What is cloud vulnerability management?
Cloud vulnerability management is the continuous process of finding, prioritizing, and remediating vulnerabilities across cloud workloads, containers, Kubernetes, identities, and data services.
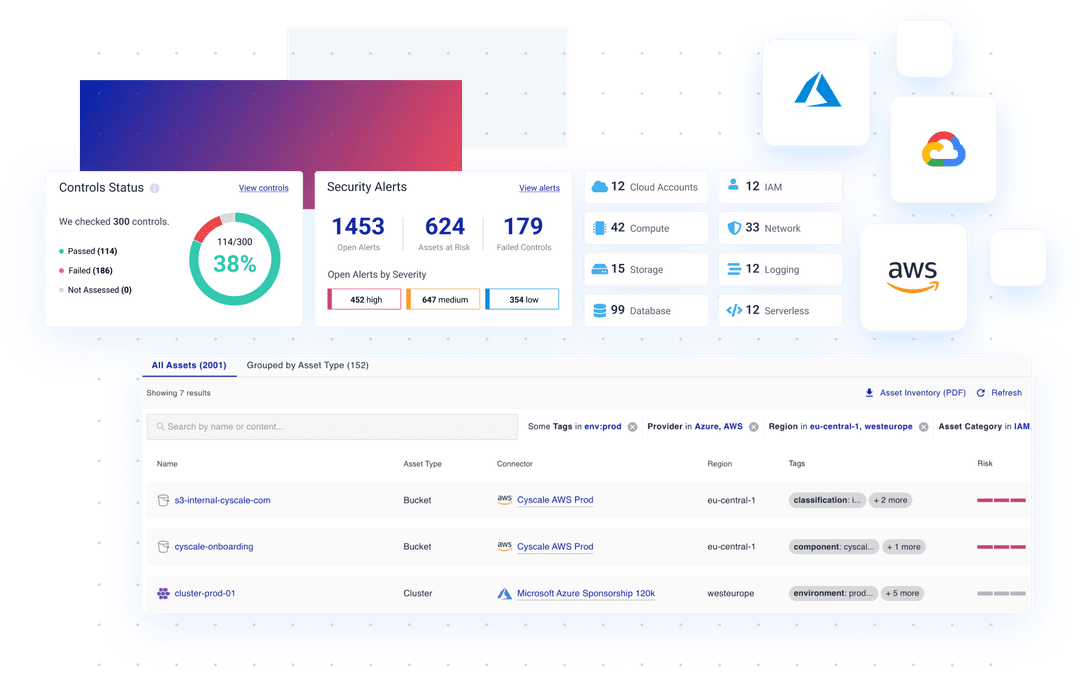
Continuously scan your multi-cloud environment, identifying vulnerabilities and ensuring compliance.
Experience real-time monitoring, intuitive insights, and streamlined security management - all through one unified CNAPP platform.
Protect Your Cloud Infrastructure
See how you can transform complex security tasks into a walk in the cloud.
Dive into real-time monitoring and protection for all your data across any cloud service.
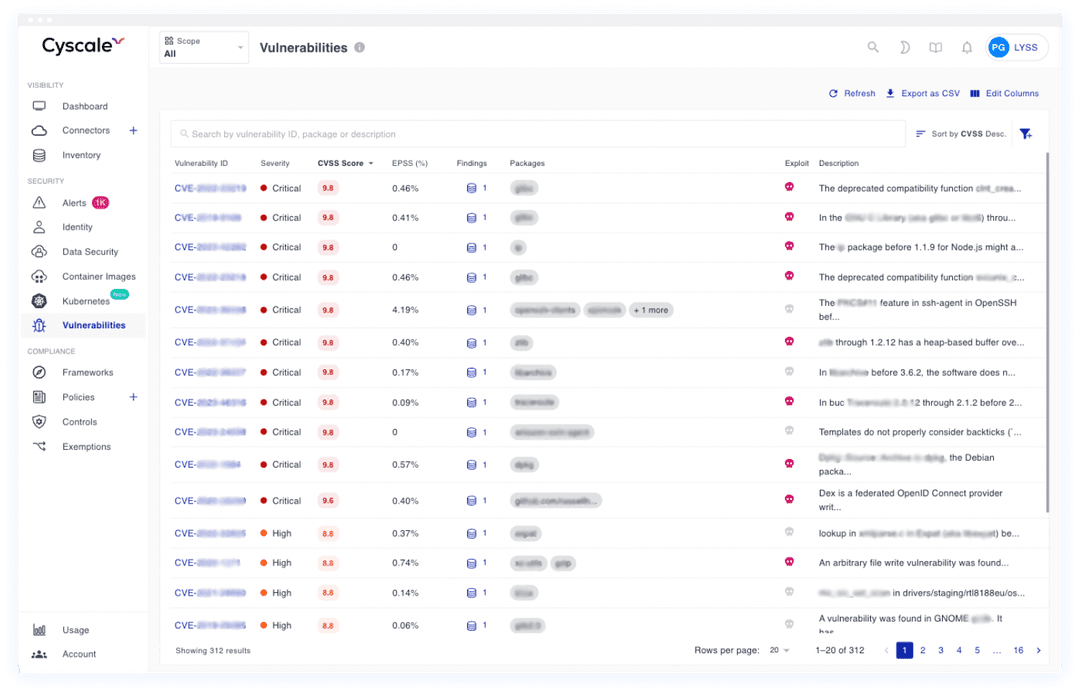
Simplify Vulnerability Management
A single pane of glass view into all cloud-based assets helps you understand:
Vulnerability programs get stuck when every issue looks equally urgent. Cyscale helps teams prioritize based on exposure, reachability, workload importance, and ownership so engineering can work on a smaller, more meaningful queue.
Meet Industry Regulations
Protect sensitive data and comply with strict industry regulations. Cyscale automatically runs all critical compliance checks across multiple public cloud providers such as AWS, Azure, and Google Cloud, as well as Kubernetes, identifying vulnerabilities that put your data at risk.
Built-in Compliance Templates
You can either use policy templates as a basis for your custom policies or create them from scratch. Control access through IAM policies, IAM roles and other IAM solutions to ensure a comprehensive identity management program and reduce the attack surface.
PCI-DSS, SOC 2, GDPR, and more
Cyscale offers a wide range of benchmarks and frameworks, including CIS, ISO27001, PCI-DSS, NIST, SOC2, GDPR, and helps you prepare for auditing.
500+ out-of-the-box security controls
Onboard teams in 30 minutes and coordinate efforts to apply 500+ out-of-the-box cybersecurity controls and a large set of policies and standards to prevent data breaches. From access control to MFA (multi-factor authentication) and the principle of least privilege, we help make regular access reviews for your cloud infrastructure quick and painless.
Cloud vulnerability management is the continuous process of finding, prioritizing, and remediating vulnerabilities across cloud workloads, containers, Kubernetes, identities, and data services.
Cyscale prioritizes vulnerabilities using contextual signals such as exploitability, identity exposure, internet exposure, and compliance impact so teams focus on the most dangerous issues first.
Yes. Cyscale supports multi-cloud environments and Kubernetes workloads, helping teams monitor and remediate vulnerabilities from a single CNAPP workflow.
Yes. Combining vulnerability management with CSPM gives teams a full picture of cloud posture risk, CVE exposure, and misconfiguration impact, which improves remediation decisions.
Pair this use case with CSPM and a unified CNAPP platform for end-to-end cloud risk reduction.
Vulnerability Playbook
The key to cloud vulnerability management is context. Security teams need to identify which vulnerabilities are actually reachable, exposed, and likely to impact high-value workloads, then route those fixes into normal delivery workflows.
Cloud Vulnerability Management Wiki Guide
Operational guidance for contextual vulnerability programs.
SCA Wiki Guide
Map vulnerable dependencies, transitive packages, and fix paths faster.
CNAPP Wiki Guide
How vulnerability management fits in full code-to-cloud security.
Container Image Scanning Wiki Guide
Understand how image contents affect workload vulnerability exposure.
End-of-Life Software Wiki Guide
Reduce unsupported runtime risk before it turns into urgent vulnerability work.
Cyscale vs Lacework
Compare operational simplicity and remediation execution.
Boost cloud security with CNAPP and advanced vulnerability management
for comprehensive, proactive threat protection.
RECOMMENDED ARTICLES
Explore effective strategies for cloud data security, including encryption, data classification, and misconfiguration remedies in this essential guide.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
SCA identifies vulnerable and risky open-source packages, transitive dependencies, license issues, and outdated components across modern software delivery pipelines.
Container image scanning finds vulnerable packages, malware, secrets, and misconfigurations inside build artifacts before those workloads run in production.
End-of-life software increases operational and security risk because unsupported components stop receiving patches, fixes, and ecosystem support.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited