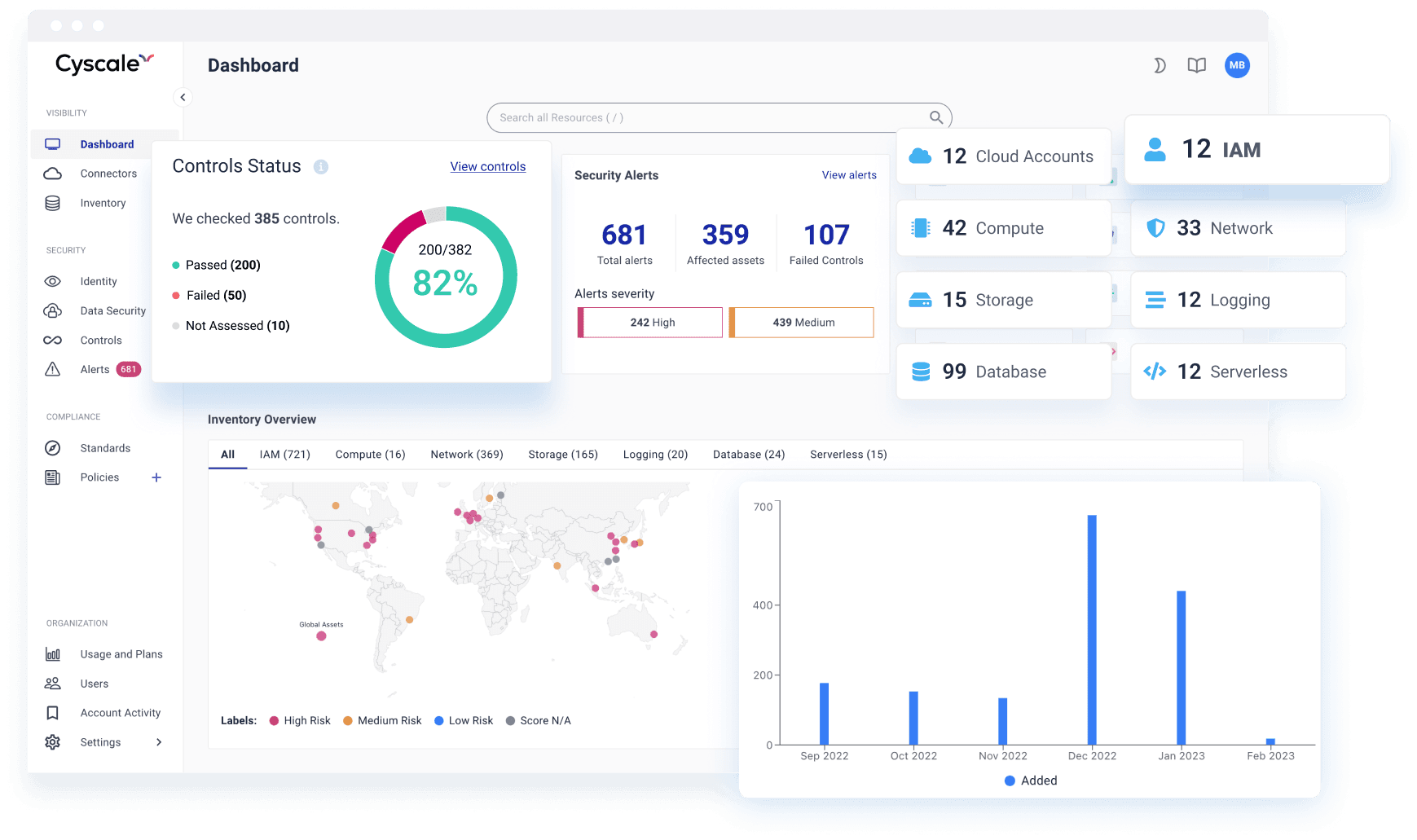
What does Cyscale CNAPP cover?
Cyscale CNAPP unifies cloud posture, vulnerabilities, identity and entitlement context, Kubernetes security, workload risk, data security, AI Security, compliance evidence, and remediation workflows across cloud accounts and runtime environments.
How is Cyscale CNAPP different from using multiple point tools?
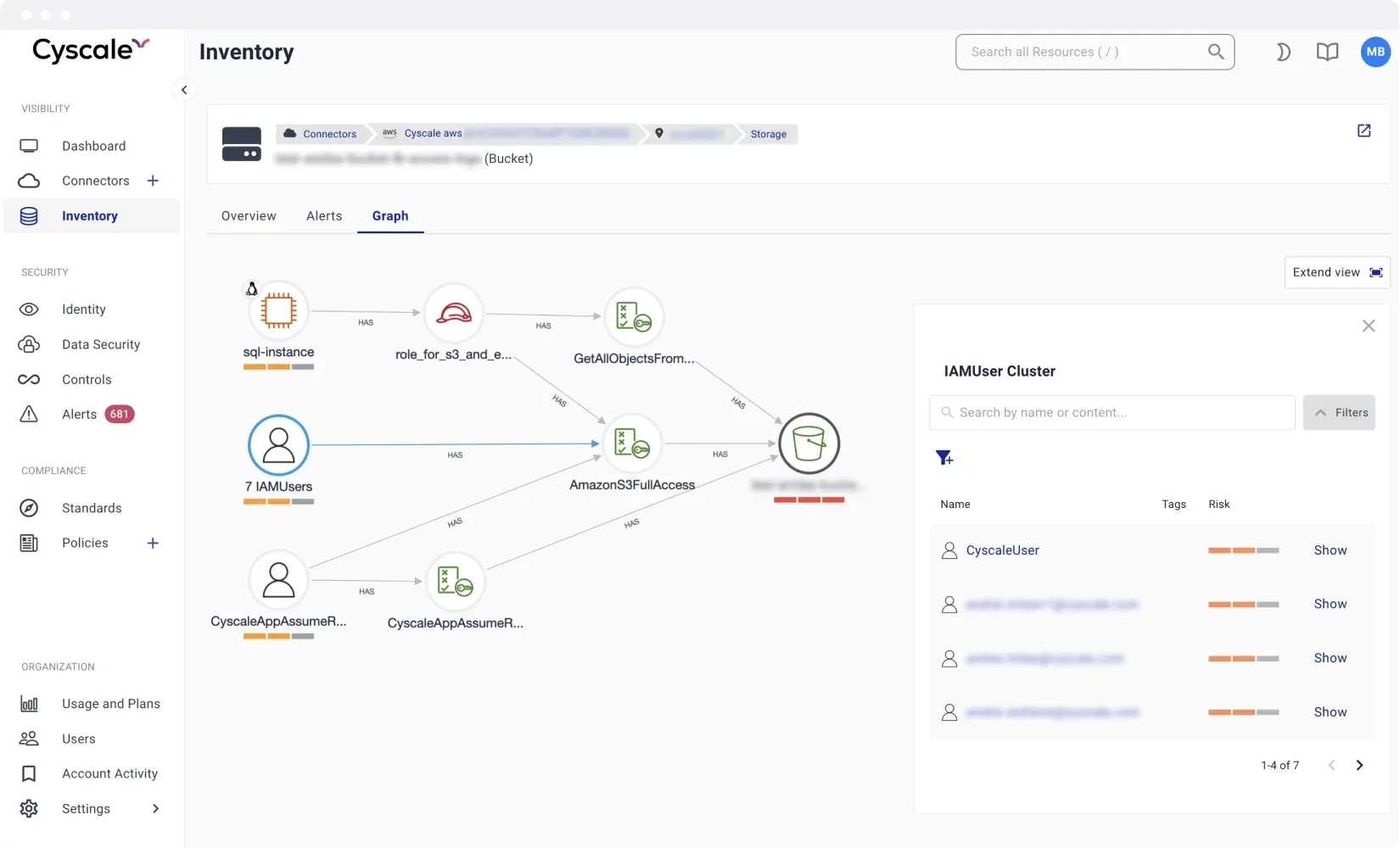
Point tools create siloed alerts, duplicate triage, and separate ownership models. Cyscale correlates findings across code, cloud, identities, workloads, data, compliance, and AI assets so teams get one prioritized queue tied to business and attack-path context.
Can Cyscale prioritize real cloud risk instead of raw findings?
Yes. Cyscale prioritizes based on exposure, exploitability, identity reachability, affected workloads, sensitive data access, compliance impact, and business context, helping teams focus on high-impact attack paths first.
Is onboarding agentless?
Most cloud onboarding is agentless and uses secure provider APIs. Kubernetes coverage uses the Cyscale Kubernetes agent because cluster runtime inventory, workload context, and package metadata require in-cluster collection.
Can security and engineering teams collaborate in one workflow?
Yes. Cyscale provides actionable remediation context and ownership-ready workflows so security, platform, and engineering teams can resolve risks without tool switching.
Does Cyscale CNAPP include AI Security?
Yes, when the AI Security module is enabled for an account or plan. Cyscale can discover AI services, AI workloads, model endpoints, agents, datasets, vector stores, AI BOM components, and risky AI relationships across cloud and Kubernetes environments.
How does Cyscale support code-to-cloud security?
Cyscale connects repositories, packages, container images, workloads, cloud assets, identities, and findings so teams can see whether a code or dependency issue reaches a live service and who should own the fix.
Can Cyscale support compliance and custom controls inside the CNAPP workflow?
Yes. Cyscale maps findings to compliance frameworks and supports custom controls, exemptions, evidence, and reports so compliance and remediation work happen from the same cloud security context.