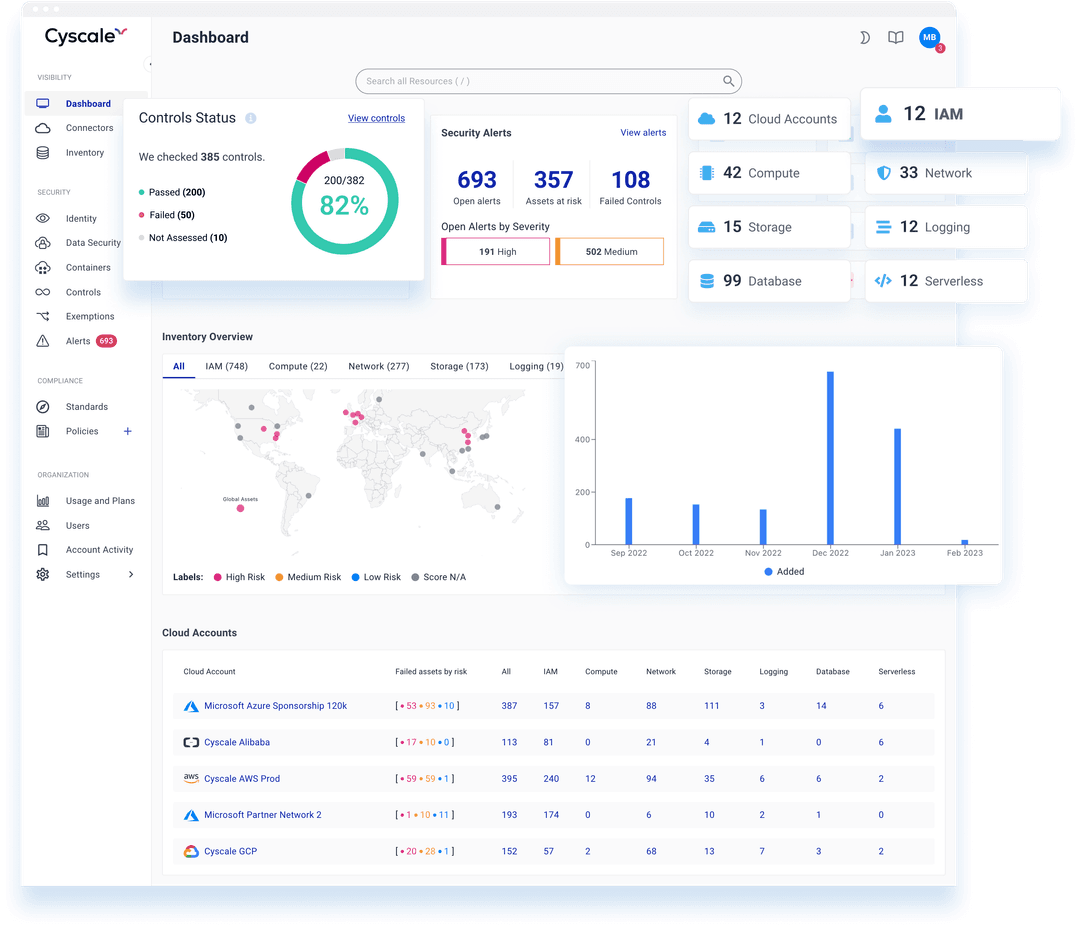
Streamline posture management for Google Cloud services and your multi-cloud environments. Get visibility into your cloud security and achieve continuous compliance.
- Security controls for Storage, Compute, Containers, cloud IAM (Identity and Access Management), Cloud SQL and many other cloud services to ensure misconfiguration coverage
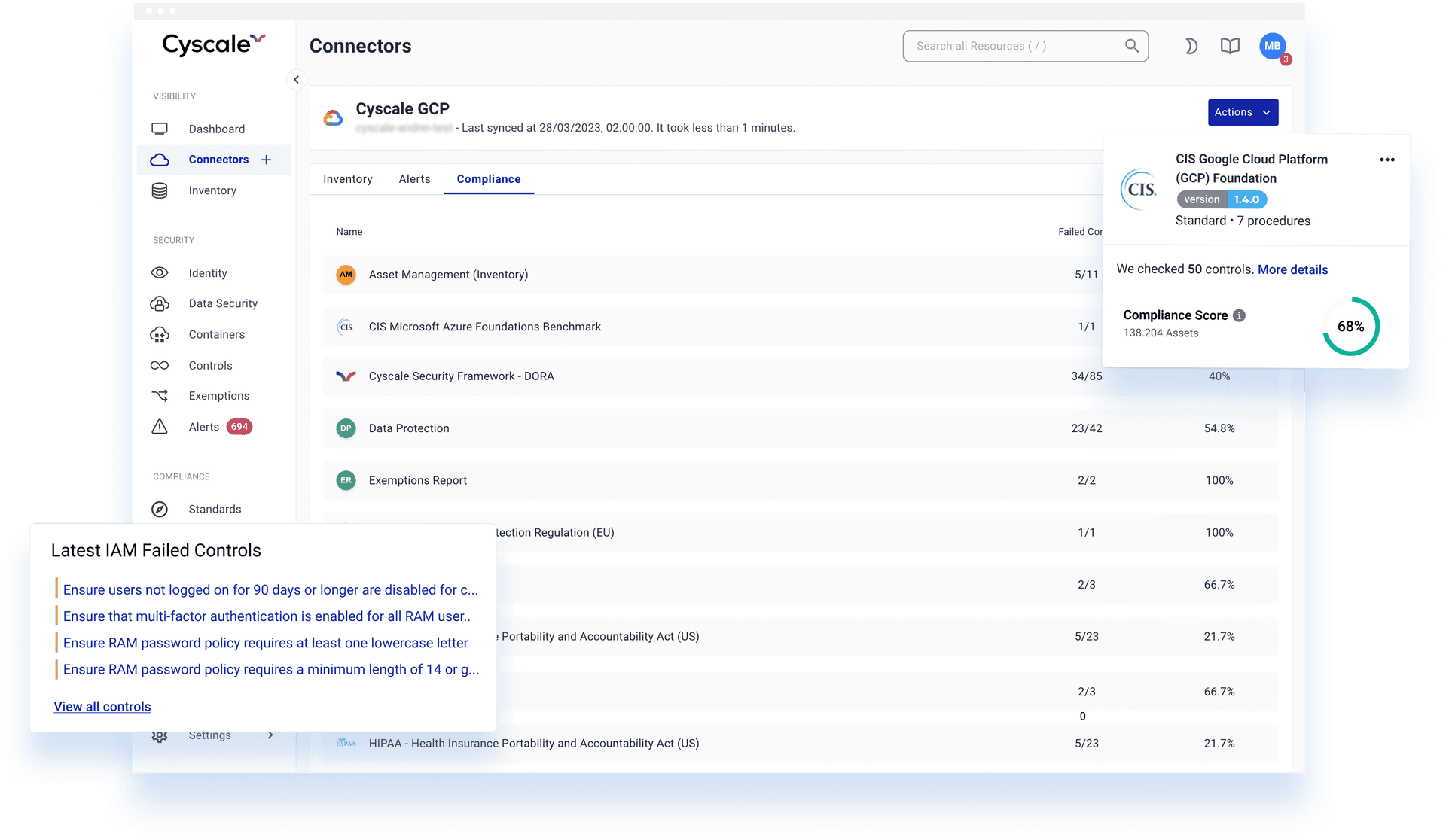
- CIS Google Cloud Platform benchmark available in-app to get guidance on and to help you follow security best practices
- Alerts to help you stay in control of dynamic cloud infrastructures and avoid cyber threats
- Improve team workflows by configuring prefered notification channels and audit logging
- Audit-ready PDF report with Asset Inventory across multiple Google Projects
- Cloud-native cybersecurity across workloads with Google Kubernetes Engine Service (GKE) management and monitoring
Moreover, secure your multi-cloud infrastructure that comprises AWS and Azure cloud computing, as well as single and public cloud environments.
Automate compliance checks & security control audits
Use Cyscale for governance automation across cloud providers and internal teams to ensure consistent security and compliance.
We keep your cloud environments under continuous assessment and provide in-app security consultancy so you make the most of your time and effort.
Coming soon: create custom Controls that tap into our Security Knowledge Graph™ and automate the Google Cloud security and compliance checks that matter most for your organization.
100% Confidence in your Cloud Compliance
Meet industry regulations
Protect sensitive data and comply with strict industry regulations in your organization. Cyscale automatically runs all critical compliance checks and finds data at-risk.
Built-in compliance templates
You can either use policy templates as a basis to configure custom policies, or create them from scratch using a smart text editor.
PCI-DSS, SOC 2, GDPR, and more.
Cyscale offers a wide range of benchmarks and frameworks, including: CIS, ISO27001, PCI-DSS, NIST, SOC2, GDPR, to help you obtain certifications.
500+ out-of-the-box security controls
Onboard teams in 30 minutes and coordinate efforts to apply 500+ out-of-the-box security controls and a large set of policies and standards covering VMs (virtual machines), access control, authentication, firewall configuration, permissions, network security, cloud identity and others.
RECOMMENDED ARTICLES
Compliance
Google Cloud - A Cloud Industry OverviewSecuring IAM - Best Practices Recommended by AWS, Azure, and Google CloudCloud Security and Compliance:
A Guide for Your Cloud InfrastructureUnderstanding serverless computing:
how you can use it and how to secure itWhat Is Data Classification And
Why Is It Important?Cloud Compliance 101:
From Basics to Best Practices
The In-Depth Guide
to Cloud Compliance
in 2026
What standards exist on the market, and who are they destined for?
Download the whitepaper to read about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.