Platform
Cloud Vulnerability Management
Cyscale helps teams understand where vulnerable code, packages, images, and workloads are running, then prioritize remediation by real exposure and cloud impact.
- Correlate code and dependency findings with cloud runtime.
- Prioritize exploitable issues based on exposure and workload context.
- Reduce remediation noise across workloads, containers, and cloud assets.
Operational risk view
Cloud vulnerability management with runtime context
Bring together software findings, deployed workloads, and exposure signals so security and engineering teams can focus on the issues most likely to affect production.
1 shared queue
for software findings, runtime context, and cloud exposure across the estate
Runtime aware
triage that weighs internet exposure, reachability, service criticality, and ownership
Daily re-checks
to keep vulnerability visibility current as workloads, images, and SBOM data change
What Cyscale helps you do
If you are investing in cloud vulnerability management, you need more than a long CVE list. You need code-to-runtime context, practical prioritization, and remediation workflows your engineering teams will actually use.
See where vulnerabilities run
Map vulnerable packages, base images, and code findings to the workloads, services, and cloud assets that are actually deployed.
Triage with context
Prioritize based on exposure, service criticality, and cloud reachability instead of relying on CVSS or raw alert volume alone.
Speed up remediation
Give engineering and platform teams enough runtime context to patch the right workloads, validate fixes faster, and reduce backlog noise.
What you should expect
What you should expect from cloud vulnerability management
If you are evaluating cloud vulnerability tools, you should expect one workflow that connects vulnerability data to runtime reality. Cyscale gives you that without adding more operational overhead.
You should expect
Code to runtime visibility
Your cloud vulnerability platform should connect packages, images, workloads, and exposed services instead of leaving you with isolated scan results.
You should expect
Less noise, better prioritization
You should get reachability, exposure, and business context so engineering only sees the issues most likely to create real cloud risk.
With Cyscale
Built for live workloads
Cyscale release updates added Kubernetes vulnerability scanning with in-cluster SBOM generation, recurring re-checks, and targeted views for workloads affected by specific vulnerabilities.
Visibility
Understand where vulnerable software is actually running
Cloud vulnerability management breaks down when teams cannot tell which findings are tied to production workloads, which ones affect exposed services, and which ones still matter after deployment changes.
Cyscale connects vulnerability data to the cloud resources that run it so security, platform, and engineering teams can work from the same picture of deployed risk.
- Coverage across packages, images, workloads, and cloud services in one operational view.
- Clear mapping from finding to workload, service, and environment.
- Fewer disconnected dashboards when triaging vulnerability noise.
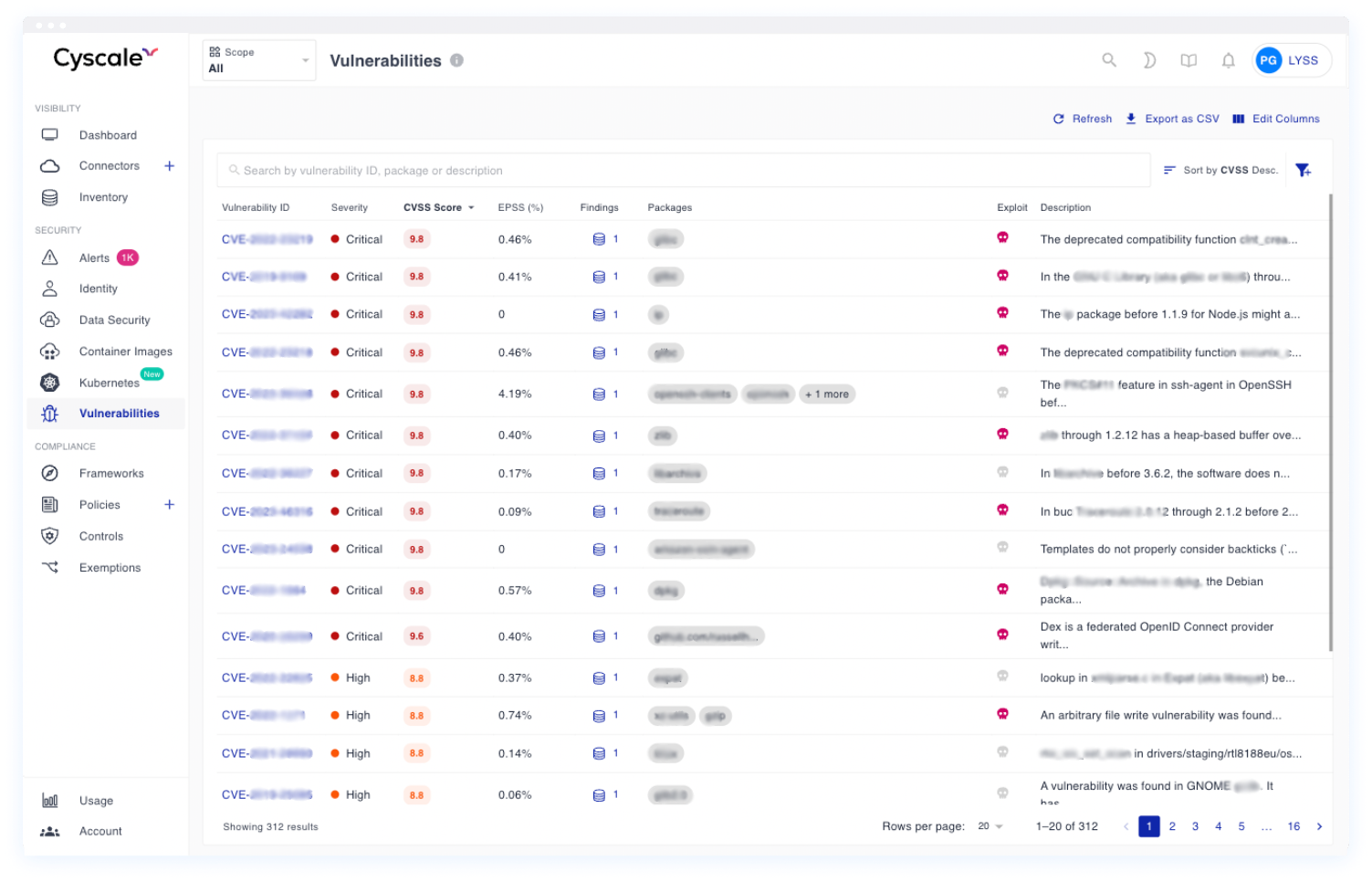
Use one view to understand which vulnerable workloads are active, where they run, and which issues belong at the top of the remediation queue.
Prioritization
Reduce noise before it becomes an engineering backlog problem
The market has moved toward contextual prioritization because raw severity alone does not tell teams what matters most in production. Internet exposure, reachability, business criticality, and ownership all change urgency.
Cyscale helps teams separate background hygiene from exploitable risk so remediation starts with the cloud services that are most likely to be targeted or affected first.
- Prioritize findings affecting internet-facing or sensitive workloads first.
- Use cloud context to explain why an issue should be fixed now versus scheduled later.
- Give engineering clearer remediation paths with less back-and-forth.
Contextual scoring helps teams move from large finding lists to a smaller, better-defended queue that engineering can work through faster.
How teams use the platform
This is the operating model strong cloud vulnerability programs increasingly follow: unify signals, apply context, and drive remediation with enough clarity to keep momentum.
Step 1
Ingest vulnerability signals
Bring together findings across dependencies, code, containers, and workloads into one operational view.
Step 2
Rank what matters most
Use deployment, exposure, and service context to focus on what could actually be exploited in the cloud estate.
Step 3
Drive remediation with context
Help teams patch the right workloads first, validate fixes, and show measurable progress in backlog reduction.
Related playbooks and product flows
Use these pages to connect posture findings, CVE triage, AppSec signals, and remediation workflows across the broader Cyscale platform.
FAQ
How is Cyscale different from a basic vulnerability scanner?
Cyscale helps teams understand where vulnerable software is running in cloud environments and prioritize remediation by real exposure, runtime relevance, and operational context.
Can Cyscale help reduce vulnerability noise?
Yes. Cyscale correlates findings with deployment and cloud context so teams focus on vulnerabilities that affect meaningful workloads and services instead of treating every alert equally.
Does cloud vulnerability management only cover containers?
No. Effective programs also cover repositories, dependencies, images, workloads, and the cloud environments where those artifacts run.