Microsoft Entra ID Security
Microsoft Entra ID security
built for fast remediation
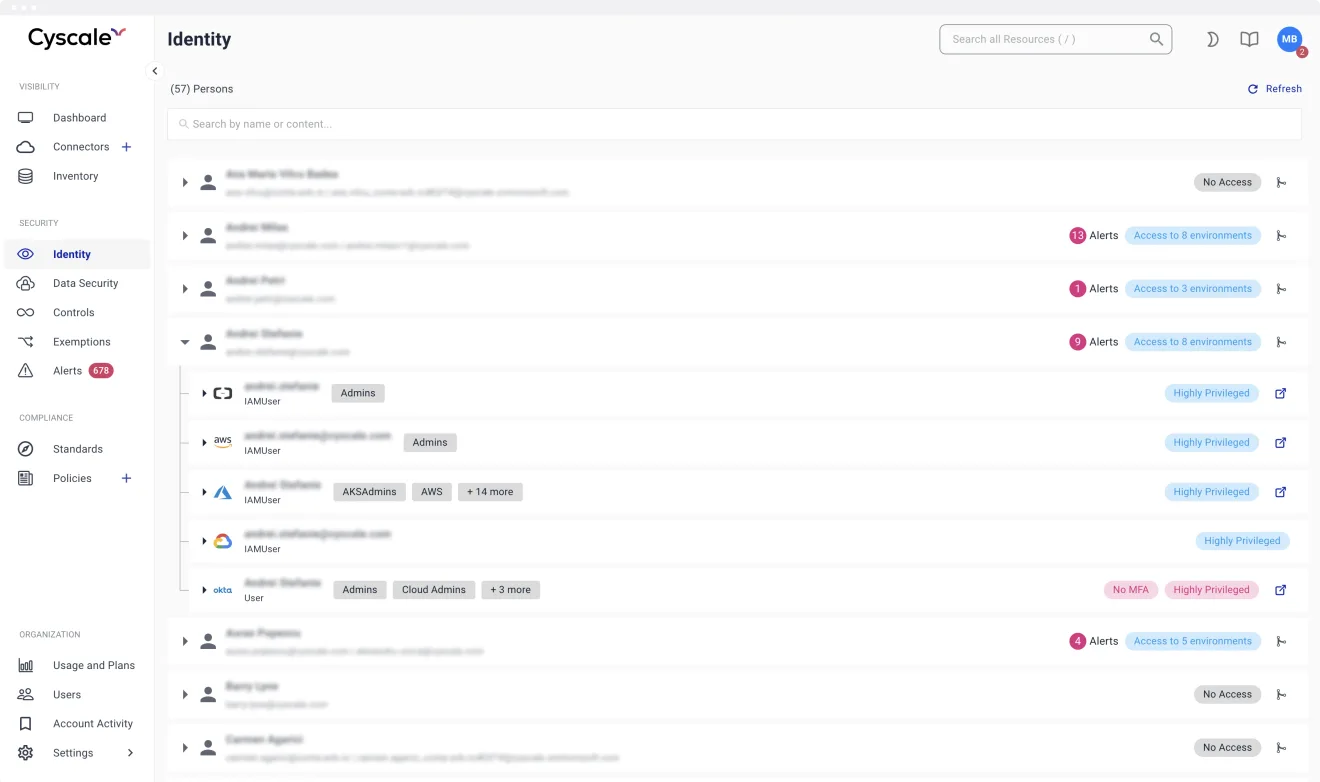
Microsoft Entra ID (formerly Azure AD) is your access control plane. Cyscale helps you continuously monitor risky sign-ins, Conditional Access posture, role hygiene, and workload identity exposure.
Instead of isolated identity alerts, your team gets contextual remediation based on actual cloud blast radius across AWS, Azure, GCP, Kubernetes, containers, repositories, and cloud functions.


Why security teams run Entra ID through Cyscale
See identity risk with cloud context
Prioritize alerts based on exposed data paths, reachable workloads, and asset criticality, not raw event volume.
Govern human and workload identities
Track over-privileged users, stale admin assignments, service principals, and workload identities that expand attack paths.
Improve audit readiness continuously
Maintain evidence for MFA, Conditional Access, least privilege, and identity controls mapped to SOC 2, ISO 27001, NIST, and PCI.
What Cyscale monitors in Entra ID environments
- Risk-based access coverage and Conditional Access rollout drift, from report-only to enforced policies.
- Privileged role hygiene, including standing admin permissions versus just-in-time access patterns.
- Service principals and workload identities that bypass expected controls and broaden lateral movement paths.
- Legacy identity protection policy exposure, including retirement planning before October 1, 2026.
- SBOM-based vulnerability workflows for VMs, Kubernetes, container images, repositories, and cloud functions tied to identity blast radius.
First 30 days with Cyscale + Entra ID
Week 1
Connect and baseline
Connect Entra ID, ingest cloud context, and baseline identity risk, role sprawl, and policy drift.
Week 2-3
Prioritize highest-risk paths
Focus engineering effort on identity findings that expose critical assets or vulnerable workloads.
Week 4
Prove measurable progress
Track remediation closure, control maturity, and audit evidence from one workspace.
Connect Entra ID and start reducing identity risk in days
Get contextual cloud risk prioritization, remediation workflows, and continuous evidence from one platform.