Payment API exposure
Internet-facing services, weak auth flows, and leaked credentials increase fraud and account-takeover risk.
CLOUD SECURITY FOR FINANCIAL TECHNOLOGY
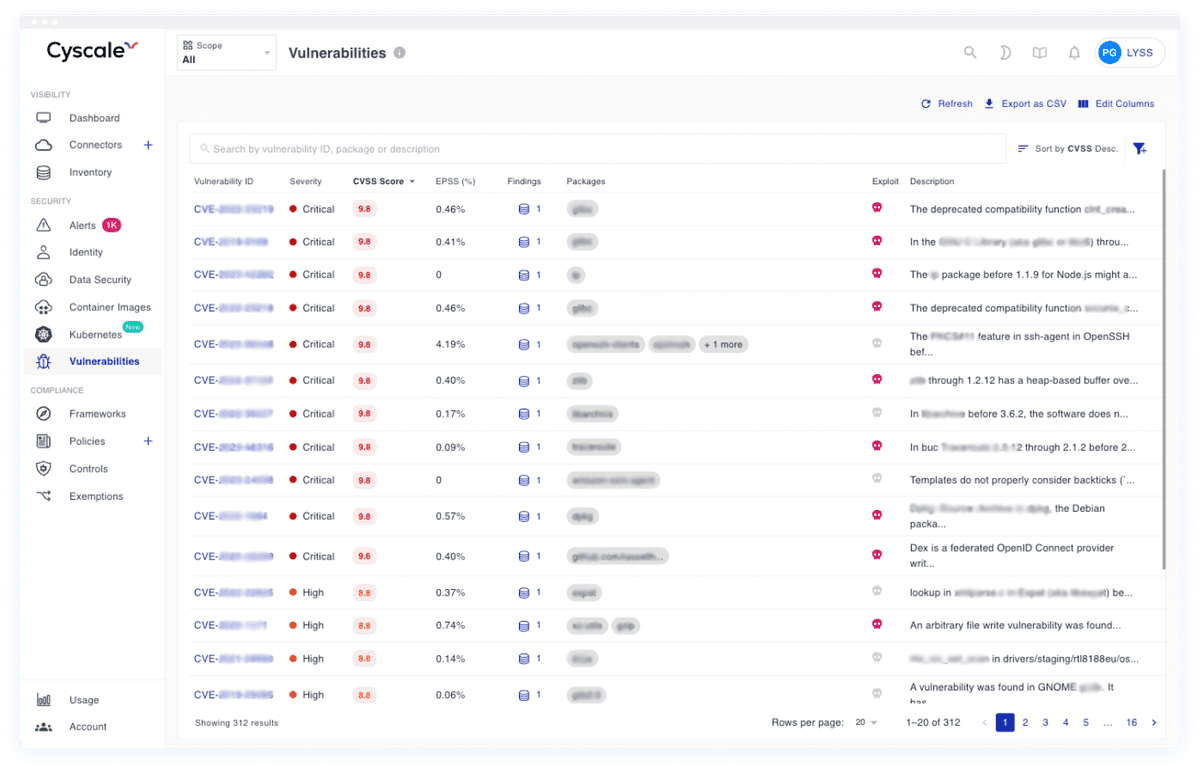
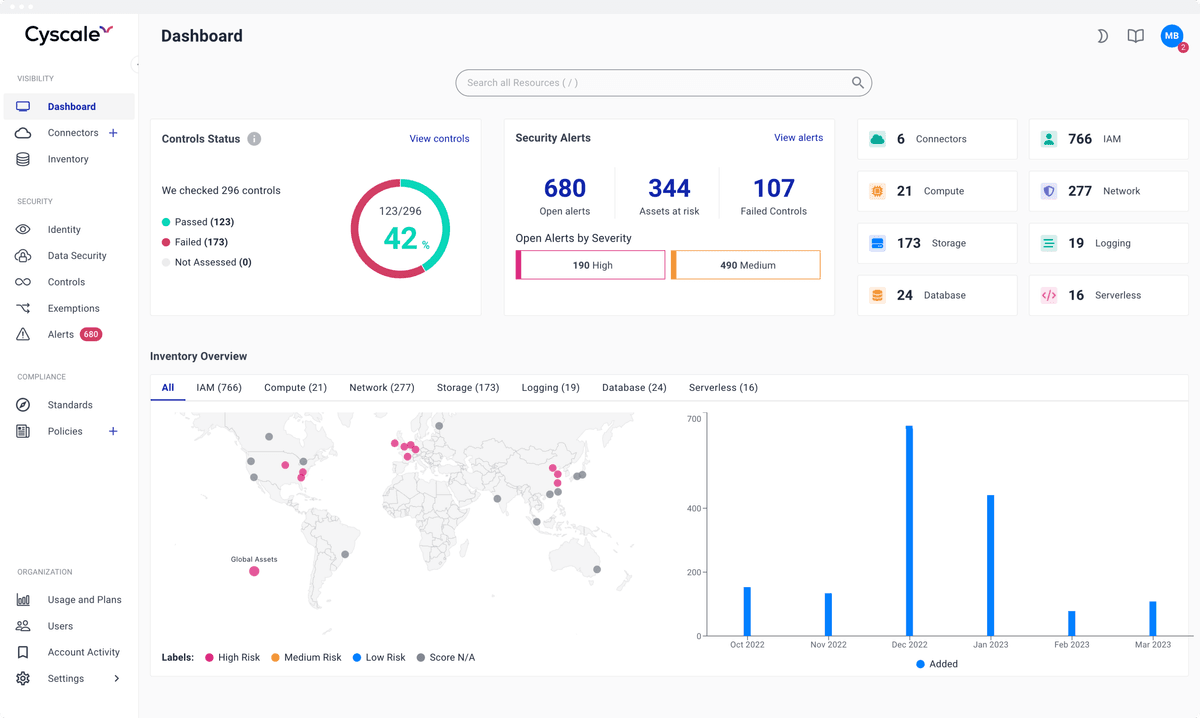
Secure payment workloads, customer financial data, and cloud-native fintech applications with contextual CNAPP, CSPM, and SBOM-based vulnerability scanning.
Stop guessing which findings matter. Prioritize cloud, identity, and software risks that can impact payments, account data, and transaction availability.
< 15 min
to map cloud attack surface
1 platform
for posture plus vulnerability workflows
Continuous
evidence for remediation and audit tracking
Internet-facing services, weak auth flows, and leaked credentials increase fraud and account-takeover risk.
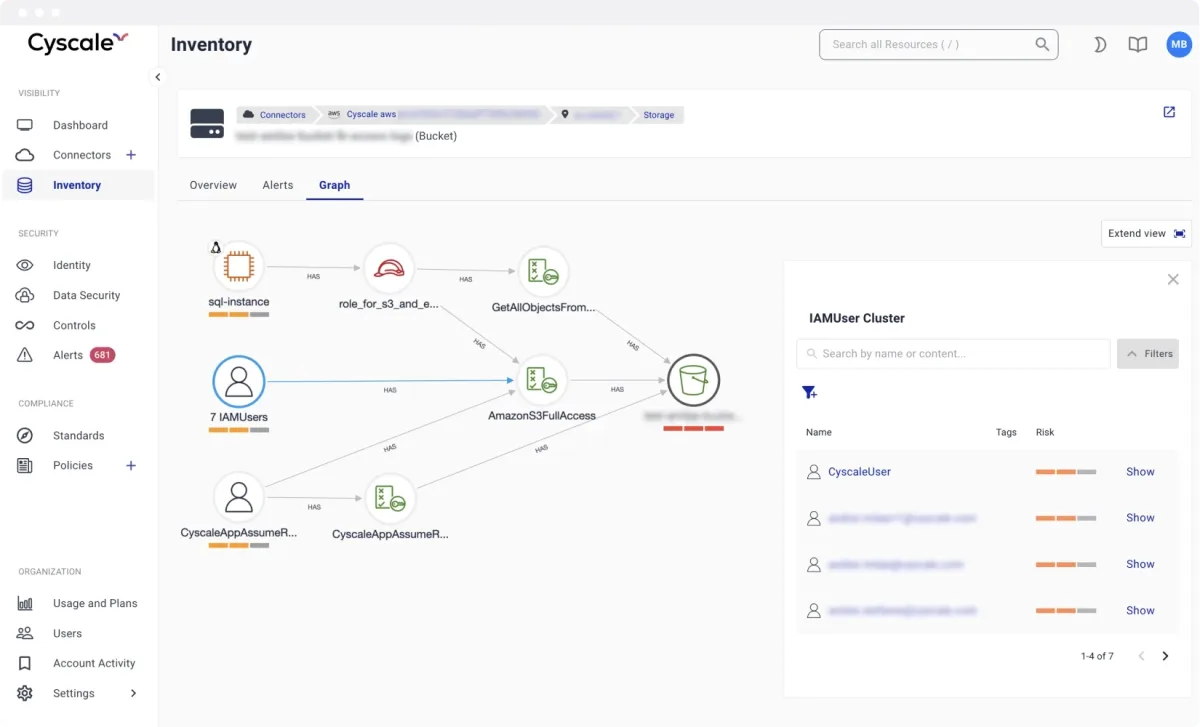
Over-privileged roles and trust chains create lateral movement paths into high-value financial assets.
Fast shipping requires SBOM-backed software controls without slowing product and platform engineering.
Security leaders need continuous evidence, not manual spreadsheet collection before each audit cycle.
Modeled after high-performing cloud security programs, these are the workflows teams execute continuously to keep risk under control.
Detect risky exposure on internet-facing services, secrets, and over-privileged identities used by payment and account APIs.
Scan code and build artifacts early, then connect findings to runtime cloud context so engineering can fix critical issues before release.
Track control coverage and remediation progress against common financial compliance expectations across cloud environments.
Cyscale Platform extends beyond posture checks and covers the software and workload security chain end to end.
Map cloud findings to the frameworks your teams and customers care about. Cyscale helps security and compliance teams track status continuously instead of preparing only for periodic audits.
They trust Cyscale to protect payment flows and financial data, secure cloud infrastructure, and remediate vulnerabilities before they impact customers.

OpenPayd

Swan

Sikoia

Fyorin
Cyscale correlates vulnerability and posture findings with cloud exposure, identities, and asset criticality so teams can fix issues with the highest financial and operational impact first.
Yes. Cyscale maps technical findings to common frameworks and keeps remediation evidence available for internal and external audit preparation.
Start with contextual CNAPP visibility and SBOM-driven vulnerability scanning.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CNAPP combines cloud posture, vulnerability management, identity context, and compliance workflows into one operating model so teams can fix risk faster.
CSPM continuously identifies cloud misconfigurations and policy violations across AWS, Azure, and Google Cloud to reduce breach exposure and audit risk.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
Cloud compliance programs work best when technical controls, evidence collection, and remediation ownership are continuous rather than audit-driven.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited