Cloud Identity - Expert Insights, Best Practices & Tips
AWS Resource Control Policies (RCPs): Everything You Need To Get Started
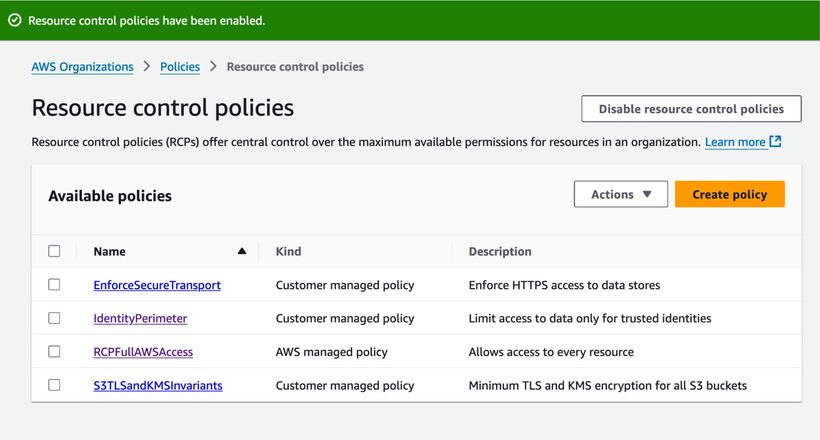
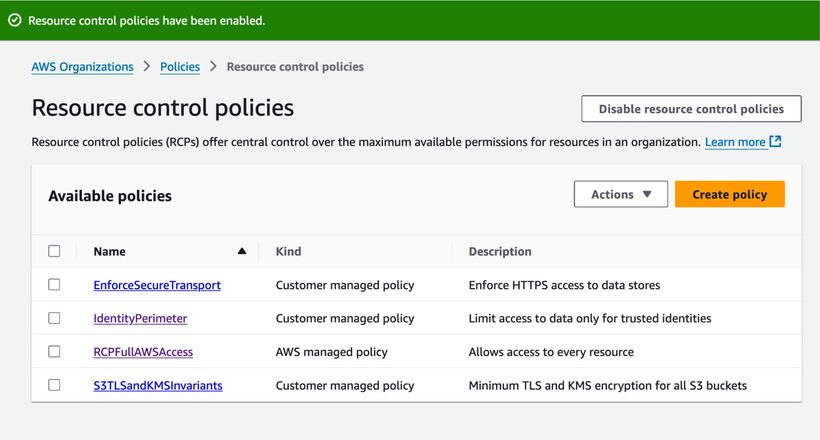
AWS Resource Control Policies (RCPs): Everything You Need To Get Started
Guest Users Label Helps Teams Reduce External Identity Risk in Multi-Cloud
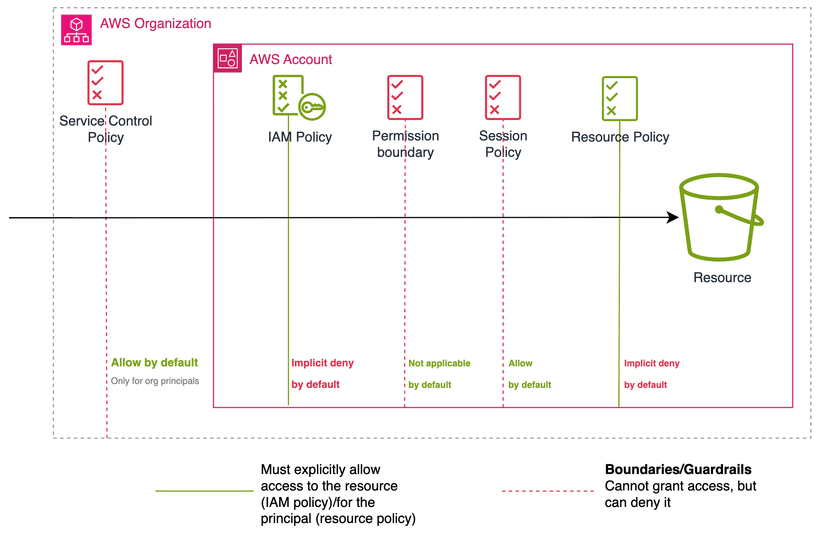
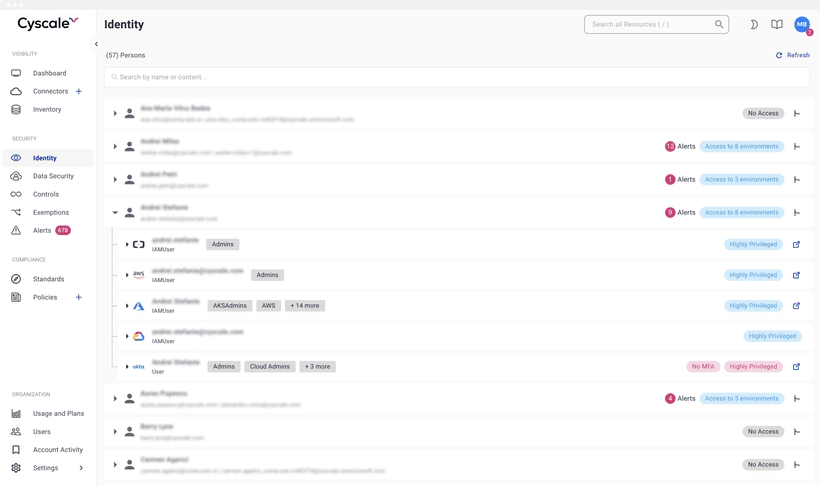
AWS IAM: A Comprehensive Guide Toward Least Privilege
What are Non-Human Identities (NHIs), and how do we secure them?