Powerful
Cloud Native
Security Platform
Secure Your Cloud Infrastructure with Our Advanced Security Platform
Protect your entire stack, from virtual machines to serverless environments, in any cloud environment. Our powerful platform provides advanced security features, giving you maximum cloud-native security and peace of mind to confidently accelerate innovation.
Key Components to
Build a Resilient Cloud
Security Plan
CSPM
Secure multi-cloud environments with Cloud Security Posture Management. Continuous monitoring and remediation across AWS, Azure, Google Cloud, Alibaba Cloud. Automate and streamline cloud security management, ensure compliance, and protect sensitive data.
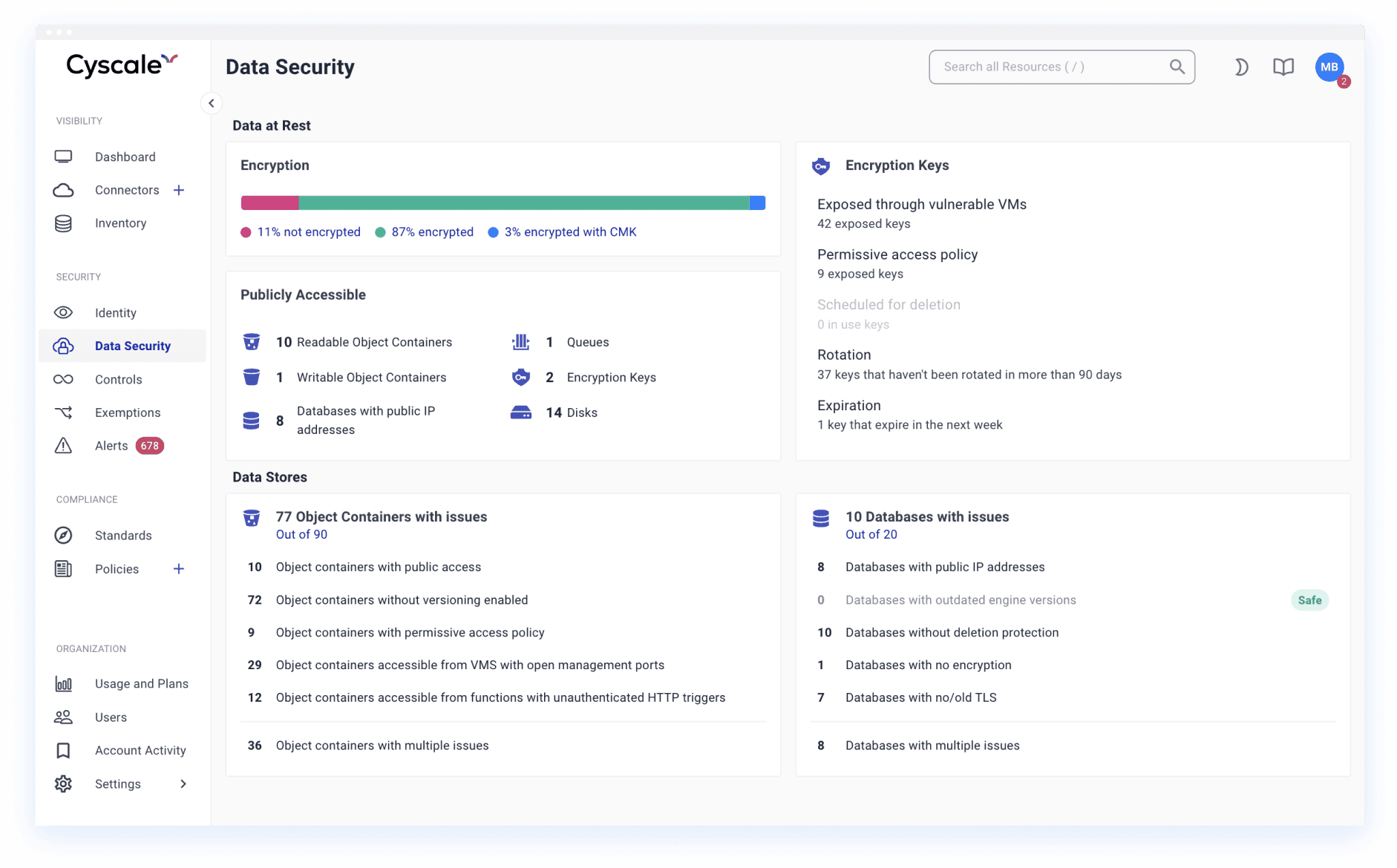
Contextual Analysis
Automatically correlate misconfigurations across compute, storage, and identity assets, determining their real impact on data security. Gain insights to prioritize and streamline remediation efforts, ultimately reducing your organization's exposure to cyber threats and vulnerabilities.
Identity and Access Management
Implement strong identity and access management controls to ensure that only authorized users can access your cloud-native infrastructure and applications. Use multi-factor authentication and role-based access controls to minimize the risk of unauthorized access.
Cloud-Native Application Security (CNAPP)
Automate prevention, detection, and response across the entire cloud-native application lifecycle to enhance security. Ensure secure supply chain, cloud infrastructure, and running workloads, regardless of deployment location. Provide end-to-end security coverage, enabling DevOps teams to build and deploy secure cloud-native applications at scale.
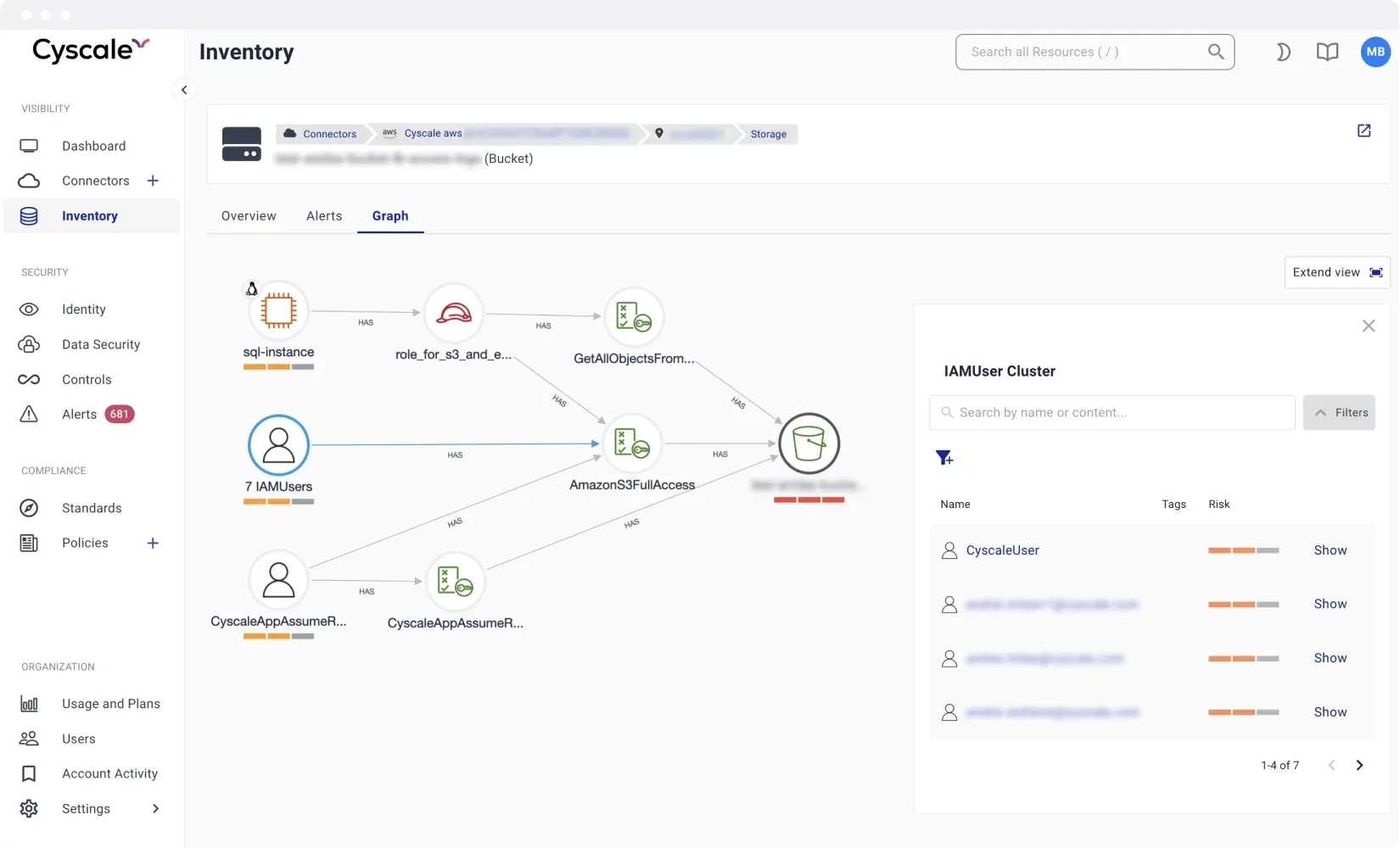
CIEM
Easily review access and track users, access levels, and permissions, including IAM asset misconfigurations. Gain insights into identities and permissions in complex multi-cloud environments, ensuring secure and compliant access management.
CWPP
Enhance your workload security with Cloud Workload Protection Platform. Perform contextual analysis of cloud misconfigurations and vulnerabilities across instances, images, containers, and serverless functions. Ensure complete visibility into your entire app stack, across any cloud environment for better security management.
Container Security
Ensure the security of your container-based apps and cloud infrastructure with Container Security solutions. Gain complete visibility over where containers are running in the cloud and perform a contextual analysis of vulnerabilities, misconfigurations, networking, and access.
Kubernetes Security
Secure your Kubernetes clusters, managed or unmanaged, with complete inventory and continuous scanning for vulnerabilities in cluster components and container images. Detect and remediate potential threats to ensure secure Kubernetes environments for your organization.
Real-time Cloud Security
with Contextual Analysis
Our Cloud-Native Application Protection Platform provides real-time security with automated contextual analysis, giving you complete visibility and control over your cloud environment. By analyzing cloud configuration, workload, and identity, it identifies the most critical attack vectors that pose a threat to your business, rather than overwhelming you with numerous alerts for vulnerabilities, permissions, and exposed services.
With our security tools, you can prioritize and address the most significant security risks, ensuring application security and the integrity of your cloud infrastructure. Automations enable continuous scanning for vulnerabilities, misconfigurations, and threats across your entire cloud ecosystem.
Integrate with all major
Cloud Providers
We support all major cloud providers from Amazon Web Services to Microsoft Azure, Google Cloud, Oracle Cloud, and IBM Cloud. You can also use Cyscale for your cloud-native security needs (VMs, network, serverless, databases, apps) for vulnerability and threat management, cloud inventory, secure cloud extension, and as a compliance and cost-reduction solution.
With our vulnerability and threat management tools, you can identify and mitigate security risks before they can be exploited. Our cloud inventory feature provides complete visibility into your cloud environment, while our secure cloud extension allows you to securely connect to remote environments.
100% Confidence with
your Cloud Compliance
Meet industry regulations
Protect sensitive data and comply with strict industry regulations in your organisation. Cyscale automatically runs all critical compliance checks and finds data at-risk across multiple cloud service providers.
PCI-DSS, SOC 2, GDPR, and more
Cyscale offers a wide range of benchmarks and frameworks, including: CIS, ISO27001, PCI-DSS, NIST,
SOC 2, GDPR.
Built-in compliance templates
You can either use policy templates as a basis for your custom policies, or create them from scratch.
500+ out-of-the-box security controls
Onboard teams in 30 minutes and coordinate efforts to apply 500+ out-of-the-box security controls.
Elevate your Cloud Native Security game with CNAPP
Strenghten your cloud security practices