DORA Compliance
DORA compliance for
cloud-first financial operations
DORA applies from January 17, 2025 and raises the bar for ICT risk management, incident handling, resilience testing, and third-party oversight in financial services.
Cyscale gives security and compliance teams a practical operating layer to monitor, prioritize, and remediate cloud risk with evidence that supports DORA programs.
DORA pillars translated into daily cloud-security operations
ICT risk management
DORA requires financial entities to establish a robust ICT risk-management framework with clear ownership, controls, and lifecycle governance.
ICT incident management and reporting
Teams must classify, manage, and report major ICT incidents with structured communication to regulators and stakeholders.
Digital operational resilience testing
Organizations should test detection and response capabilities, including advanced threat-led exercises where applicable.
Third-party ICT risk management
DORA places strong emphasis on managing ICT supplier dependencies, concentration risk, and contractual security obligations.
How Cyscale supports DORA technical compliance programs
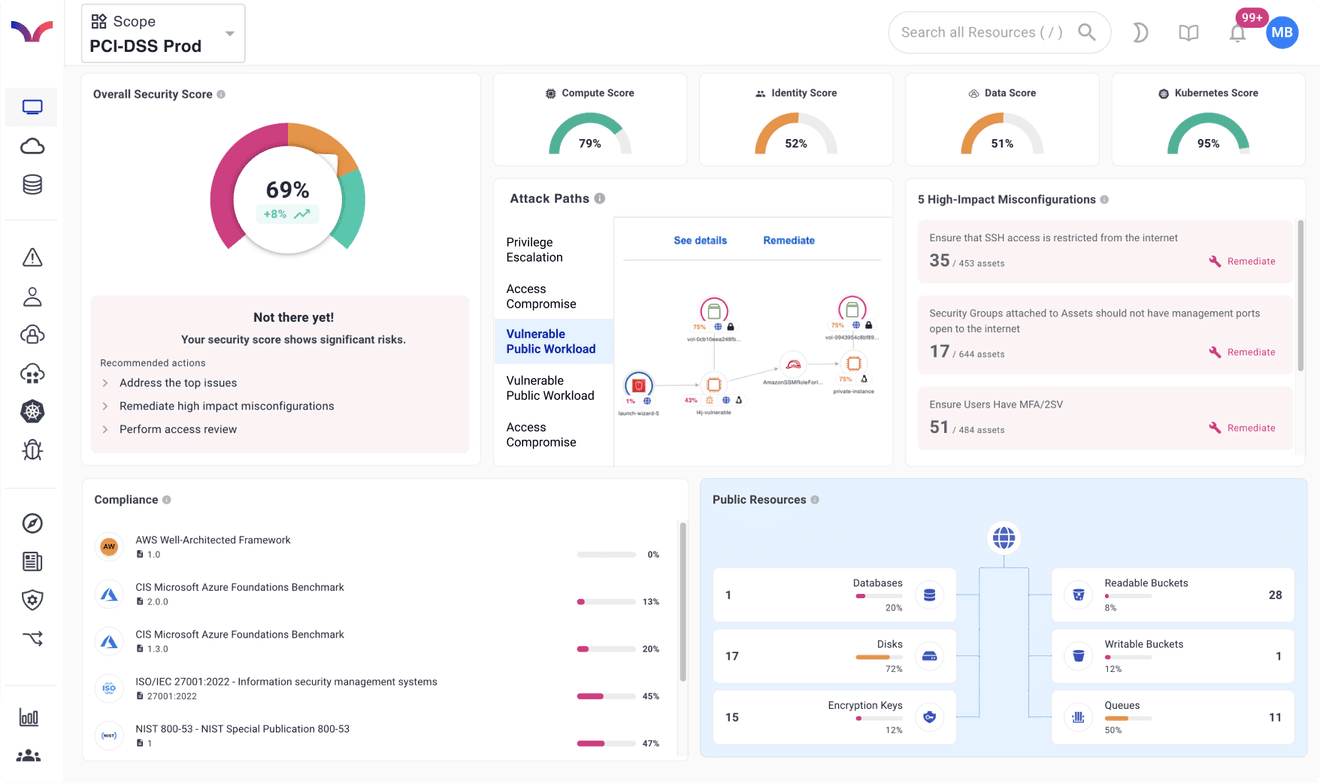
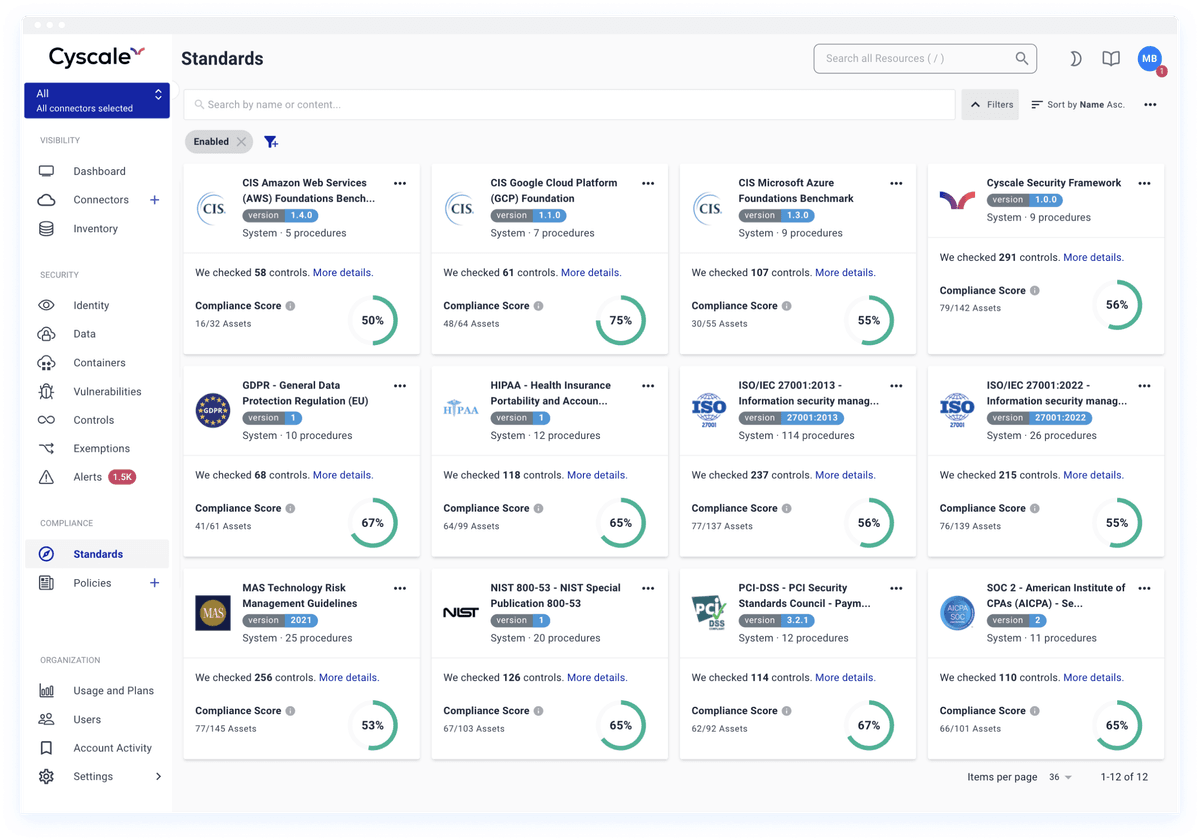
Continuous control monitoring
Cyscale continuously evaluates posture and identity risk across cloud assets and keeps compliance drift visible for operational teams.
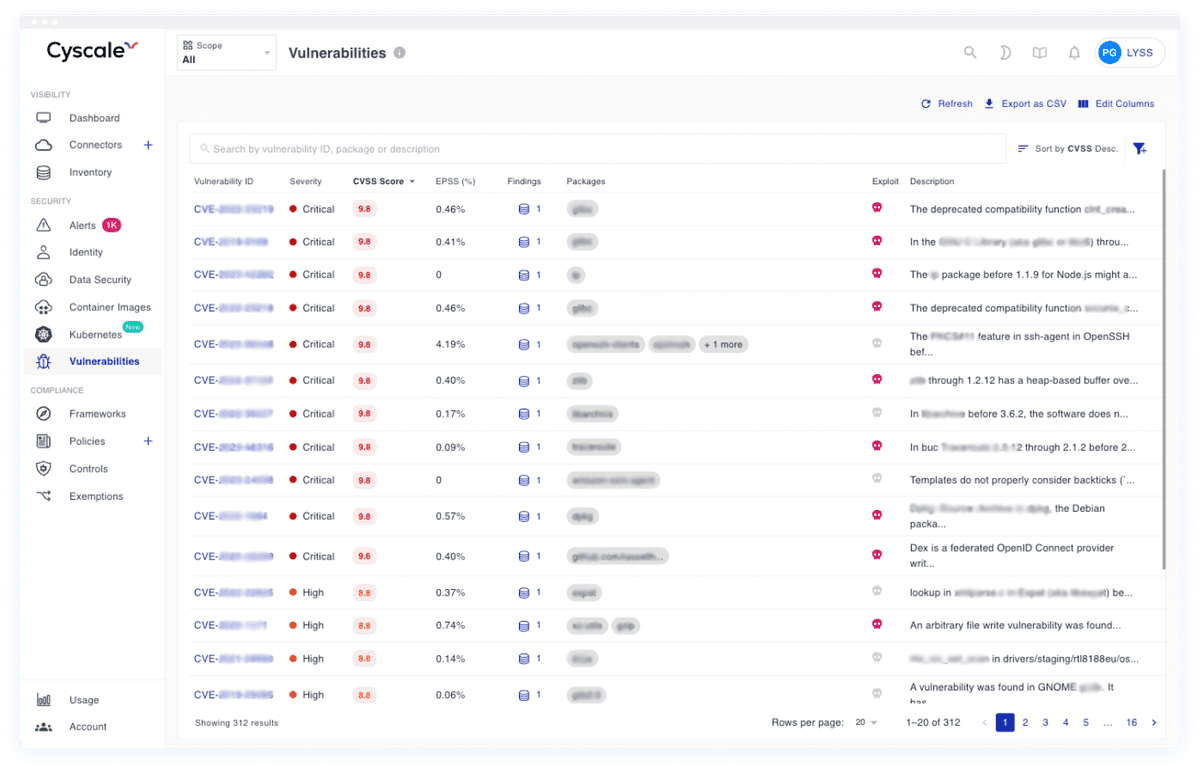
Vulnerability and software-risk governance
SBOM-based scanning across repositories, Docker images, Kubernetes, VMs, and cloud functions supports practical vulnerability governance under DORA.
Incident evidence and remediation traceability
Security teams can track ownership, remediation status, and evidence history to support ICT-incident communication and governance updates.
Supplier and concentration-risk visibility
Cloud asset context, integration visibility, and policy findings help teams identify third-party exposures and prioritize mitigation.
First 45 days of DORA cloud-readiness with Cyscale
Days 1-10
Baseline ICT risk posture
Connect cloud environments, identify critical services, and establish high-risk findings tied to resilience and availability impact.
Days 11-25
Prioritize major risk paths
Focus on exploitable vulnerabilities, misconfigurations, and identity exposures that could trigger major ICT incidents.
Days 26-45
Operationalize reporting rhythm
Build recurring evidence exports for management bodies, compliance stakeholders, and regulator-facing incident workflows.
Note: Cyscale supports technical implementation, monitoring, and evidence for DORA programs. Final regulatory interpretation should be validated with legal and compliance counsel.
Improve DORA readiness with one cloud-security operating model
Connect environments, prioritize major ICT risk paths, and keep reporting evidence ready for management and regulator workflows.
RECOMMENDED ARTICLES