Unknown inherited cloud risk
Target environments often hide misconfigurations, identity drift, and vulnerable software that can alter deal risk.
CLOUD SECURITY FOR M&A AND ACQUISITION ASSESSMENTS
Assess the security and compliance posture of acquisition targets with contextual CNAPP visibility, SBOM-based vulnerability scanning, and evidence-ready reporting.
Assess acquisition-target cloud risk with clear evidence before close, then drive a focused post-close remediation and integration plan.
< 15 min
to map cloud attack surface
1 platform
for posture plus vulnerability workflows
Continuous
evidence for remediation and audit tracking
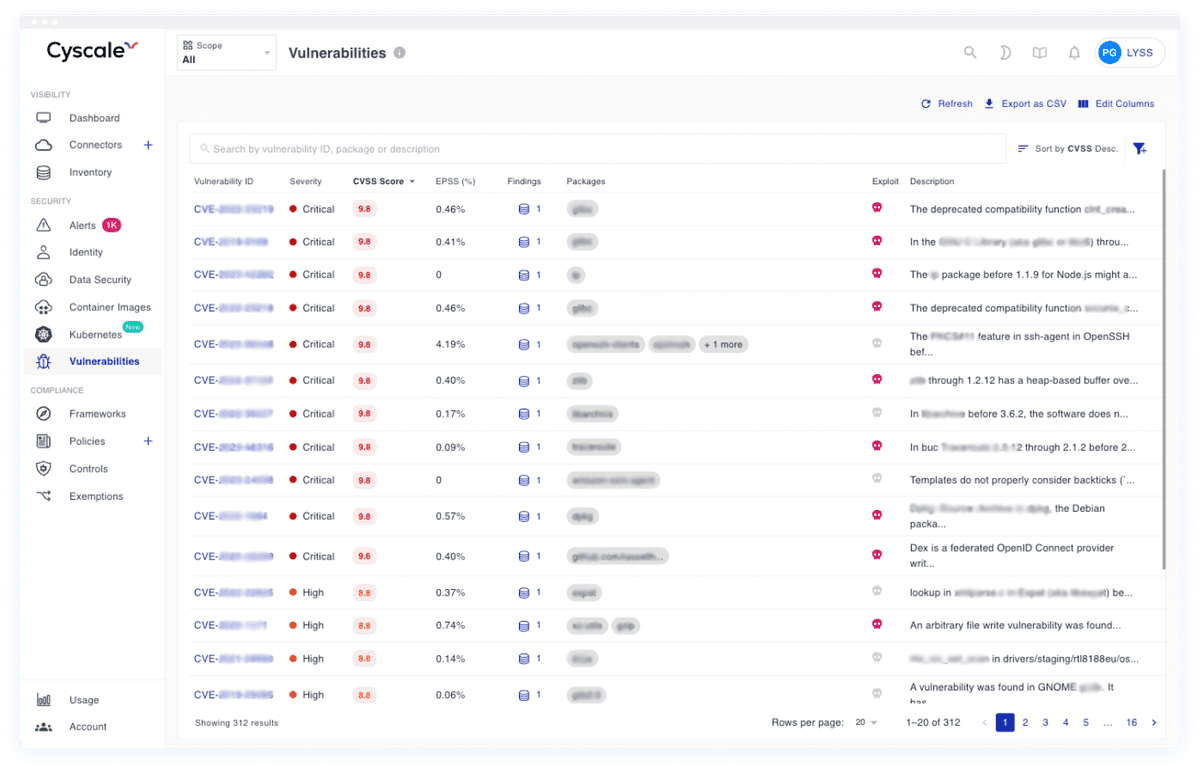
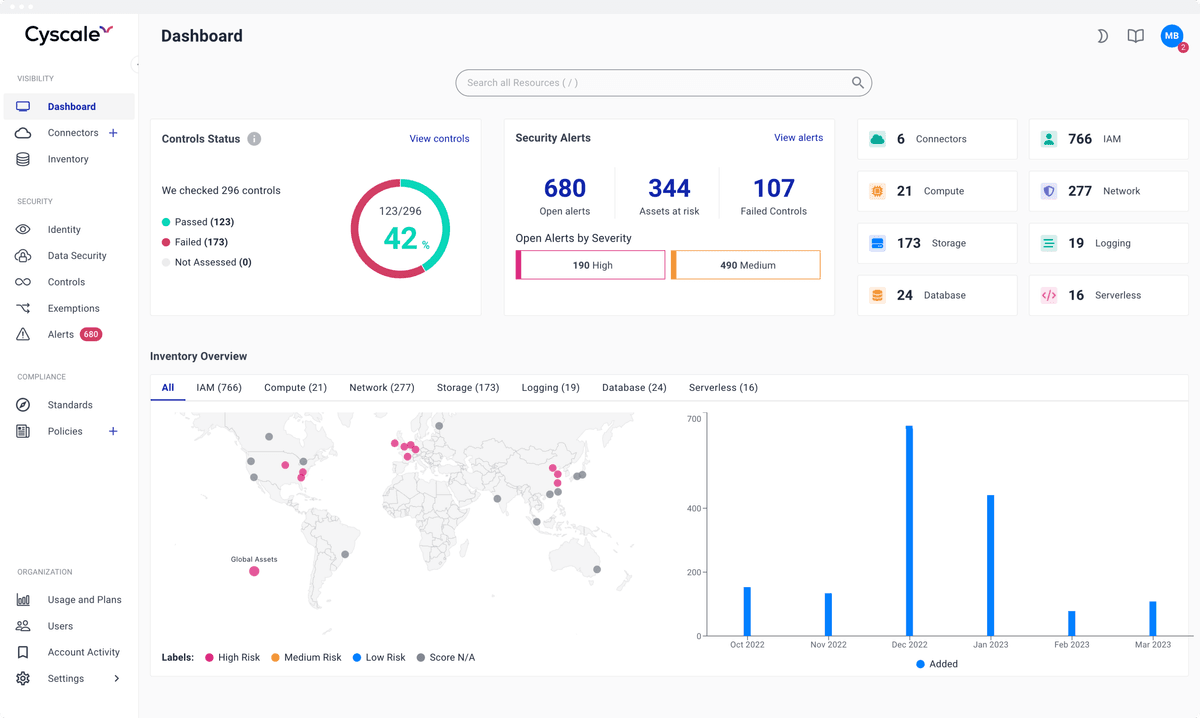
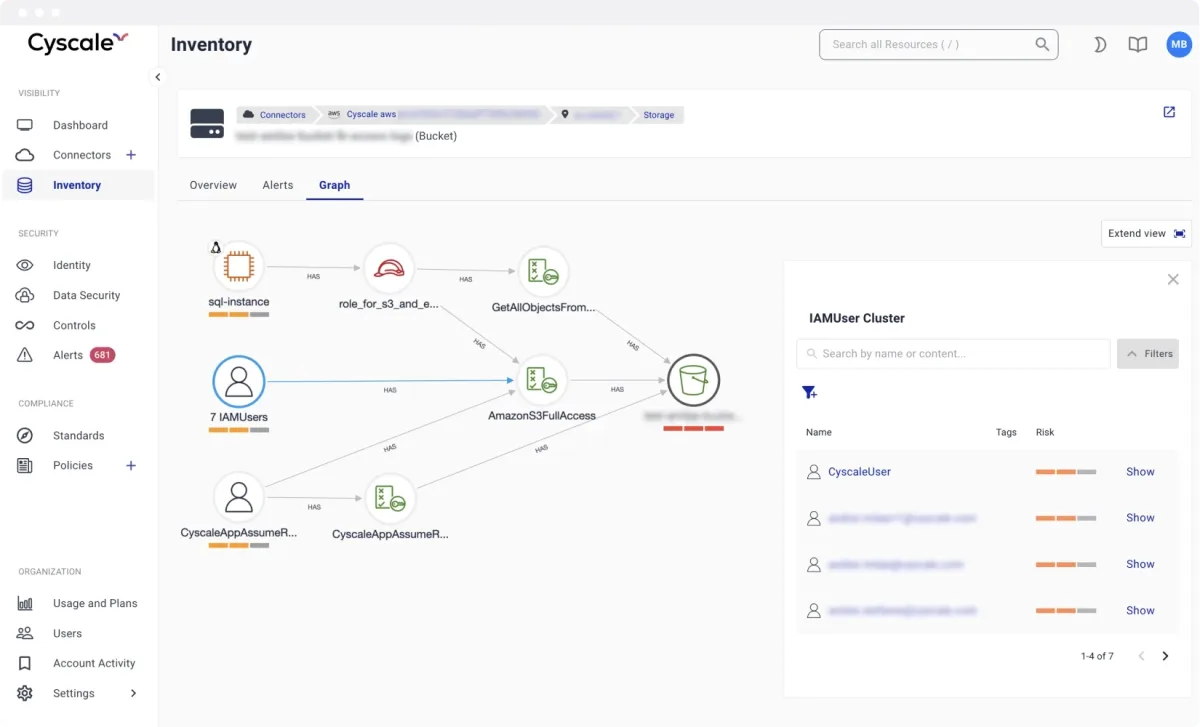
Map misconfigurations, identity risk, and exploitable software findings across the target cloud estate and engineering stack.
Review control maturity and remediation history tied to SOC 2, ISO 27001, PCI DSS, NIST, and buyer-specific requirements.
Prioritize post-close remediation by blast radius so security, platform, and leadership teams can execute a focused integration roadmap.
Modeled after high-performing cloud security programs, these are the workflows teams execute continuously to keep risk under control.
Target environments often hide misconfigurations, identity drift, and vulnerable software that can alter deal risk.
Buyers need evidence of real control operation, not static policy documents, before final investment decisions.
Security teams must produce a defensible view of target risk quickly without sacrificing technical depth.
High-risk findings need remediation sequencing that aligns with Day-1 operations and integration milestones.
Cyscale Platform extends beyond posture checks and covers the software and workload security chain end to end.
Map cloud findings to the frameworks your teams and customers care about. Cyscale helps security and compliance teams track status continuously instead of preparing only for periodic audits.
They trust Cyscale to assess target cloud risk, validate security posture for acquisitions, and prioritize remediation before and after close.

Midaxo

DealCircle

SourceScrub

4Degrees
Cyscale centralizes posture, identity, and vulnerability signals so teams can quickly assess inherited cloud risk and focus diligence effort on high-impact findings.
Yes. Findings are prioritized by exposure and blast radius, helping teams sequence remediation and integration actions after deal close.
Start with contextual CNAPP visibility and SBOM-driven vulnerability scanning.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CNAPP combines cloud posture, vulnerability management, identity context, and compliance workflows into one operating model so teams can fix risk faster.
CSPM continuously identifies cloud misconfigurations and policy violations across AWS, Azure, and Google Cloud to reduce breach exposure and audit risk.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
Cloud compliance programs work best when technical controls, evidence collection, and remediation ownership are continuous rather than audit-driven.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited