All you need to know about protecting SaaS apps and data in the cloud
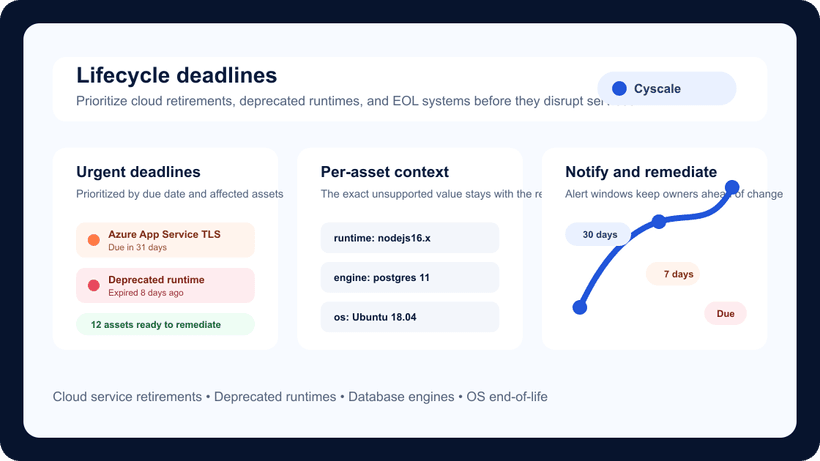
Lifecycle Deadlines Help Teams Prevent Cloud Service Disruptions
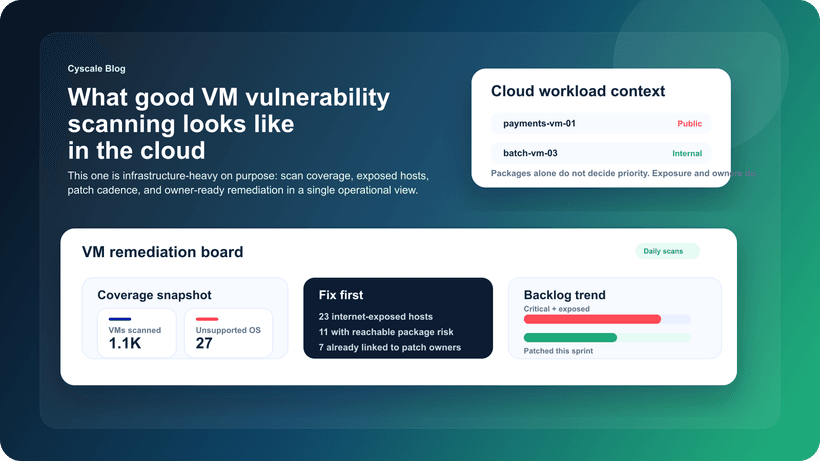
What Good VM Vulnerability Scanning Looks Like in Cloud Environments
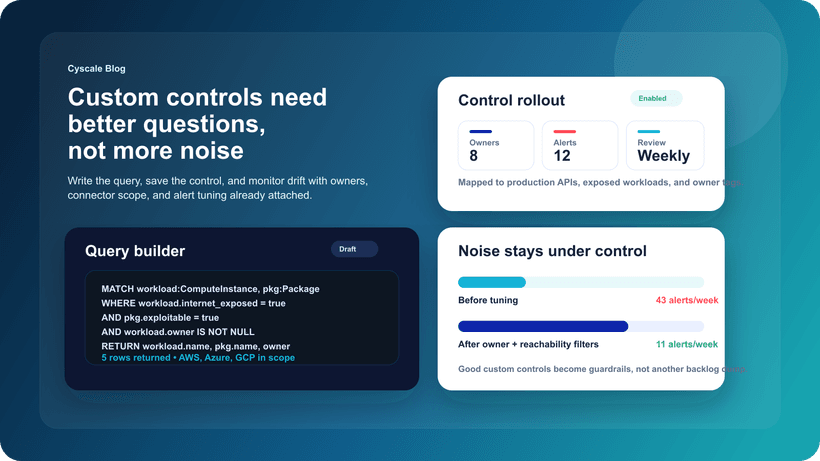
How to Build Custom Cloud Controls with Query Builder Without Creating More Noise