Patient-data confidentiality
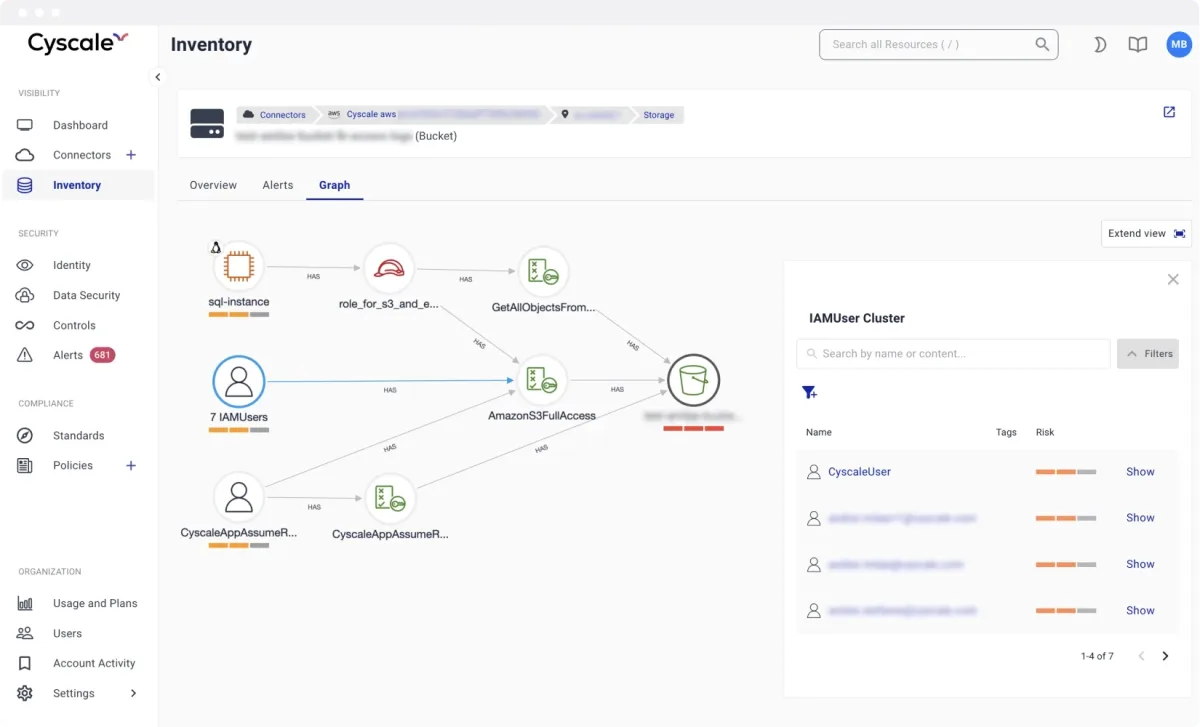
Storage exposure, weak key posture, and broad access policies can put protected data at risk.
CLOUD SECURITY FOR HEALTHCARE TECHNOLOGY
Protect healthcare data workloads with contextual cloud posture management, SBOM-based vulnerability scanning, and continuous compliance visibility.
Protect PHI workflows and cloud-native clinical platforms with contextual prioritization across posture drift, identity risk, and software vulnerabilities.
< 15 min
to map cloud attack surface
1 platform
for posture plus vulnerability workflows
Continuous
evidence for remediation and audit tracking
Storage exposure, weak key posture, and broad access policies can put protected data at risk.
Operational outages in cloud backends impact patient experience and care-delivery continuity.
Healthcare integrations multiply trust boundaries and increase chances of inherited cloud misconfiguration.
Procurement and compliance teams expect clear proof of continuous control operation.
Modeled after high-performing cloud security programs, these are the workflows teams execute continuously to keep risk under control.
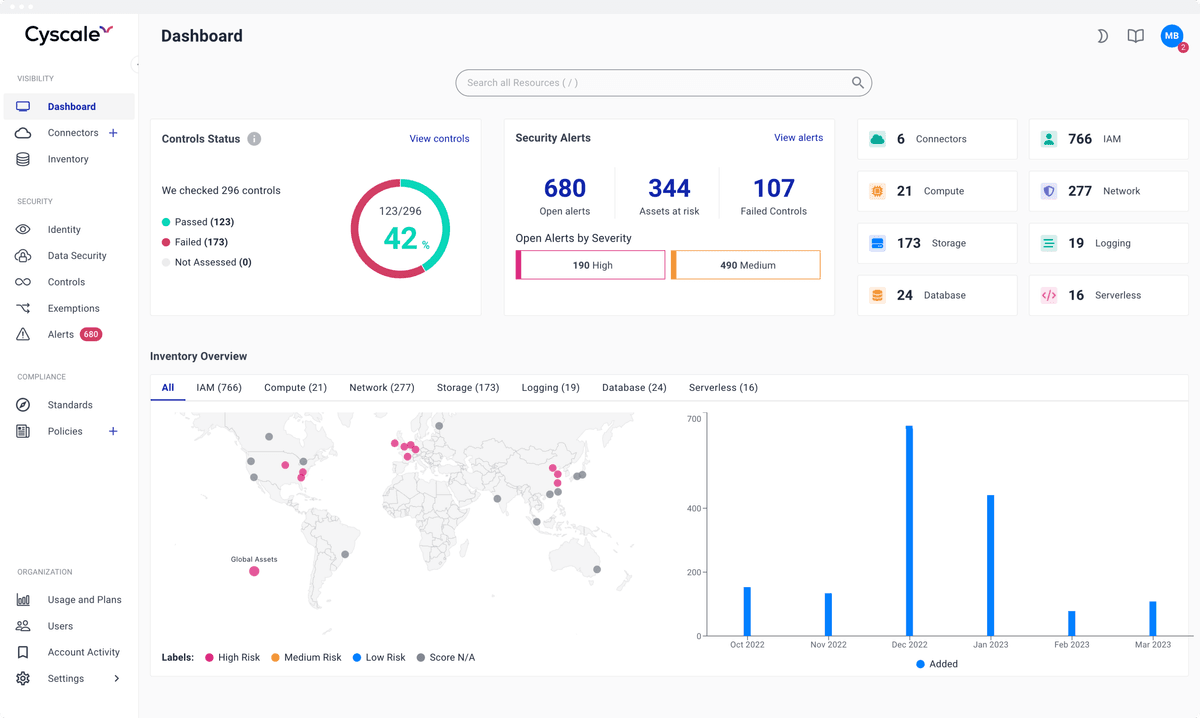
Continuously detect misconfigurations, weak encryption posture, and identity risks around systems handling protected health information.
Monitor cloud-native services, Kubernetes workloads, and serverless functions that power patient portals and internal healthcare apps.
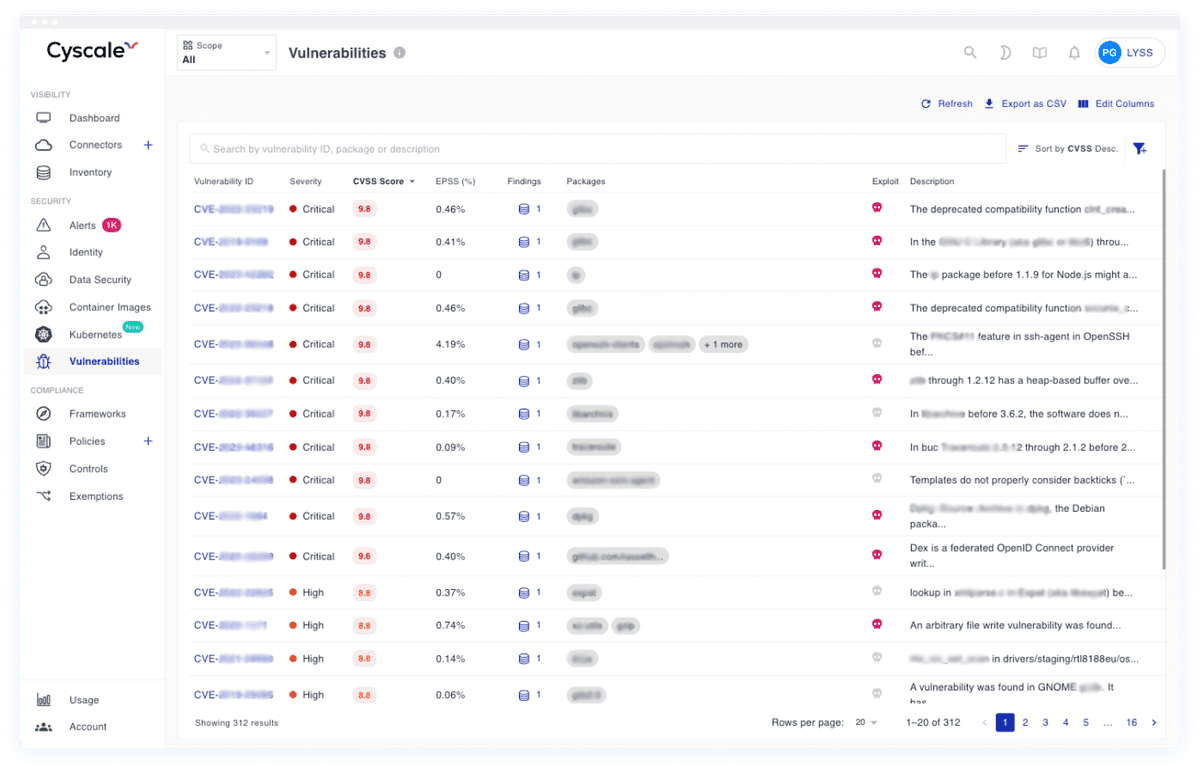
Use SBOM-based scanning and code security checks to reduce vulnerable dependencies and insecure code patterns before deployment.
Cyscale Platform extends beyond posture checks and covers the software and workload security chain end to end.
Map cloud findings to the frameworks your teams and customers care about. Cyscale helps security and compliance teams track status continuously instead of preparing only for periodic audits.
They trust Cyscale to protect patient data, secure clinical cloud systems, and fix vulnerabilities that can disrupt care operations.

PatchRx

Awell

Medefer

Lindus Health
Cyscale supports control mapping and continuous cloud monitoring that helps healthcare technology teams operationalize HIPAA-related security practices.
Yes. Cyscale covers cloud workloads, containerized services, code repositories, and serverless components used in modern HealthTech delivery pipelines.
Start with contextual CNAPP visibility and SBOM-driven vulnerability scanning.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CNAPP combines cloud posture, vulnerability management, identity context, and compliance workflows into one operating model so teams can fix risk faster.
CSPM continuously identifies cloud misconfigurations and policy violations across AWS, Azure, and Google Cloud to reduce breach exposure and audit risk.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
Cloud compliance programs work best when technical controls, evidence collection, and remediation ownership are continuous rather than audit-driven.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited