All you need to know about protecting SaaS apps and data in the cloud
NewsWednesday, May 10, 2023
Secure Your Cloud Stack Now with our New Data Security E-book!

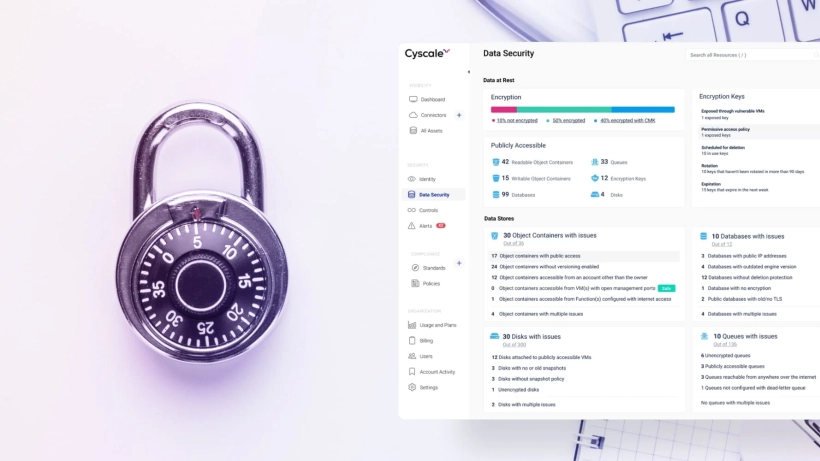
ProductMonday, March 20, 2023
How to Prevent Alert Fatigue: Announcing the New Alert Features


Cloud Native SecurityTuesday, February 21, 2023
CNAPP: The Key to Cloud-Native Applications Security

NewsThursday, January 26, 2023
Announcing the New Whitepaper: The In-Depth Guide to Cloud Compliance in 2023