CONTENTS
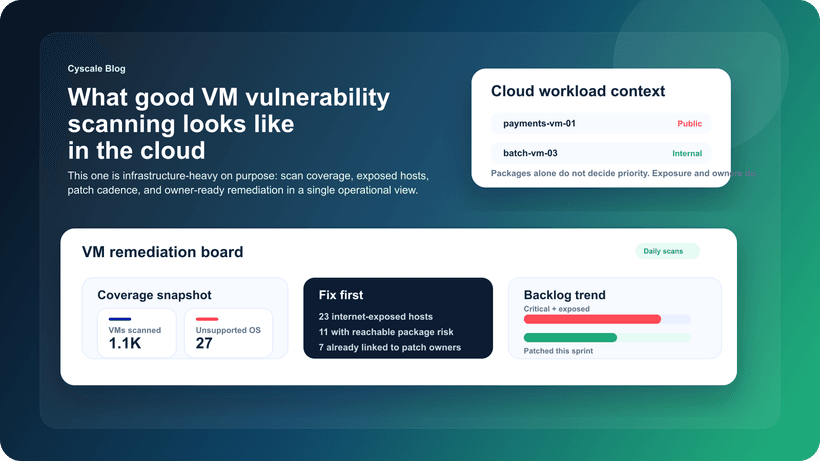
What Good VM Vulnerability Scanning Looks Like in Cloud Environments
Saturday, March 14, 2026
Updated: March 17, 2026
If your team is dealing with code, vulnerability, container, or runtime risk, Cyscale helps you cut through alert volume and understand what actually matters in production. You get practical context, faster triage, and a cleaner route to remediation.
Virtual machines are not going away.
Even in organizations with heavy container or serverless adoption, VMs still run critical services, jump hosts, data-processing jobs, integration workloads, legacy applications, and provider-specific tooling that teams cannot simply replace.
That makes VM vulnerability scanning just as relevant as ever. The problem is that many programs still run it as if the environment were static and on-premises.
Cloud environments changed the rules:
- workloads are more dynamic,
- ownership is more distributed,
- exposure changes faster,
- and patching decisions have to compete with product delivery.
So the question is no longer “are we scanning our VMs?” The better question is “are we scanning them in a way that actually improves risk reduction?”
The old model that no longer works
A lot of VM programs still follow a simple pattern:
- Scan all hosts.
- Sort by severity.
- Open tickets.
- Hope teams patch quickly.
That approach creates activity, but not always better outcomes.
It breaks down because:
- not all VMs matter equally,
- not every vulnerable package is equally exploitable,
- and not every fix can happen on the same timescale.
In cloud environments, a vulnerable VM should be judged in context:
- Is it public?
- What role is attached to it?
- Does it sit near sensitive data?
- Is it still active and business relevant?
That is what separates a useful VM program from a noisy one.
What good VM vulnerability scanning includes
1. Strong asset context
The scanner result needs to stay connected to the asset story.
That means:
- environment,
- owner,
- application or service,
- account or subscription,
- exposure,
- and whether the VM still has a real production role.
Without that context, teams waste time patching low-value assets while genuinely risky systems wait.
2. Recurring scanning, not one-time visibility
Cloud workloads change constantly. New images are deployed, packages drift, emergency fixes are applied, and old snapshots reappear in unexpected places.
A strong program re-checks continuously and treats vulnerability scanning as a live operational feed, not a monthly inventory ritual.
3. Reachability-aware prioritization
This is where VM scanning becomes much more useful.
A high-severity package on an isolated internal utility VM may matter, but it is not the same as:
- a reachable production VM,
- with a broad identity,
- sitting on a path to sensitive data,
- and carrying a package with known exploitation activity.
Good programs elevate the latter automatically.
4. Clean remediation ownership
A finding should not land in a generic security backlog. It should land with the team that owns the workload or service and include enough context to explain why it matters now.
5. Verification after the fix
Closing the ticket is not enough. Teams should verify that:
- the vulnerable package is gone,
- the asset has been rescanned,
- and the exposure story changed in the expected way.
Why VM scanning still matters in CNAPP programs
Some teams assume that because they now have CNAPP, CSPM, or container-security tooling, VM scanning is less important.
In practice, the opposite is often true.
CNAPP works best when VM scanning becomes more contextual:
- Cloud vulnerability management helps rank VM findings against broader workload risk.
- Agentless cloud scanning helps broaden coverage across cloud fleets.
- Exposure management helps separate urgent risk from general hygiene.
- Attack path analysis shows when a VM sits on a route to something more serious.
The VM does not disappear inside CNAPP. It becomes better understood.
What teams should measure
If you want a useful program, measure outcomes that reflect real execution:
- time to triage exposed high-risk VM findings,
- time to remediate confirmed high-priority VM issues,
- percentage of reachable VM issues closed within SLA,
- repeat findings caused by patch drift or image reuse,
- and backlog size after contextual prioritization, not before it.
These metrics are far more useful than “how many CVEs did we detect this month?”
A better workflow for lean teams
Smaller teams do not need a perfect VM security program on day one. They need a practical one.
Start here:
- Tag or map the VMs that matter most to production.
- Separate exposed and privileged VMs from the rest of the fleet.
- Build a fix-first queue for those assets.
- Re-scan on a recurring schedule and after major changes.
- Feed repeat patterns back into image hardening and provisioning standards.
This approach keeps the workload manageable and makes security conversations with engineering more credible.
How recent Cyscale work points in this direction
Recent platform updates around major vulnerability views, asset investigation, and Kubernetes vulnerability scanning all reinforce the same lesson: vulnerability data becomes useful when it is placed inside operational context.
Relevant release-note direction:
For VM programs, that means the ideal end state is not a longer list of packages. It is a clearer path from detected risk to accountable remediation.
Final thought
Good VM vulnerability scanning is not about scanning more often just for the sake of it. It is about scanning with enough context that teams know which hosts matter, why they matter, and what should happen next.
That is where Cyscale helps. Instead of leaving your team with a longer list of packages and CVEs, Cyscale helps connect VM findings to exposure, asset criticality, and remediation ownership so the queue becomes easier to act on and easier to defend.
If you want VM vulnerability management that fits modern cloud operations, explore Cyscale Cloud Vulnerability Management or request a demo.
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article