Primary domain focus
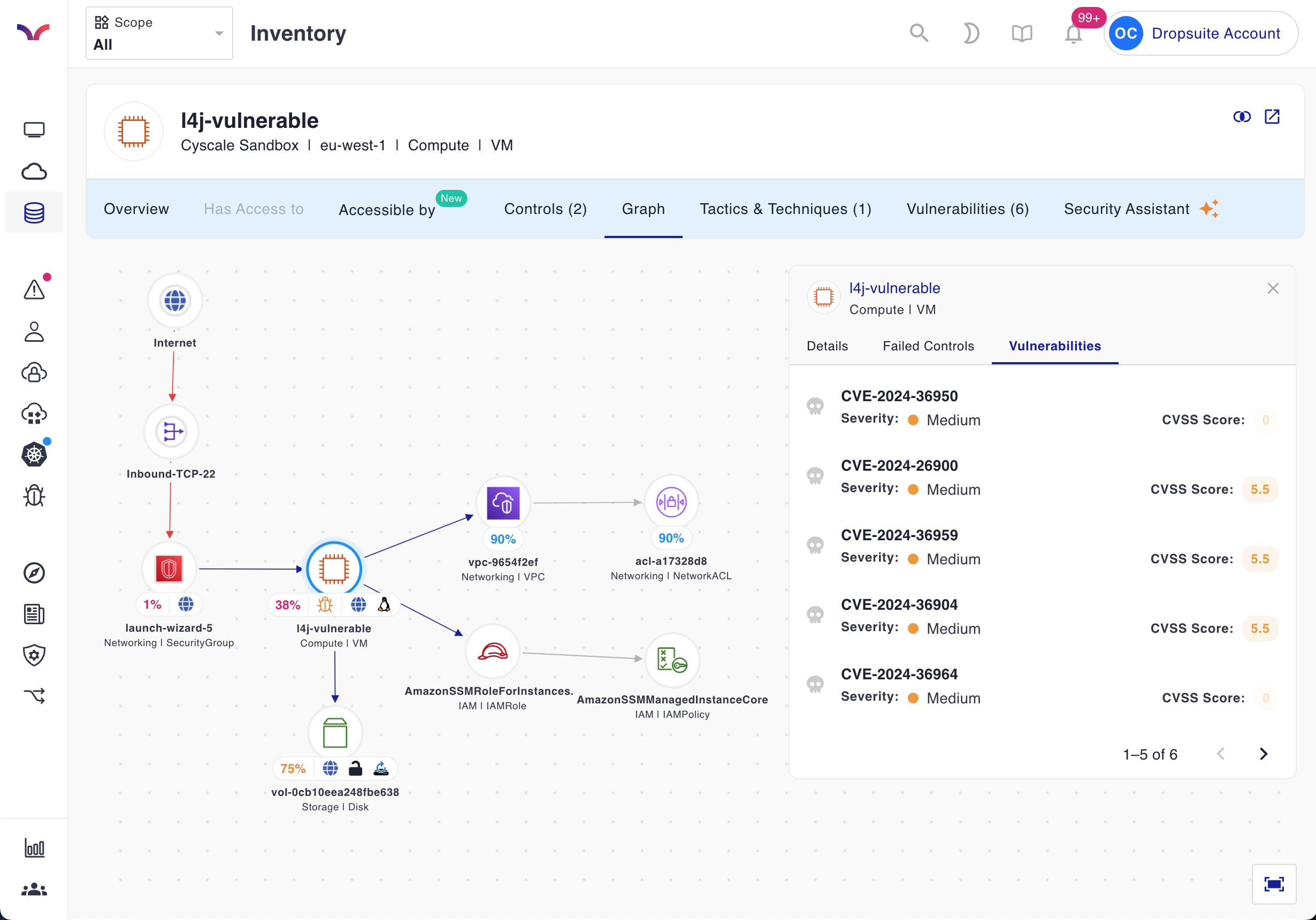
Cyscale
Cloud-native CNAPP, CSPM, and vulnerability management workflows.
Alternative
Broad portfolio focused on edge, access, and zero-trust architecture.
Operational impact
Whether cloud remediation is the center of operations.