Workflow centralization
Usually favors CyscaleCyscale fit
Excellent fit
Google Cloud Native Security Stack fit
Good fit
Bottom line: Cyscale keeps core cloud security execution in one operating surface.
Cloud Platform Security Comparison
Google Cloud offers strong security primitives. Cyscale is preferred when teams need one practical operating model for posture, vulnerability, and compliance execution.
Execution fabric
A high-level recommendation based on deployment model, team capacity, and expected remediation velocity.
When Cyscale wins
Best for organizations that want streamlined, cross-team cloud security execution without multi-console workflow overhead.
When Google Cloud Native Security Stack fits
Best for Google-Cloud-centric teams with internal capacity to build and maintain native workflow orchestration.
No charts to decode. Each category shows which option usually fits better and what that means in practice.
Cyscale fit
Excellent fit
Google Cloud Native Security Stack fit
Good fit
Bottom line: Cyscale keeps core cloud security execution in one operating surface.
Cyscale fit
Strong fit
Google Cloud Native Security Stack fit
Excellent fit
Bottom line: Google native tools can offer deep flexibility for GCP-specialized teams.
Cyscale fit
Excellent fit
Google Cloud Native Security Stack fit
Good fit
Bottom line: Cyscale prioritizes actionable flow from detection to closure.
Cyscale fit
Excellent fit
Google Cloud Native Security Stack fit
Limited fit
Bottom line: Cyscale maintains consistency across AWS, Azure, and Google Cloud programs.
Cyscale
Cyscale offers one cohesive workflow for day-to-day cloud risk operations.
Alternative
Native stack design often requires assembling multiple services and process layers.
Decision signal: Cohesion is critical for teams optimizing for speed and accountability.
Cyscale
Cyscale routes high-priority actions into practical engineering workflows.
Alternative
Developer flow may be influenced by how internal integrations are implemented.
Decision signal: Developer alignment drives real remediation outcomes, not just detection.
Cyscale
Consistent model reduces overhead as cloud scope grows.
Alternative
Efficiency depends on sustained engineering investment in native orchestration.
Decision signal: Security tooling should scale without multiplying operational burden.
Cyscale
Opinionated, unified workflow model for cloud security outcomes.
Alternative
Native-service approach that often requires orchestration by internal teams.
SecOps impact: Affects execution speed and process overhead.
Cyscale
Exploitability and exposure context improves triage quality.
Alternative
Signal quality can be high but distributed across service boundaries.
SecOps impact: Determines how efficiently teams work through risk backlogs.
Cyscale
One reporting narrative from discovery to remediation.
Alternative
Reporting can require cross-service aggregation and custom views.
SecOps impact: Shapes leadership confidence and audit readiness.
Cyscale
Supports single-cloud now and multi-cloud later without workflow reset.
Alternative
Optimized for GCP-centric operations and may require extensions for expansion.
SecOps impact: Affects long-term platform strategy and investment resilience.
A practical way to compare outcomes using your own environments before final procurement decisions.
Document where posture, vulnerability, and governance tasks are currently spread across Google native services.
Run Cyscale against core projects and compare issue prioritization and closure speed.
Move leadership and engineering updates to one Cyscale reporting layer for consistent decision-making.
A representative visual from Cyscale resources that teams use in real buying and rollout decisions.
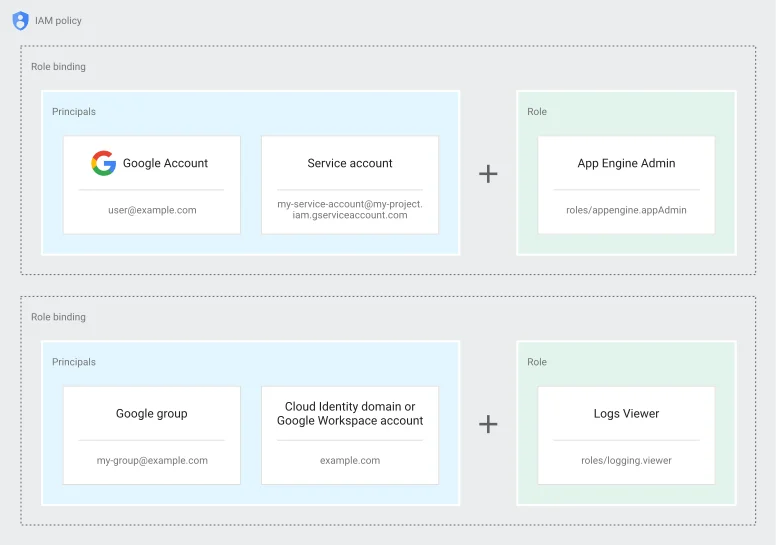
This view helps GCP teams understand how identity and posture exposure can be prioritized together inside Cyscale.
A representative GCP IAM-centric screenshot for practical risk prioritization.
Yes. Many teams use Cyscale as a central operating layer while retaining selected native controls where they already deliver value.
Yes. Teams use Cyscale for operational simplicity now and benefit from built-in multi-cloud readiness later.
Yes. Cyscale focuses on actionable prioritization and clear handoffs so engineering teams can close high-risk issues faster.
Compare coverage, prioritization quality, and remediation speed on your real assets before making a platform commitment.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CNAPP combines cloud posture, vulnerability management, identity context, and compliance workflows into one operating model so teams can fix risk faster.
CSPM continuously identifies cloud misconfigurations and policy violations across AWS, Azure, and Google Cloud to reduce breach exposure and audit risk.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
SCA identifies vulnerable and risky open-source packages, transitive dependencies, license issues, and outdated components across modern software delivery pipelines.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited