API and token abuse
Mobile ecosystems expose backend APIs, identity flows, and key material to constant adversarial testing.
CLOUD SECURITY FOR MOBILE APPLICATION BACKENDS
Secure mobile app backend infrastructure, APIs, and cloud-native delivery pipelines with SBOM-based scanning and contextual cloud risk prioritization.
Secure mobile app backends and release pipelines with code-to-runtime context that highlights what is truly exploitable in production.
< 15 min
to map cloud attack surface
1 platform
for posture plus vulnerability workflows
Continuous
evidence for remediation and audit tracking
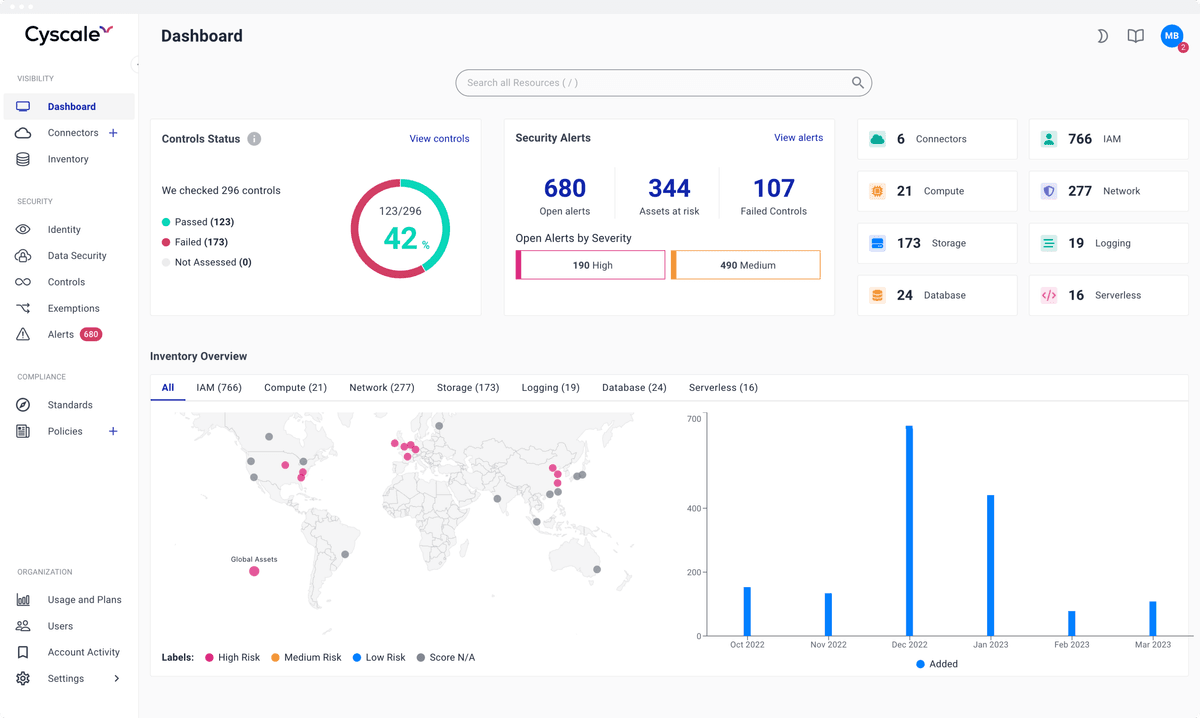
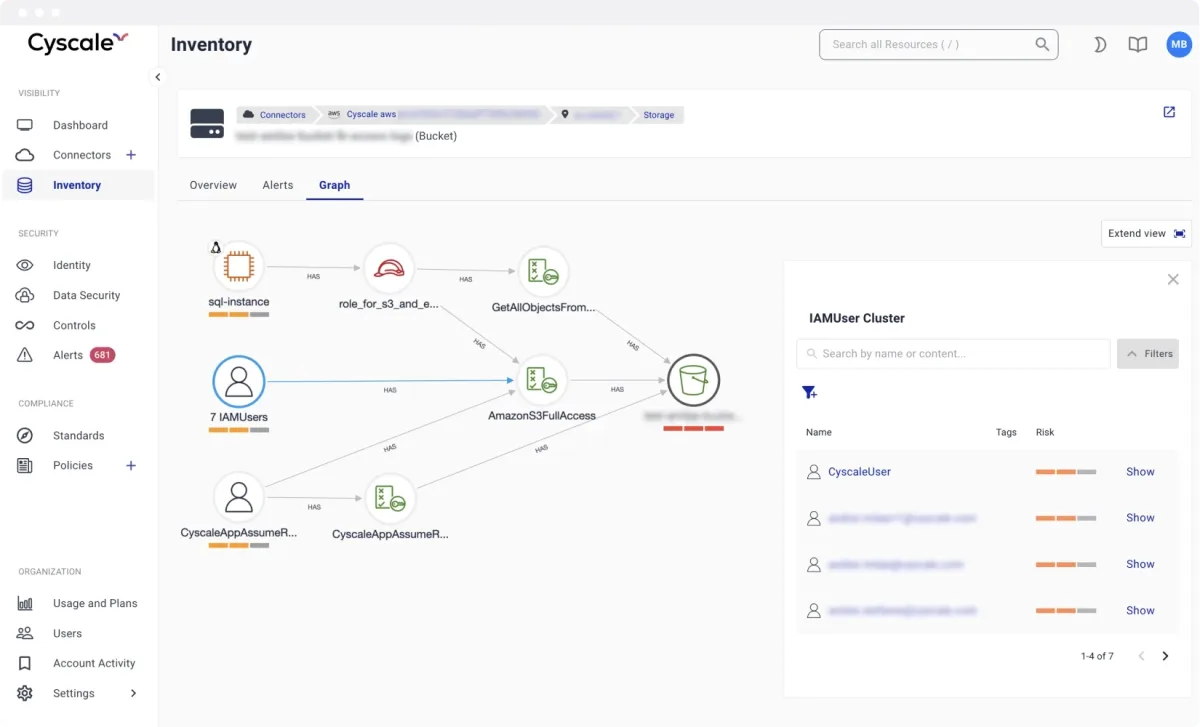
Identify risky exposures in identity flows, service-to-service communication, and cloud storage used by mobile applications.
Shift security earlier with SAST, SCA, IaC, and secret scanning, then validate runtime context after deployment.
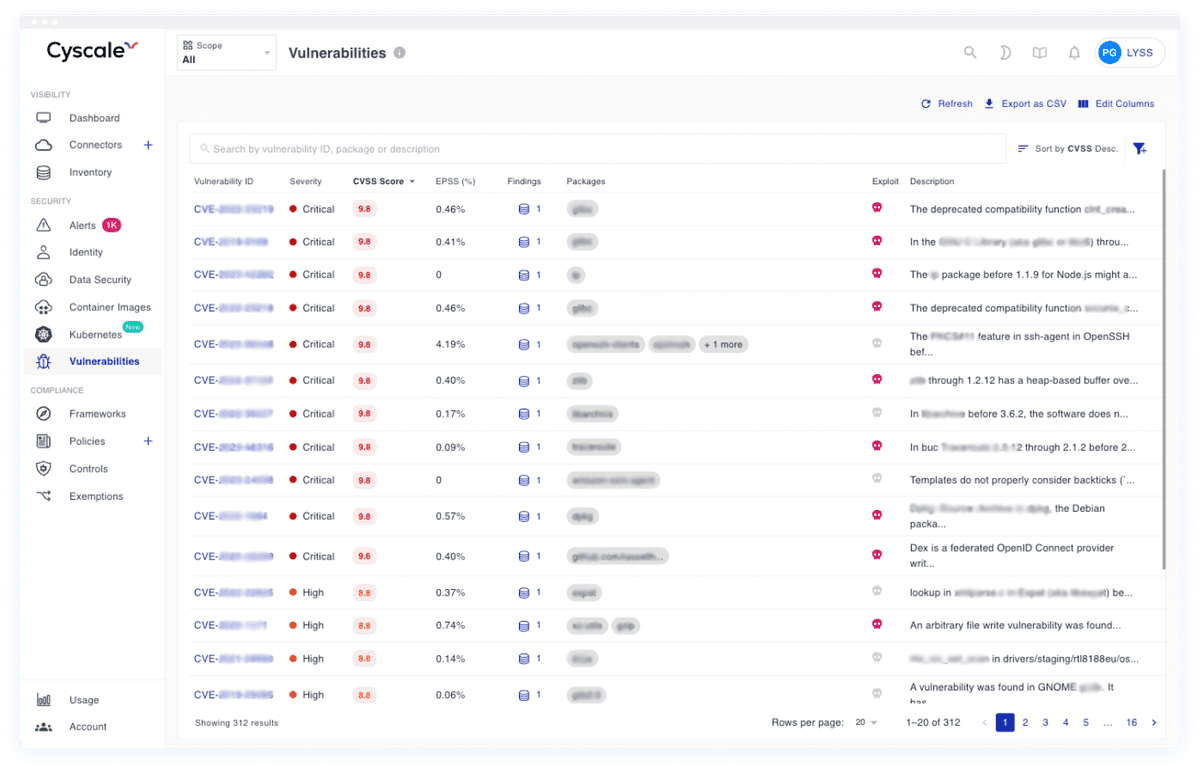
Prioritize vulnerabilities based on exploitability and exposure instead of static severity alone.
Modeled after high-performing cloud security programs, these are the workflows teams execute continuously to keep risk under control.
Mobile ecosystems expose backend APIs, identity flows, and key material to constant adversarial testing.
Frequent release cycles can hide vulnerable dependencies unless SBOM and SCA are continuous.
Serverless and containerized backend services require posture and vulnerability controls at runtime.
Security teams need automation that keeps pace with weekly and biweekly release cadences.
Cyscale Platform extends beyond posture checks and covers the software and workload security chain end to end.
Map cloud findings to the frameworks your teams and customers care about. Cyscale helps security and compliance teams track status continuously instead of preparing only for periodic audits.
They trust Cyscale to secure mobile backend infrastructure, protect API and token workflows, and fix vulnerabilities before production releases.
Jitjatjo
YAZIO
Tidepool

Trainline Partner Solutions
Yes. Cyscale supports repository-level scanning and ties those findings to runtime cloud assets for practical prioritization.
Yes. Cloud function scanning and posture analysis are part of the broader workload coverage in the Cyscale platform.
Start with contextual CNAPP visibility and SBOM-driven vulnerability scanning.
Cyscale Security Wiki
Explore connected guidance, implementation notes, and decision frameworks that link directly to this topic and related Cyscale workflows.
CNAPP combines cloud posture, vulnerability management, identity context, and compliance workflows into one operating model so teams can fix risk faster.
CSPM continuously identifies cloud misconfigurations and policy violations across AWS, Azure, and Google Cloud to reduce breach exposure and audit risk.
Cloud vulnerability management must connect software findings with runtime context so teams can prioritize exploitable and exposed issues first.
Cloud compliance programs work best when technical controls, evidence collection, and remediation ownership are continuous rather than audit-driven.
Stay connected
Receive new blog posts and product updates from Cyscale
By clicking Subscribe, I agree to Cyscale’s Privacy Policy
© 2026 Cyscale Limited