NIS 2 Compliance
NIS 2 cloud compliance
built for operational teams
NIS 2 requires continuous cyber risk management, rapid incident communication, and stronger supplier-security oversight for essential and important entities.
Cyscale helps security teams turn NIS 2 requirements into practical cloud workflows across posture, vulnerabilities, identities, and remediation evidence.

NIS 2 requirements security leaders need to operationalize
Security governance and risk management
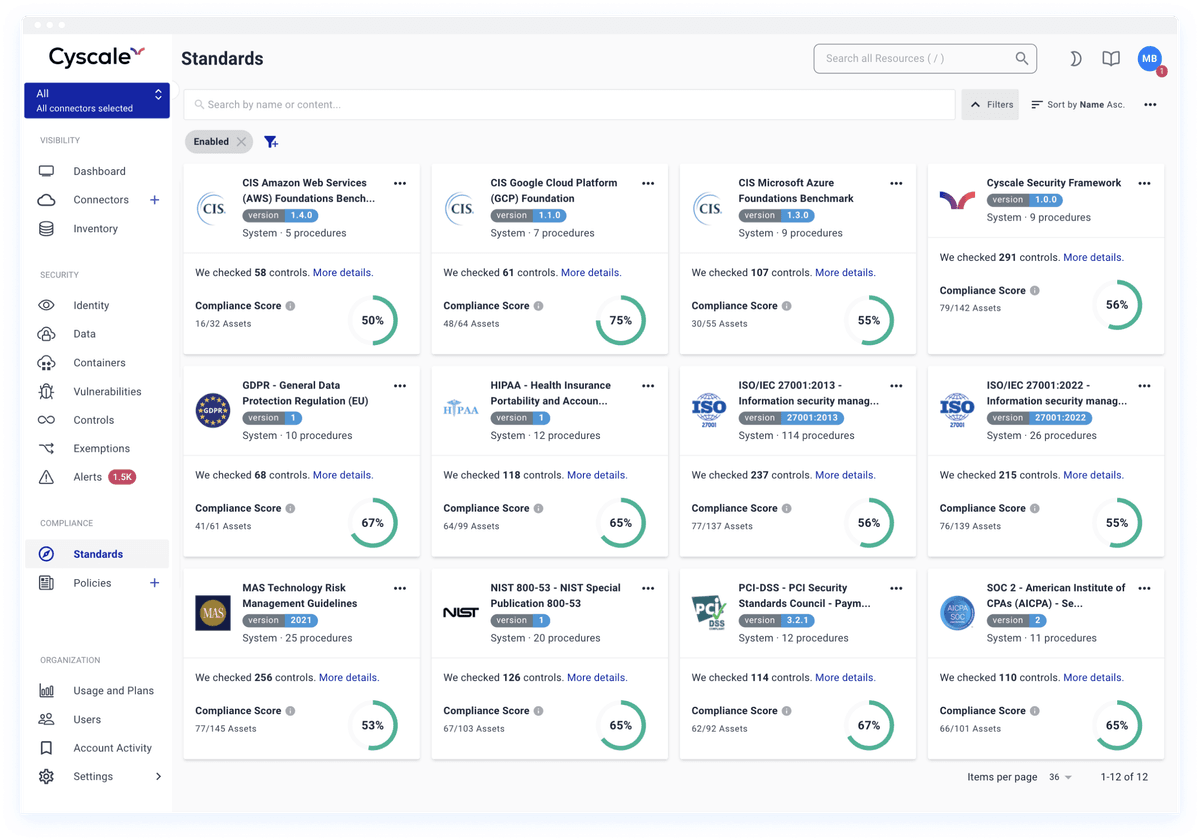
NIS2 expects organizations to implement risk-analysis and information-system security policies with measurable control ownership.
Incident response and reporting
Major incidents require an early warning within 24 hours, incident notification within 72 hours, and a final report within one month.
Supply-chain and third-party security
Entities must evaluate supplier and service-provider risk, including weaknesses introduced by cloud and software dependencies.
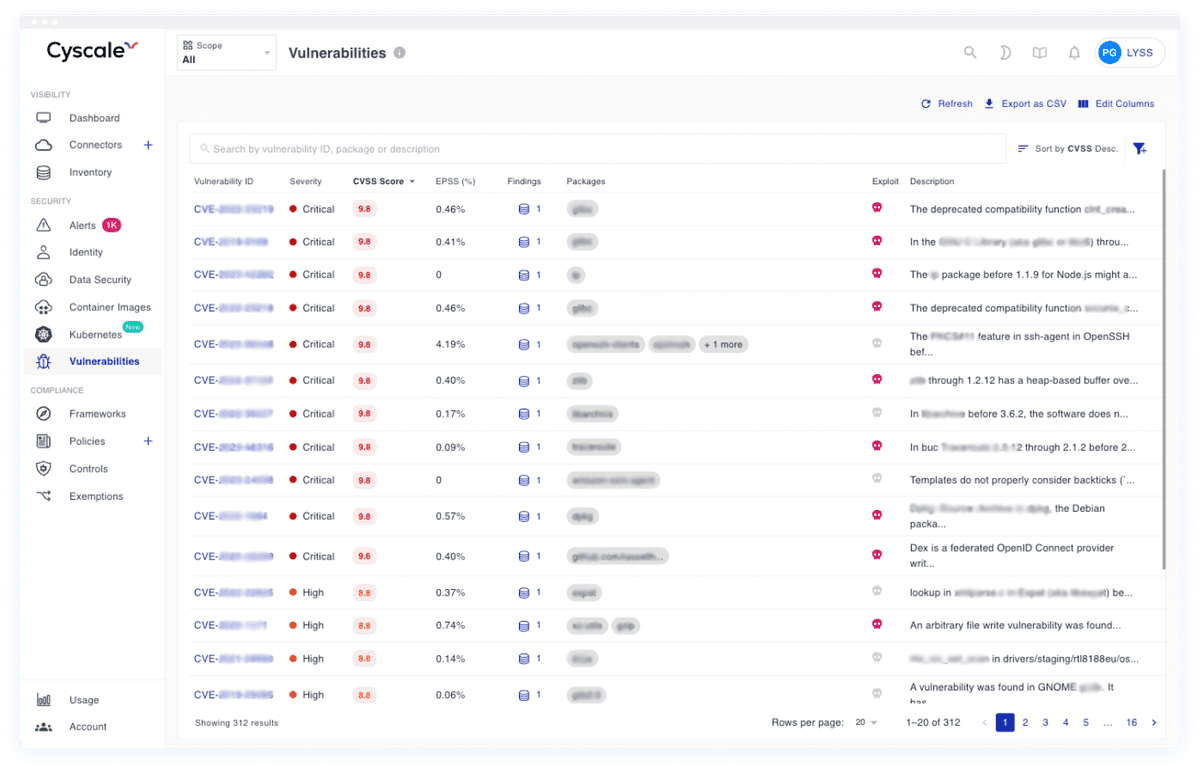
Vulnerability and disclosure readiness
NIS2 requires ongoing vulnerability handling, remediation planning, and responsible disclosure processes backed by evidence.
NIS 2 incident-reporting timeline and what to prepare
Under NIS 2, timing matters. Security teams need evidence that is quickly accessible, technically accurate, and traceable across teams.
0-24 hours
Initial detection and early warning
Capture incident scope, affected systems, and preliminary impact to support required early-warning communication.
24-72 hours
Technical incident notification
Provide validated details about likely cause, impact, and mitigation status with evidence from posture and vulnerability data.
Within 1 month
Final incident report
Submit root-cause analysis, full remediation status, and long-term corrective actions with defensible evidence trails.
How Cyscale supports NIS 2 technical measures
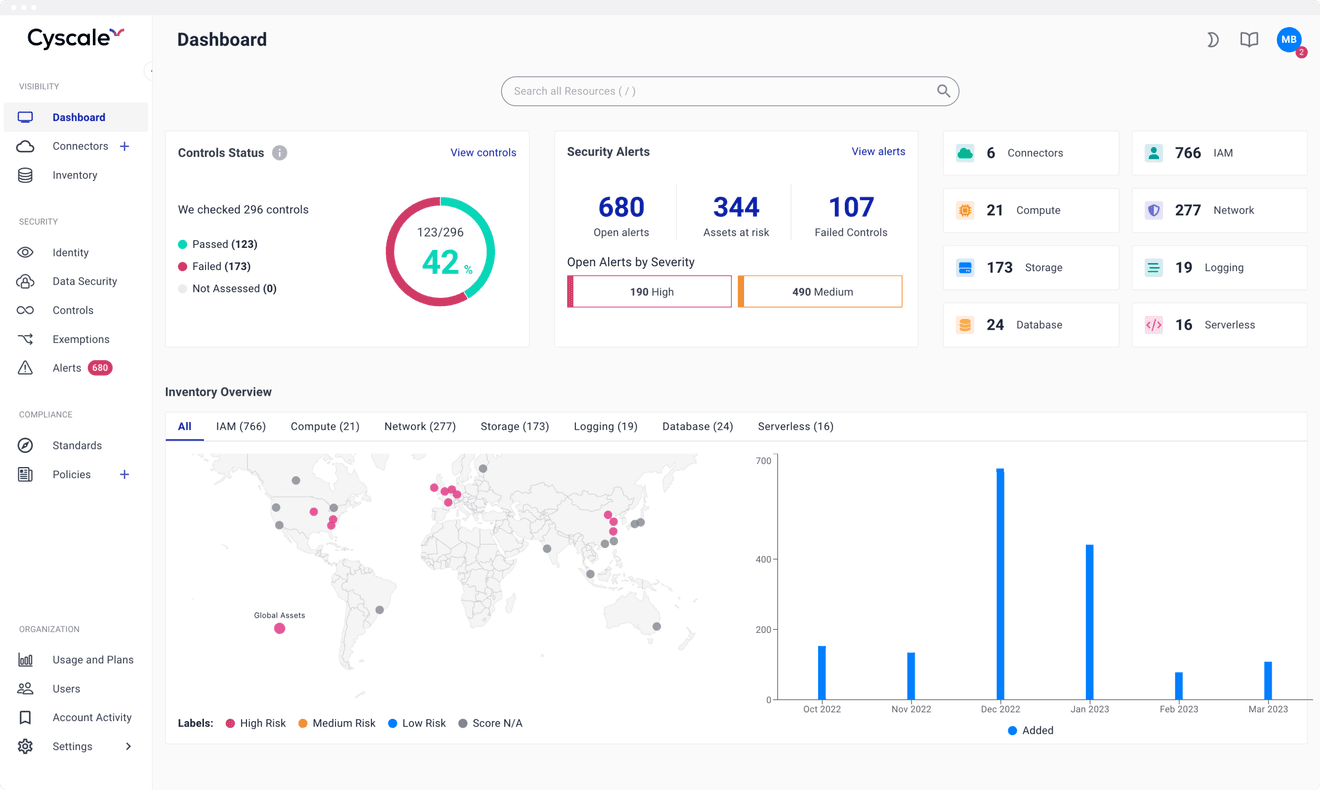
Continuous risk visibility across cloud assets
Cyscale maps your cloud inventory, identities, and exposures continuously, with priority based on exploitability and blast radius.
Evidence for governance and audits
Control findings, remediation history, and ownership tracking are available in one workspace for audit preparation and regulator reviews.
Fast incident triage and escalation
Security teams receive contextual findings with clear severity and impacted assets, helping response teams prepare 24h and 72h reporting updates.
Supply-chain and dependency risk handling
SBOM-based scanning across repositories, Docker images, Kubernetes, VMs, and cloud functions helps teams identify vulnerable components faster.
30-day NIS 2 readiness sprint with Cyscale
- Week 1: map cloud assets, critical services, and identity exposure for essential and important entities.
- Week 2: baseline high-risk posture drift, exploitable vulnerabilities, and supplier software dependencies.
- Week 3: run remediation workflows for high-impact findings and assign accountable owners.
- Week 4: package technical evidence for governance, regulator communication, and executive review.
Note: Cyscale supports technical compliance operations and evidence workflows. Legal interpretation and final regulatory scope should be confirmed with your legal counsel.
Build NIS 2 evidence continuously, not before deadlines
Connect your cloud accounts and start prioritizing the findings that matter for governance, incident readiness, and regulator confidence.
RECOMMENDED ARTICLES