Cloud Security Expert Insights and Tips

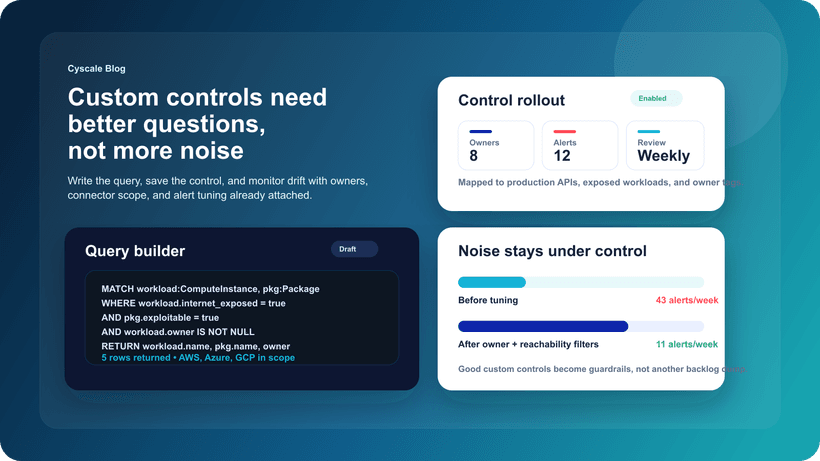
Better Control Remediation Guidance in Cyscale
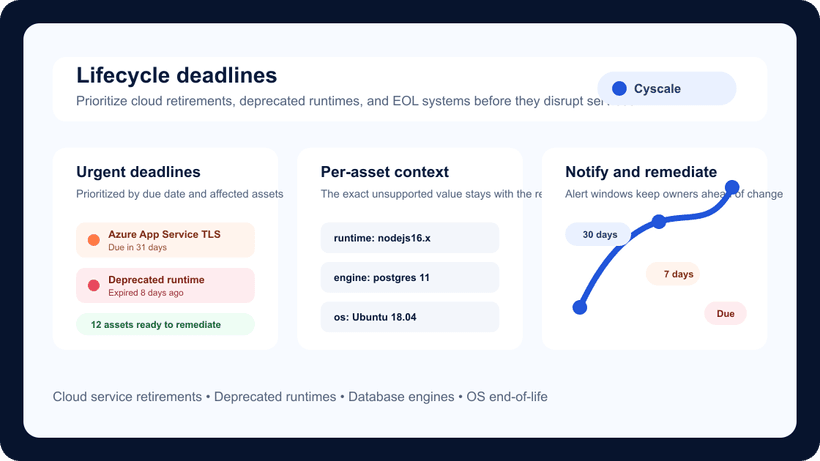
Lifecycle Deadlines Help Teams Prevent Cloud Service Disruptions
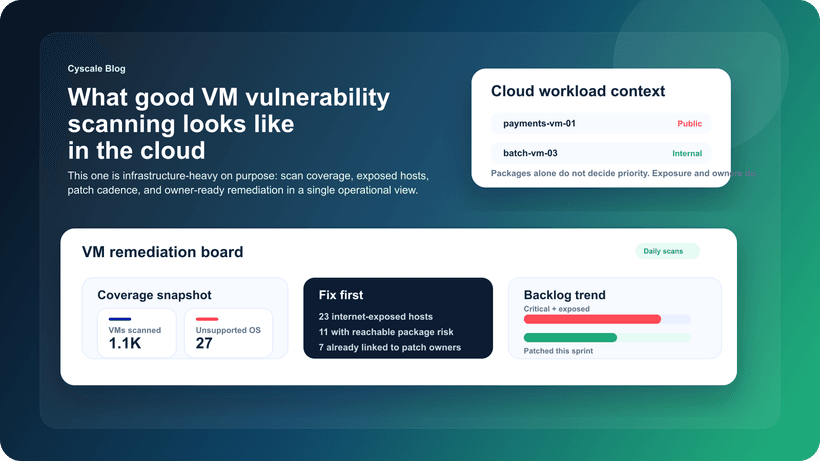
What Good VM Vulnerability Scanning Looks Like in Cloud Environments
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CNAPP combines cloud posture, vulnerability management, identity context, and compliance workflows into one operating model so teams can fix risk faster.
CSPM continuously identifies cloud misconfigurations and policy violations across AWS, Azure, and Google Cloud to reduce breach exposure and audit risk.
SCA identifies vulnerable and risky open-source packages, transitive dependencies, license issues, and outdated components across modern software delivery pipelines.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited