What does Cyscale CNAPP cover?
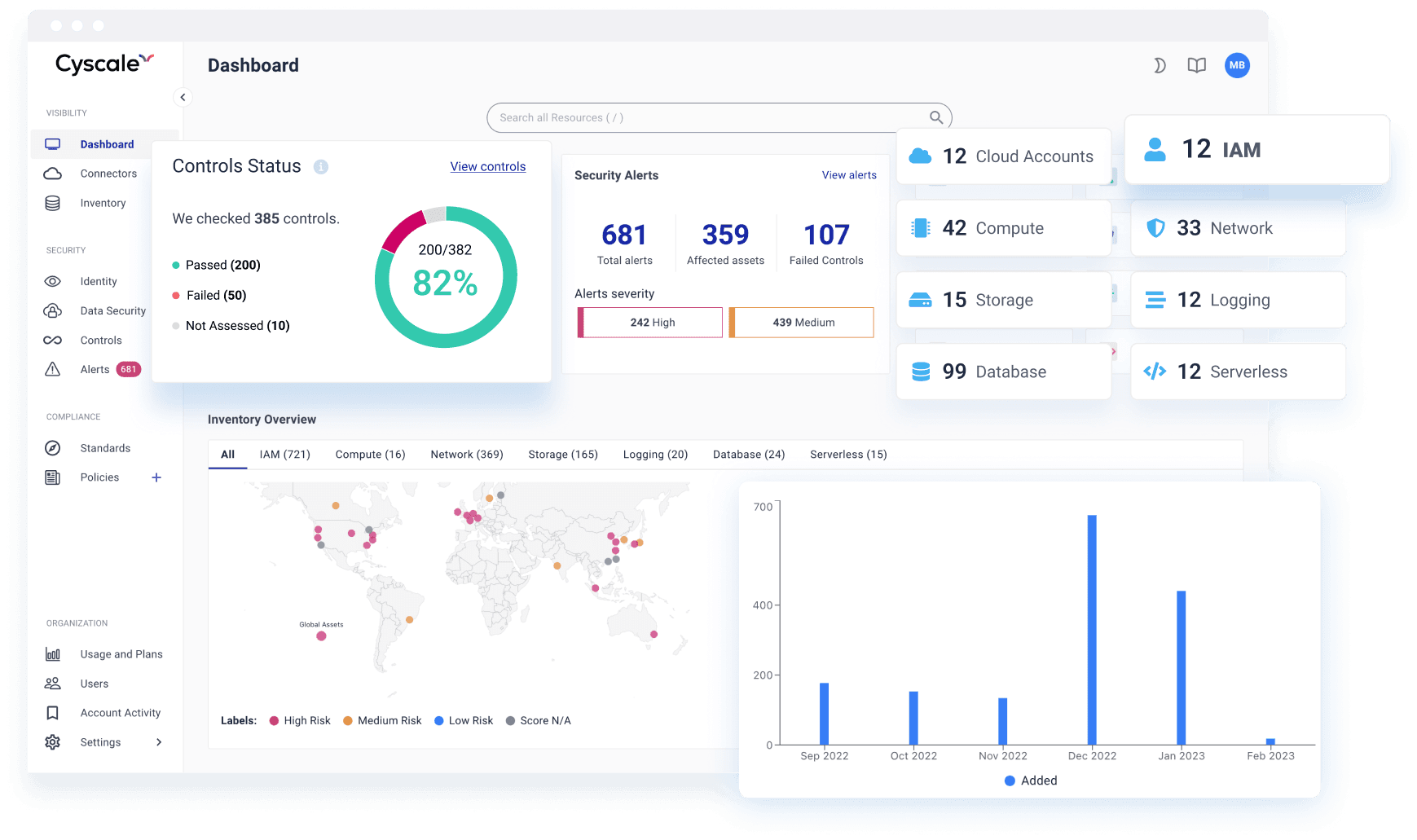
Cyscale CNAPP unifies posture, vulnerabilities, identities, workload risk, and compliance workflows across cloud accounts and runtime environments from one platform.
CNAPP PLATFORM
Cyscale gives Security, Engineering, and Cloud teams one shared operating model to detect, prioritize, and remediate risks that actually reduce attack surface.
Leading CNAPP teams replace scattered tooling with one platform that can prioritize real risk and drive fixes quickly. Cyscale brings together posture, identity, vulnerability, and compliance in a single actionable workflow.
Unify findings from code, cloud, identities, workloads, and compliance into one prioritized queue with clear ownership.
Focus on what is exposed and exploitable, not raw finding counts. Surface attack paths that have real business impact.
Connect cloud accounts through secure, read-only integrations and start triage with an immediate baseline of posture and risk.
A modern CNAPP is expected to do more than aggregate posture and workload findings. It should also help teams understand where code and dependency risk reaches live services so remediation starts with the most meaningful issues.
Continuously detect posture drift and misconfigurations across AWS, Azure, Google Cloud, and Alibaba Cloud.
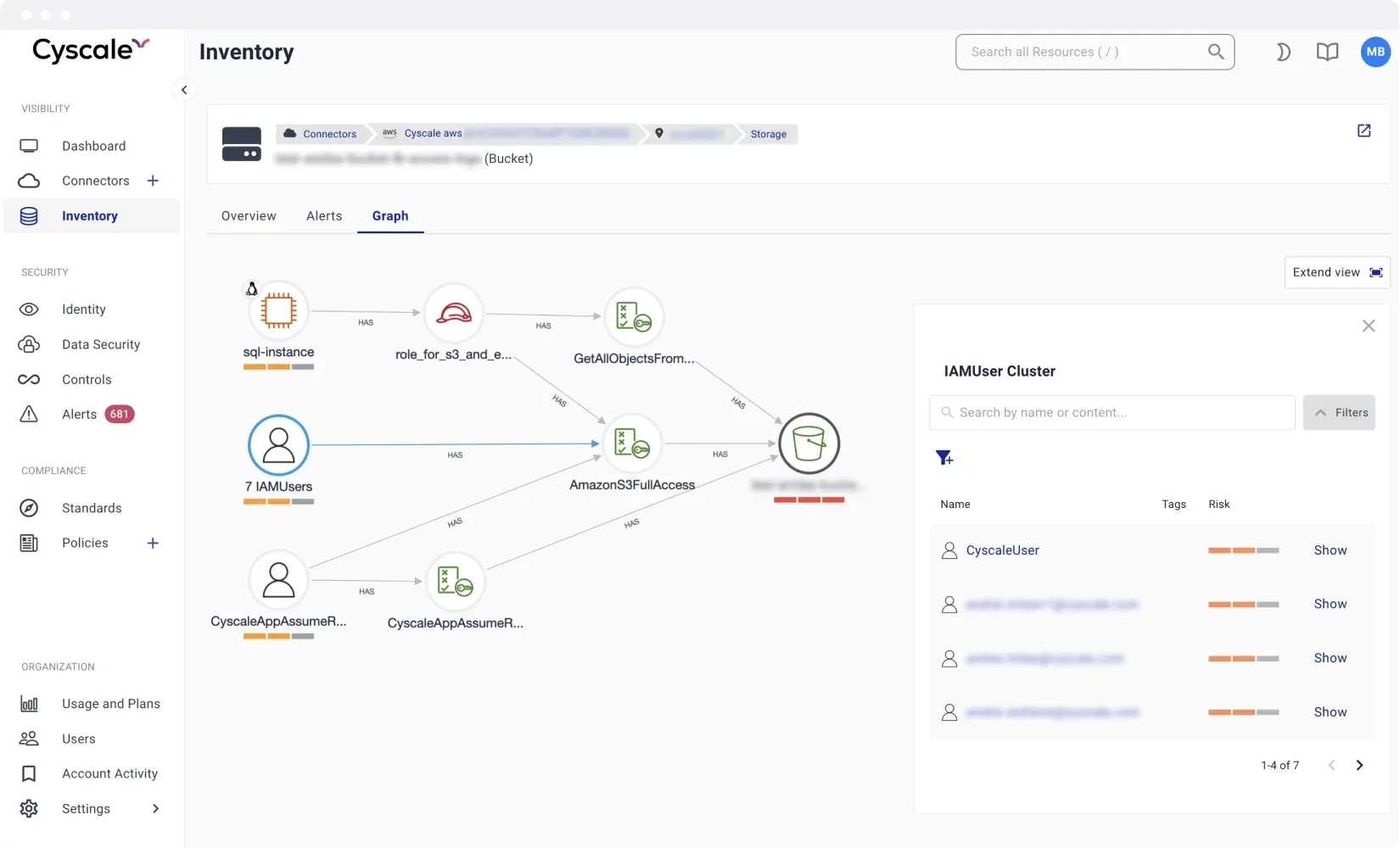
Correlate vulnerabilities, identities, and exposures to surface attack paths that materially increase risk.
Map findings to frameworks like ISO 27001, SOC 2, PCI DSS, and NIST with ongoing evidence collection.
Identify exposed data stores and toxic risk combinations that put sensitive cloud data at risk.
Understand effective permissions, excessive access, and identity risk across multi-cloud environments.
Scan and prioritize workload risks across VMs, container images, Kubernetes, and cloud functions.
Track container exposure and vulnerabilities in context with runtime configuration and access paths.
Inventory clusters and continuously assess control gaps, workload risk, and security drift.
Cyscale helps teams move from fragmented findings to coordinated remediation. Every issue is analyzed with context so you can understand exposure, likely impact, and the fastest remediation path.
Cyscale CNAPP unifies posture, vulnerabilities, identities, workload risk, and compliance workflows across cloud accounts and runtime environments from one platform.
Point tools create siloed alerts and duplicated work. Cyscale correlates findings across domains and presents one prioritized queue so teams fix what truly reduces attack surface.
Yes. Cyscale prioritizes based on exposure, exploitability, identity reachability, and business context, helping teams focus on high-impact attack paths first.
Yes. Cyscale uses an agentless onboarding model so teams can connect cloud accounts quickly and start with immediate visibility, without adding runtime overhead.
Yes. Cyscale provides actionable remediation context and ownership-ready workflows so security, platform, and engineering teams can resolve risks without tool switching.
CNAPP Buyer Guide
Strong CNAPP programs are measured by remediation throughput, cross-team usability, and risk-reduction reporting quality. The platform should help security, engineering, and leadership make faster, better decisions from the same data model.
SAST Wiki Guide
Bring secure code analysis into a broader code-to-cloud risk model.
SCA Wiki Guide
Use SBOM and dependency context to prioritize real software risk.
CNAPP Wiki Guide
Detailed framework for selecting and operationalizing a CNAPP platform.
CSPM Wiki Guide
How posture management should integrate into CNAPP workflows.
Cloud Vulnerability Management Wiki Guide
How to run contextual vulnerability programs at cloud speed.
Secret Scanning Wiki Guide
Understand how exposed credentials change application and cloud risk fast.
Cyscale vs Wiz
Comparison for teams evaluating enterprise CNAPP alternatives.
Start seeing measurable risk reduction in weeks, not quarters
GET A DEMORECOMMENDED ARTICLES
This guide helps security teams understand cloud storage misconfiguration risk and design practical remediation workflows.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CNAPP combines cloud posture, vulnerability management, identity context, and compliance workflows into one operating model so teams can fix risk faster.
SAST analyzes source code, bytecode, or compiled artifacts before deployment so teams can catch insecure coding patterns earlier in the delivery pipeline.
SCA identifies vulnerable and risky open-source packages, transitive dependencies, license issues, and outdated components across modern software delivery pipelines.
Secret scanning detects exposed credentials, API keys, tokens, and certificates before they become an entry point into cloud or application environments.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited