Security Operations Use Case
Code Vulnerability Scanning
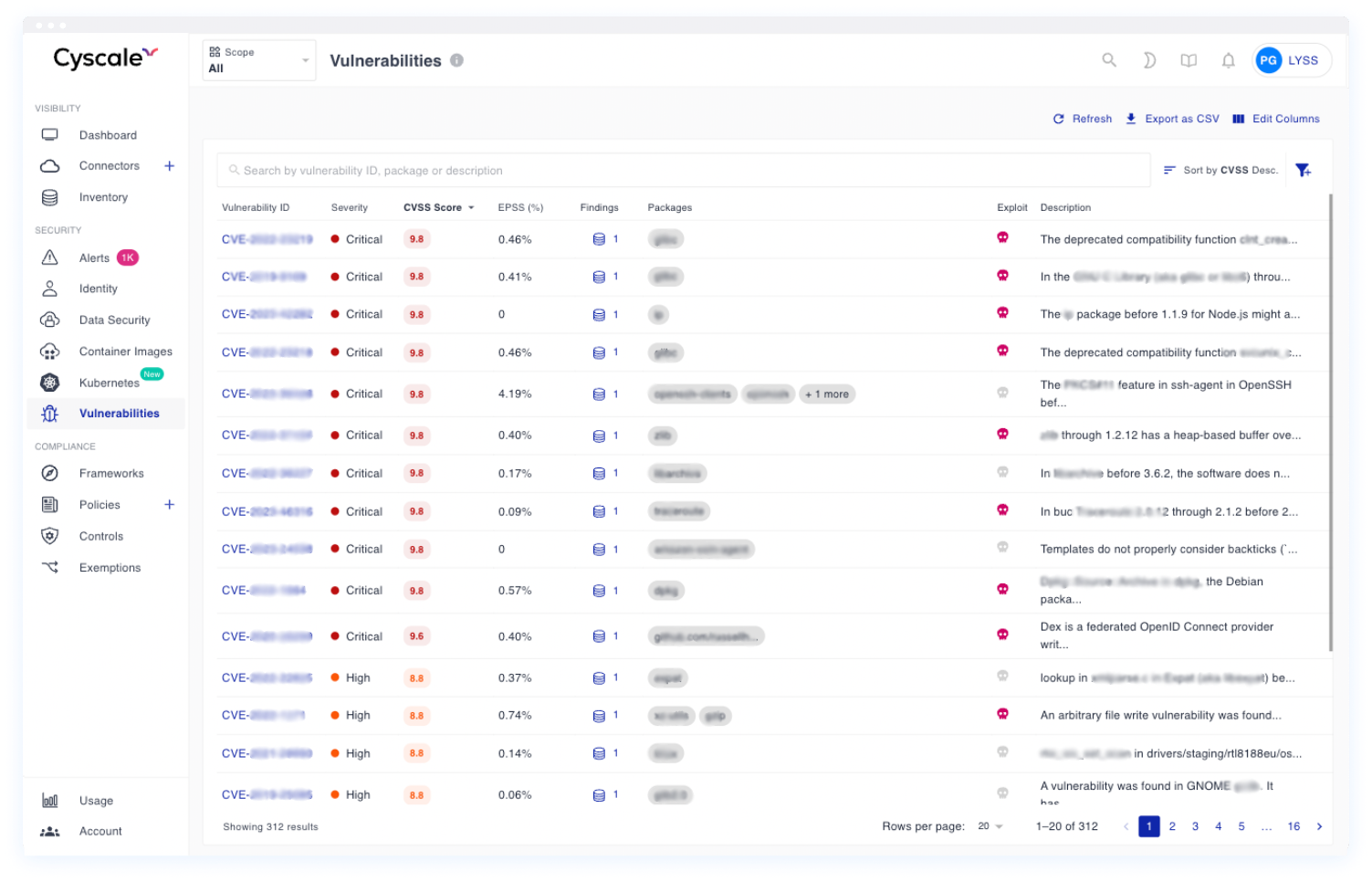
Cyscale helps teams connect code, dependency, and runtime findings so they understand what is actually deployed, what is exposed, and what needs to be fixed first.
- Connect SCA, SAST, DAST, and cloud runtime context in one place.
- Prioritize issues based on where vulnerable code is actually deployed.
- Reduce remediation noise before it becomes exploitable cloud risk.
Operational risk view
From scan result to deployed risk
Bring together SCA, SAST, DAST, and cloud runtime context so teams can see which findings affect production and which ones can wait.
Deployed-risk clarity
for the code findings that actually affect running workloads and exposed services
Smaller queues
when code-security alerts are filtered through runtime relevance and ownership
Better remediation
because engineering gets service, workload, and cloud context with the issue
What this workflow gives security and engineering teams
The value of code vulnerability scanning is not just more findings. It is knowing which findings matter in production and getting them to the right teams with enough context to fix them quickly.
Deployed-risk visibility
See whether code and dependency findings are tied to workloads that are running in production, exposed externally, or linked to sensitive cloud assets.
Noise reduction
Correlate code and cloud signals so teams spend less time comparing separate dashboards and more time fixing what matters.
Actionable remediation
Route findings with clearer ownership and business context so cloud, platform, and engineering teams can act faster.
What you should expect
What you should expect from code vulnerability scanning
If you are investing in code vulnerability scanning, you should expect one system that can unify scan types, add runtime evidence, and help engineering focus on a smaller set of meaningful issues.
You should expect
Unified AppSec signals
SCA, SAST, DAST, secrets, and artifact findings should be triaged together instead of in separate queues.
You should expect
Runtime-based urgency
You should know whether a finding affects a deployed, reachable, or sensitive service before you elevate it.
With Cyscale
Cloud-aware code triage
Cyscale connects code findings to workloads, runtime exposure, and graph-based context so teams can prioritize what is operationally relevant.
Visibility
Connect code findings to the workloads that actually run
Code vulnerability scanning creates value only when it is connected to deployment reality. Security teams need to know whether a vulnerable package or insecure code path is running in production, which workload uses it, and whether that workload is exposed to the internet or sensitive identities.
That is where an ASPM-style workflow helps. Instead of treating every SCA, SAST, and DAST alert as equally urgent, teams can triage based on cloud exposure, service criticality, and remediation ownership.
- Unify SCA, SAST, DAST, and cloud runtime findings in one place.
- Understand which services and workloads are actually affected.
- Give security and engineering a shared picture of deployed code risk.
Graph-based context helps teams understand how a repository finding connects to runtime services, cloud identities, and the paths that matter in production.
Execution
Reduce code-security backlog with better prioritization
Engineering teams lose time when security queues are shaped by raw scan volume instead of real production impact. The result is a long backlog with too little context and too many debates about urgency.
Cyscale helps teams rank code issues by deployment, exposure, and service importance so remediation becomes easier to defend and easier to complete.
- Focus first on findings affecting exposed or business-critical services.
- Deduplicate effort across application, platform, and security teams.
- Move from issue to owner to remediation faster.
Use one queue to decide what to fix now, what to schedule, and where to send engineering effort first.
How teams reduce code-security backlog with Cyscale
Teams that make code scanning useful follow a practical loop: map findings to runtime, triage by real impact, and hand off remediation with enough context to keep engineering moving.
Step 1
Map findings to runtime
Connect repository and dependency alerts to the workloads, services, and cloud assets that actually use them.
Step 2
Triage by real impact
Focus on what is exposed, reachable, or tied to important services instead of escalating every code finding equally.
Step 3
Drive remediation
Assign fixes to the right teams with enough deployment context to patch, validate, and close issues faster.
Related playbooks and product flows
Use these pages to connect posture findings, CVE triage, AppSec signals, and remediation workflows across the broader Cyscale platform.
FAQ
How is code vulnerability scanning different from cloud vulnerability management?
Code vulnerability scanning starts with application and dependency findings, while cloud vulnerability management also includes workload, image, infrastructure, and runtime prioritization. The strongest programs connect both.
Why does context matter so much for SCA, SAST, and DAST findings?
Because many findings are not equally risky. Teams need to know whether the affected code or dependency is running in production, internet-exposed, or tied to sensitive data and identities.
Can Cyscale help reduce noise in code-security queues?
Yes. Cyscale helps teams correlate findings, understand where issues run, and prioritize fixes by real cloud impact instead of raw alert volume.