What are cloud misconfigurations?
Cloud misconfigurations are insecure settings in cloud services, identities, storage, networking, or Kubernetes resources that can expose data and increase breach risk.
A single misconfiguration can have a devastating impact on your cloud security.
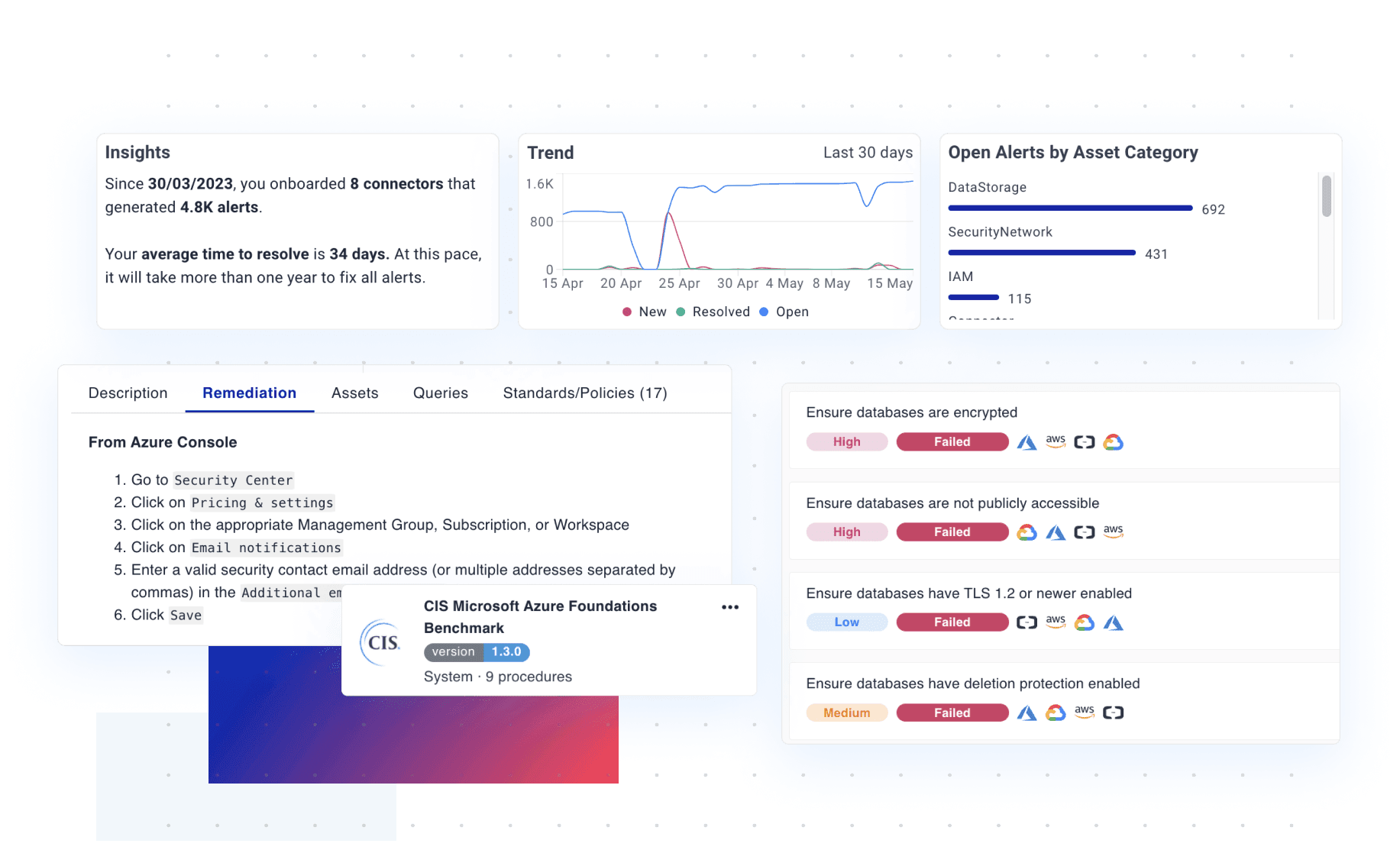
Cyscale automatically detects misconfigured services across identity, compute, storage, networking, container services, managed Kubernetes, and many more.
Get step-by-step remediation guidelines for any finding, so that you can act fast to reduce your attack surface and prevent incidents.
Don't waste time chasing false positives. Get contextual alerts when your cloud assets drift away from established security and compliance standards.
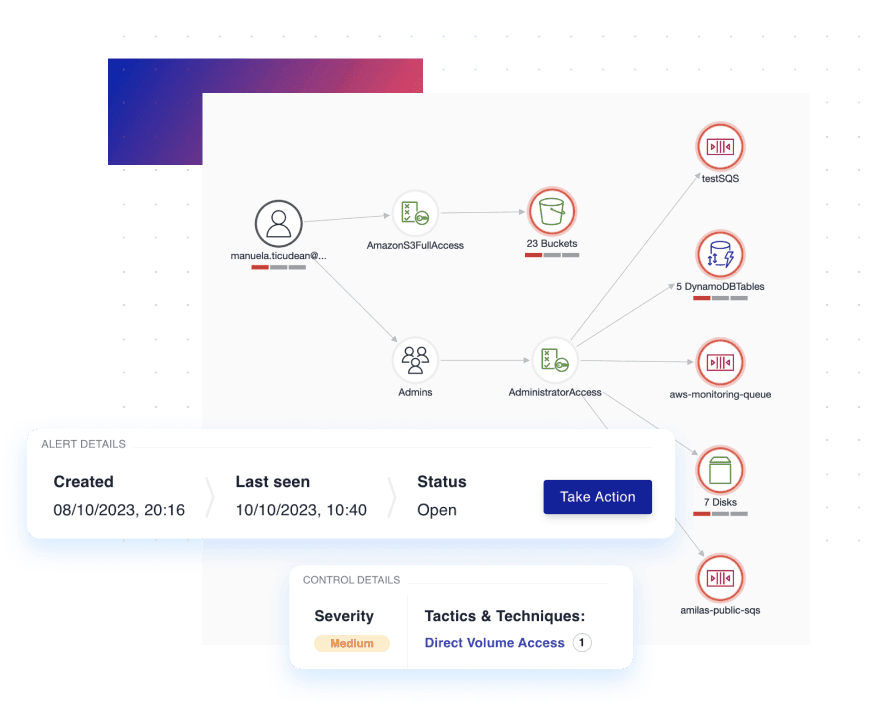
Instead of overwhelming list-based management, Cyscale's Security Knowledge Graph™ makes precise correlations between all your cloud assets and data repositories to automatically pinpoint critical security improvements.
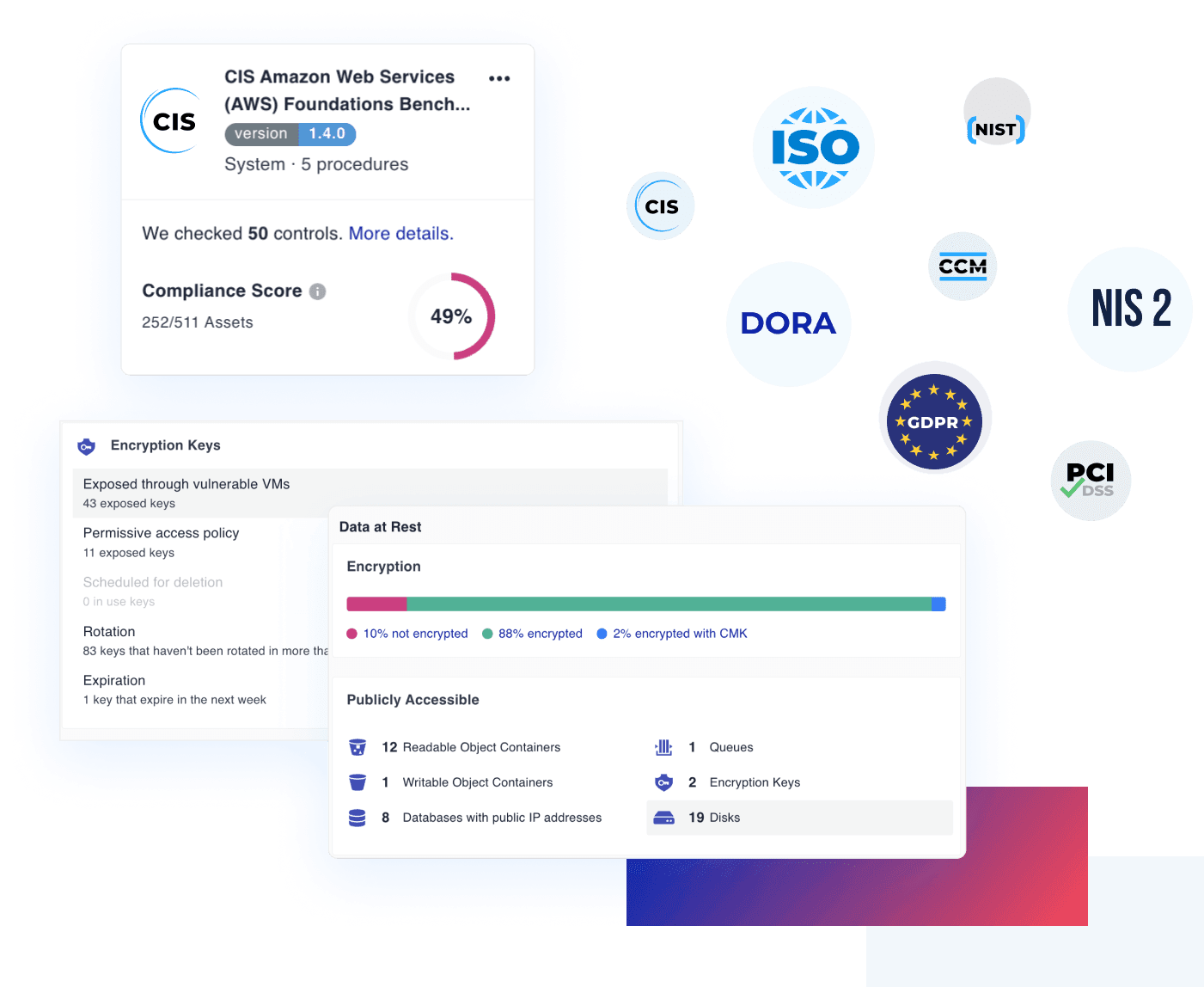
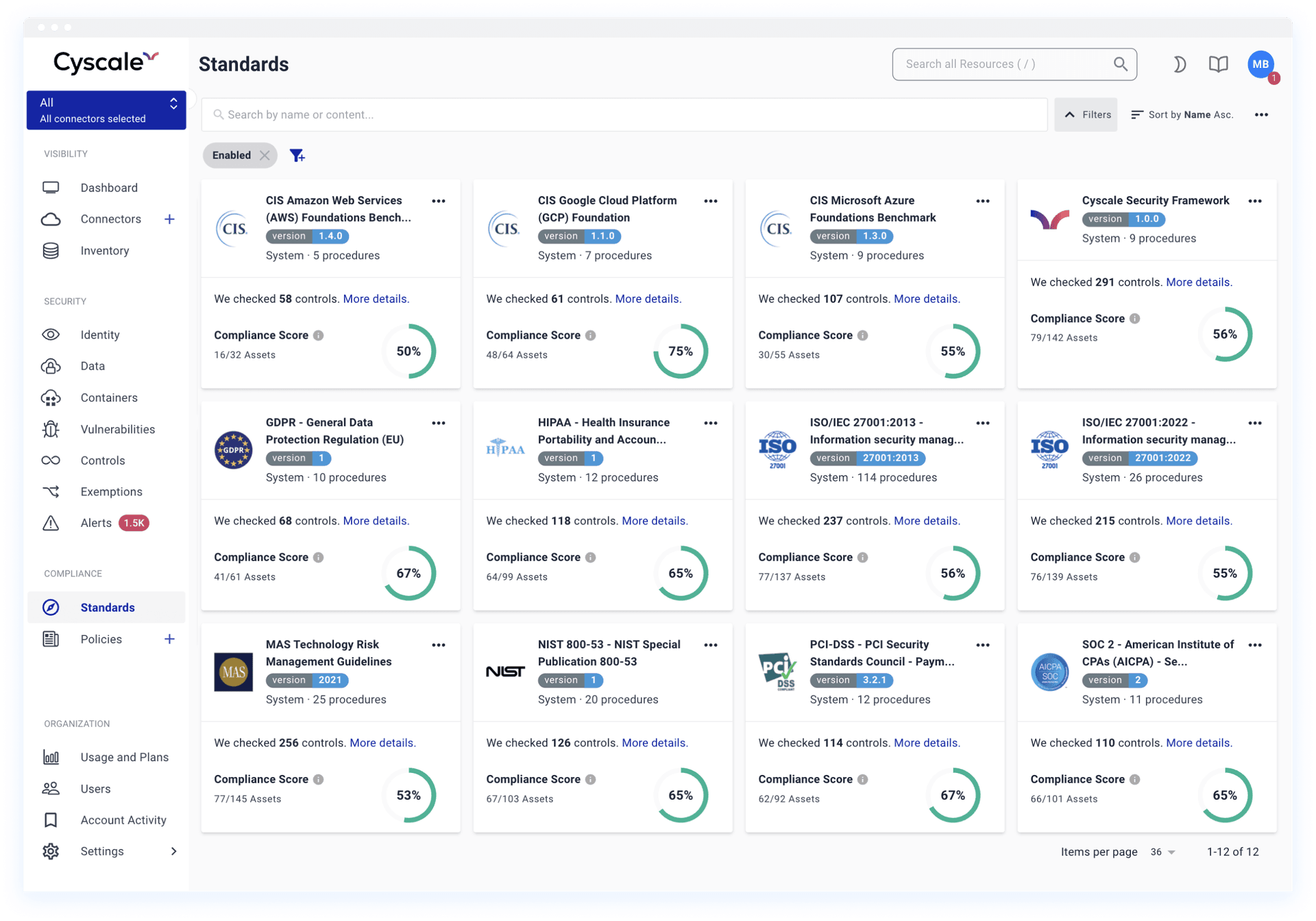
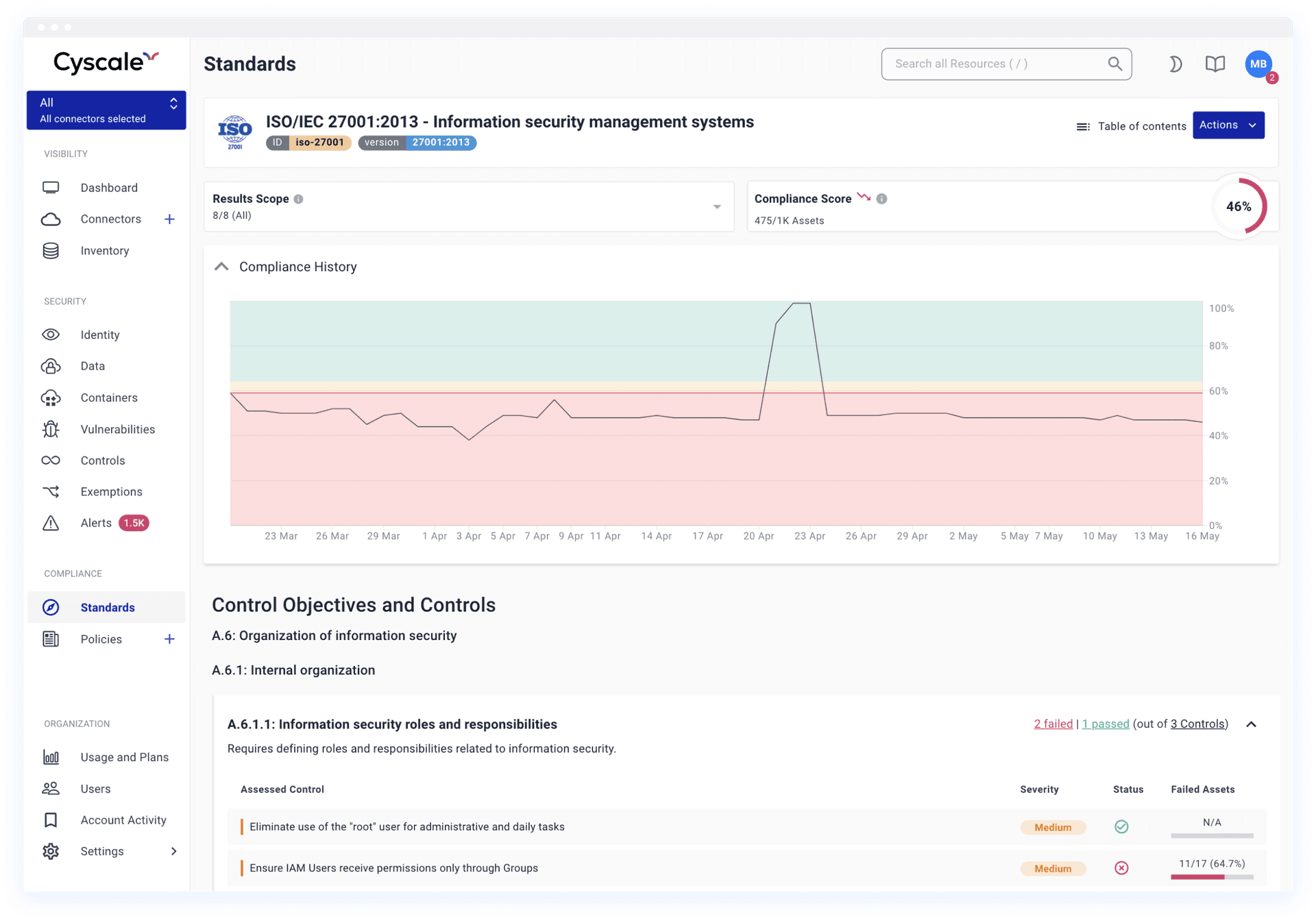
In-app security standards and organizational security policy templates for CIS Cloud Benchmarks, ISO 27001, SOC 2, GDPR, HIPAA, PCI DSS, NIST, and many more help your team with internal or external audits.
Automated and continuous assessment of your cloud compliance, with custom Controls that tap into our Security Knowledge Graph to deliver the security and compliance checks that matter most to your organization.
Analyze cloud misconfigurations
Analyze misconfigurations against the most popular industry and regulatory frameworks, including a wide range of CIS control benchmarks, ISO 27001, and SOC 2.
Ensure security and compliance
Prove alignment with the highest industry standards, enforce policies consistently across cloud providers and scale compliance efforts without overhead.
400+ unique configuration controls
Unique and customizable controls, including authentication, data protection, logging and monitoring, network configurations, system integrity, and more.
Prioritize misconfiguration risk
Contextual prioritization and remediation through our Security Knowledge Graph, which surfaces crucial issues based on the correlation of insights from a deep understanding of all your interlinked assets.
Cloud misconfigurations are insecure settings in cloud services, identities, storage, networking, or Kubernetes resources that can expose data and increase breach risk.
CSPM continuously scans cloud configurations, detects policy violations, maps issues to compliance frameworks, and provides remediation guidance to reduce risk quickly.
Yes. Cyscale uses contextual analysis to prioritize misconfigurations based on real-world impact, exposure, and relationships between assets.
Need broader coverage beyond misconfiguration checks? Explore our CNAPP platform and dedicated cloud vulnerability management workflows.
RECOMMENDED ARTICLES
This guide helps CIOs, CISOs and security staff to understand the risk & dangers of data security breaches and the importance of a secure cloud storage infrastructure.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CSPM continuously identifies cloud misconfigurations and policy violations across AWS, Azure, and Google Cloud to reduce breach exposure and audit risk.
IaC scanning reviews Terraform, CloudFormation, Kubernetes manifests, and similar files for insecure defaults before infrastructure reaches production.
Cloud compliance programs work best when technical controls, evidence collection, and remediation ownership are continuous rather than audit-driven.
Multi-cloud security requires consistent detection and remediation workflows across providers, not separate tooling islands by cloud.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited