CLOUD SECURITY POSTURE MANAGEMENT
See what matters. Fix what is exploitable. Prove what is improved.
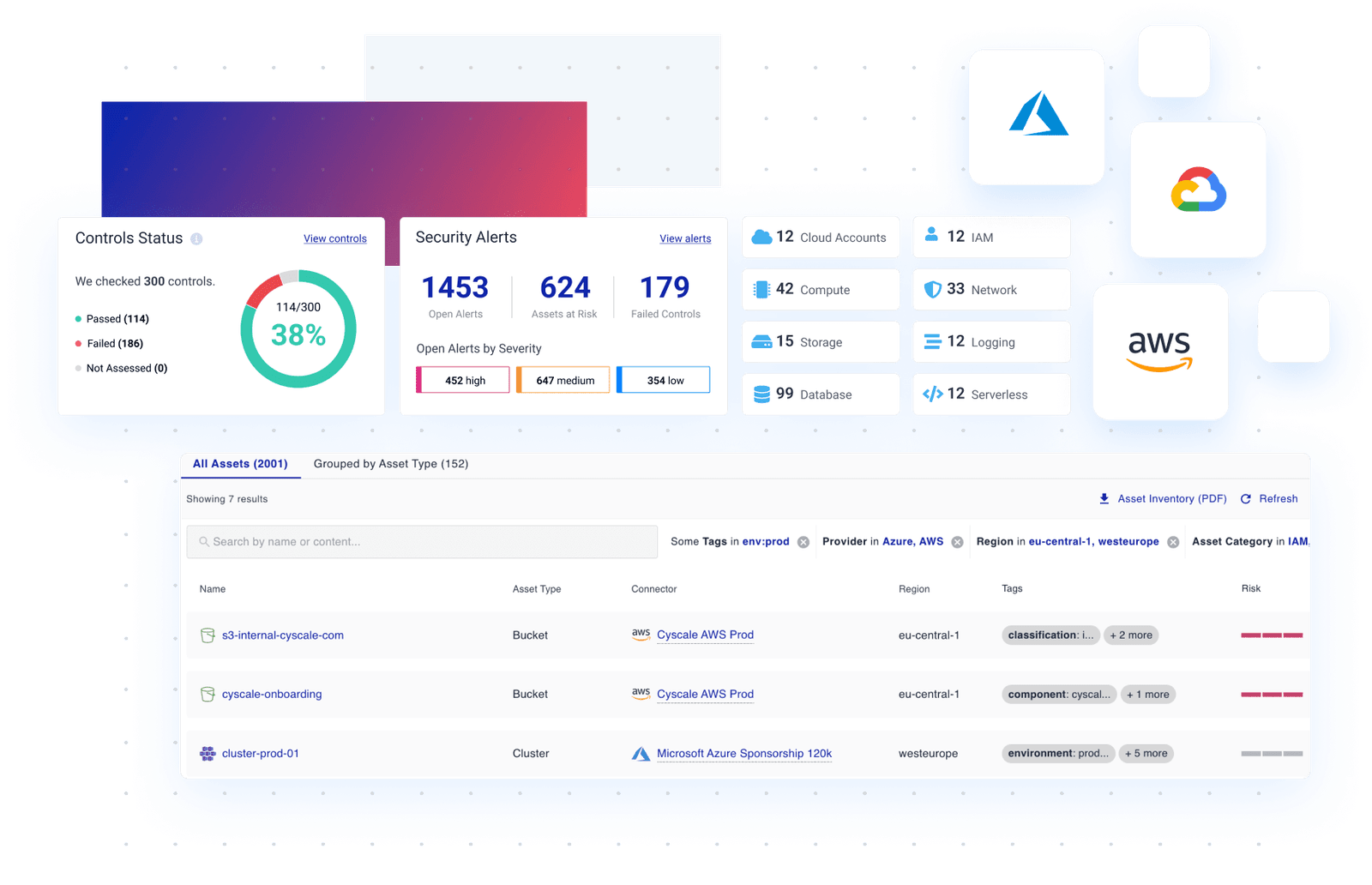
Cyscale CSPM helps cloud security teams move from alert overload to clear decisions. Detect posture drift across multi-cloud environments, prioritize by attack context, and route remediation to the right owners.
- Agentless onboarding in minutes.
- Contextual prioritization based on real blast radius.
- Actionable workflows for remediation and compliance reporting.
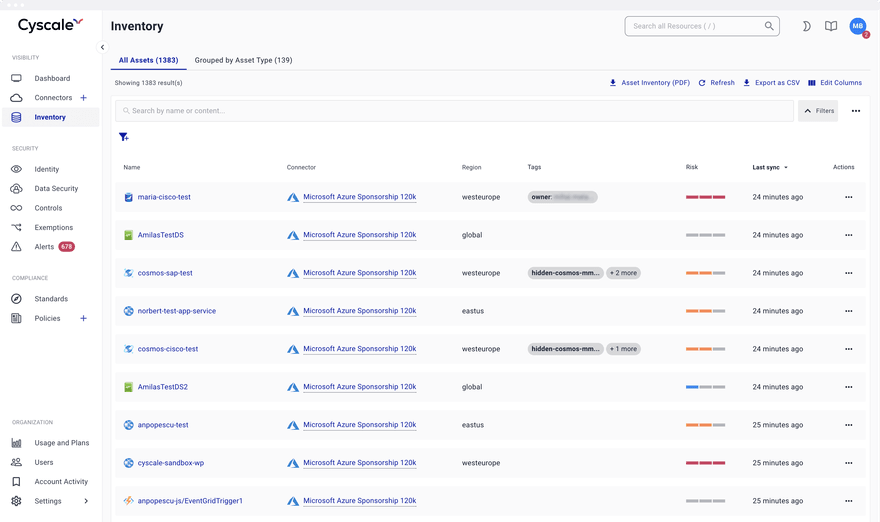
Public asset with posture drift and identity path
Risk context is already mapped for faster triage.
Built for practical cloud security outcomes
Leading cloud security platforms emphasize context, speed, and measurable remediation. Cyscale CSPM follows the same principle: help teams understand which findings truly increase business risk, then fix those first.
Prioritize what can actually be exploited
See misconfigurations in context with internet exposure, identity paths, and workload criticality so teams can act on real attack paths.
Fix faster with ownership and guidance
Convert findings into remediation tasks with clear recommendations, owner assignment, and progress tracking across security and engineering.
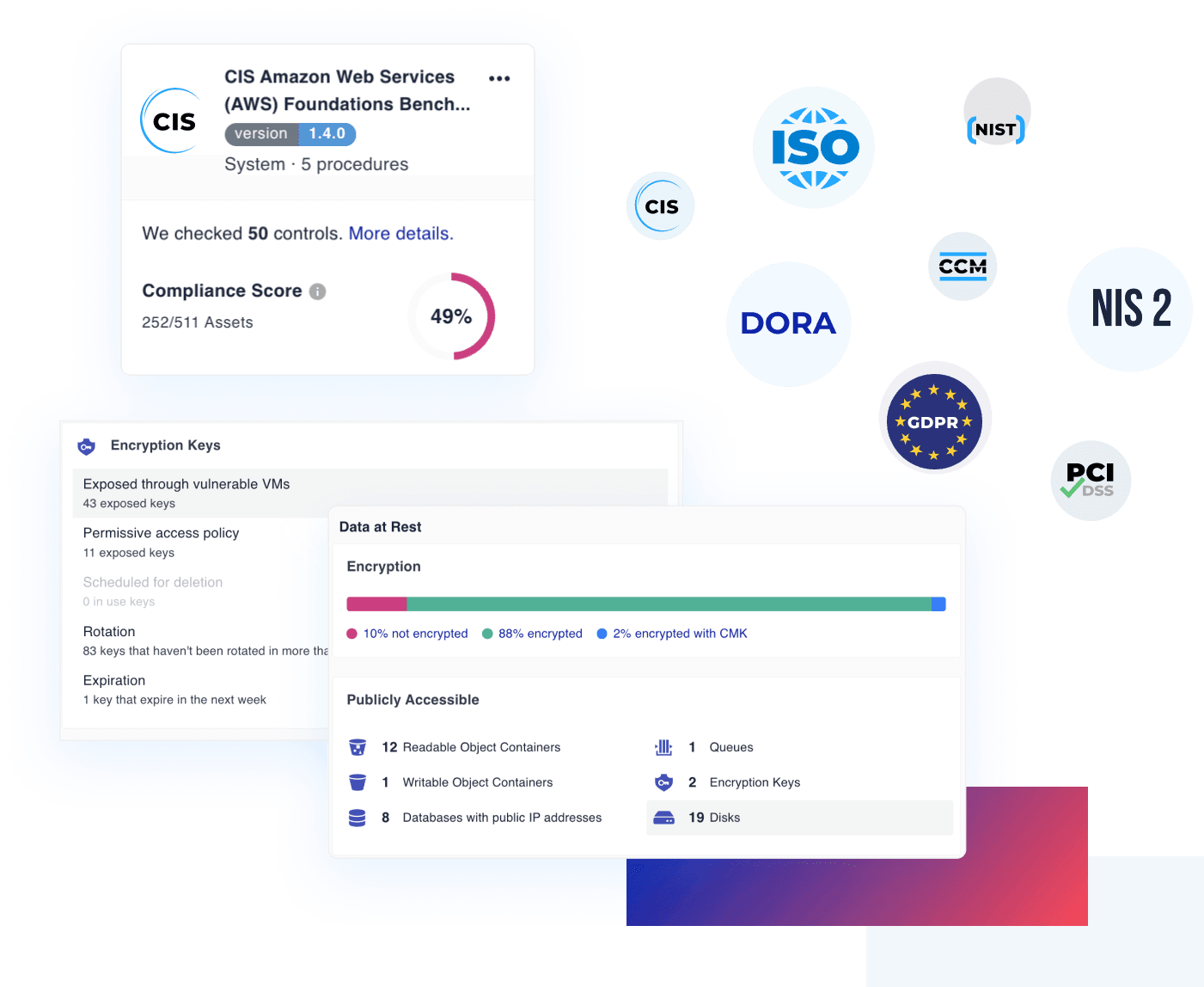
Keep compliance continuously ready
Map findings to frameworks and keep audit evidence current instead of scrambling before quarterly or annual assessments.
Prioritize posture issues the way attackers see them
CSPM becomes far more useful when posture findings are filtered through exposure, identity reachability, workload context, and ownership. That is how teams reduce noisy queues and focus on the misconfigurations that actually open attack paths.
- Escalate misconfigurations affecting exposed services first
- Tie posture findings to owners and affected environments
- Spot toxic combinations across posture and software risk
- Explain urgency with business and cloud context, not alert count alone
Actionable insight view for daily triage
Security teams need more than static lists of failed controls. Cyscale highlights the relationships that create real attack paths so triage meetings end with clear, assigned actions.
- Internet-exposed assets with high-risk misconfigurations
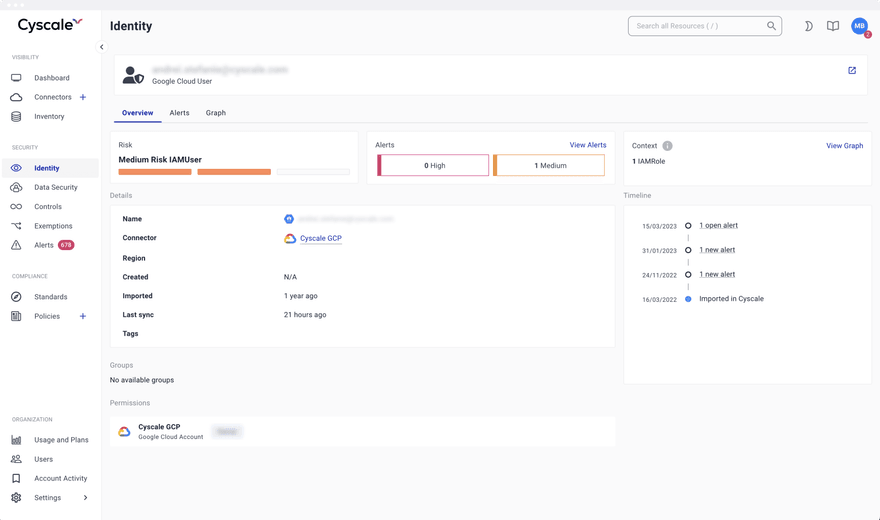
- Identity and entitlement paths to sensitive data
- Misconfiguration plus vulnerability toxic combinations
- Environment, owner, and application scoped remediation queues
- Policy drift and recurring findings that block posture improvement
How Cyscale CSPM works in real teams
01
Onboard
- Agentless setup across cloud accounts
- Immediate posture baseline and risk scoring
- Shared visibility for security and platform teams
02
Detect
- Continuous checks across identity, network, storage, and compute
- Coverage for multi-cloud misconfigurations and drift
- Policy library with customizable controls
03
Prioritize
- Contextual analysis with graph relationships
- Toxic combinations surfaced automatically
- Focus on high-impact risk, not alert volume
04
Remediate & Report
- Actionable fix steps and workflow assignment
- Status tracking by scope, team, or business unit
- Compliance reporting and exportable evidence
OPERATIONALIZE CLOUD SECURITY POSTURE MANAGEMENT
From detection to remediation without context switching
Reduce time spent chasing low-impact findings. Cyscale helps you automate posture checks, route actionable work to owners, and keep leadership informed with clear progress metrics.
Automate cloud misconfiguration
detection with context
Continuously scan cloud assets and detect drift across providers. Contextual analysis connects findings to reachable assets and likely impact so your queue reflects real operational risk.
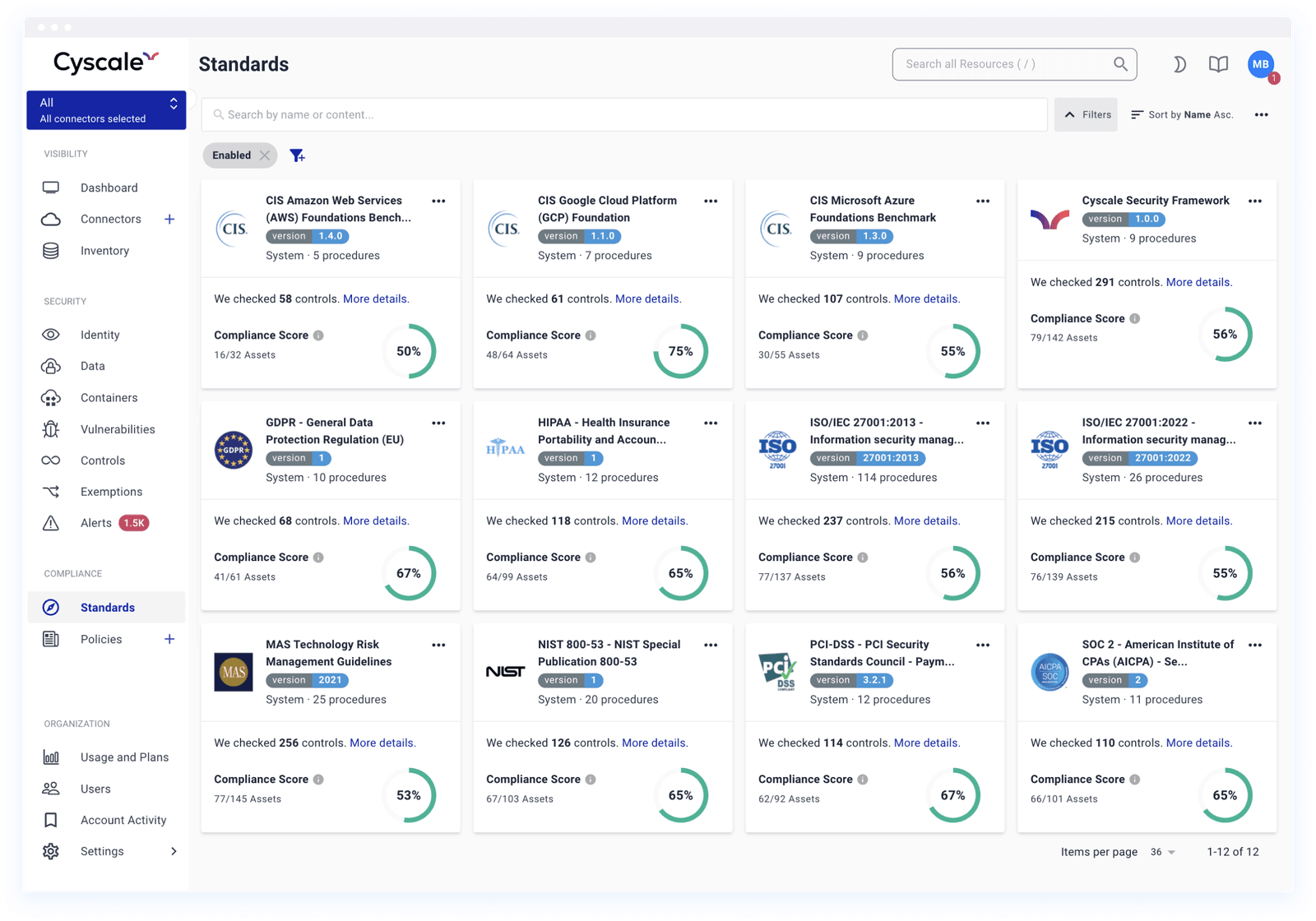
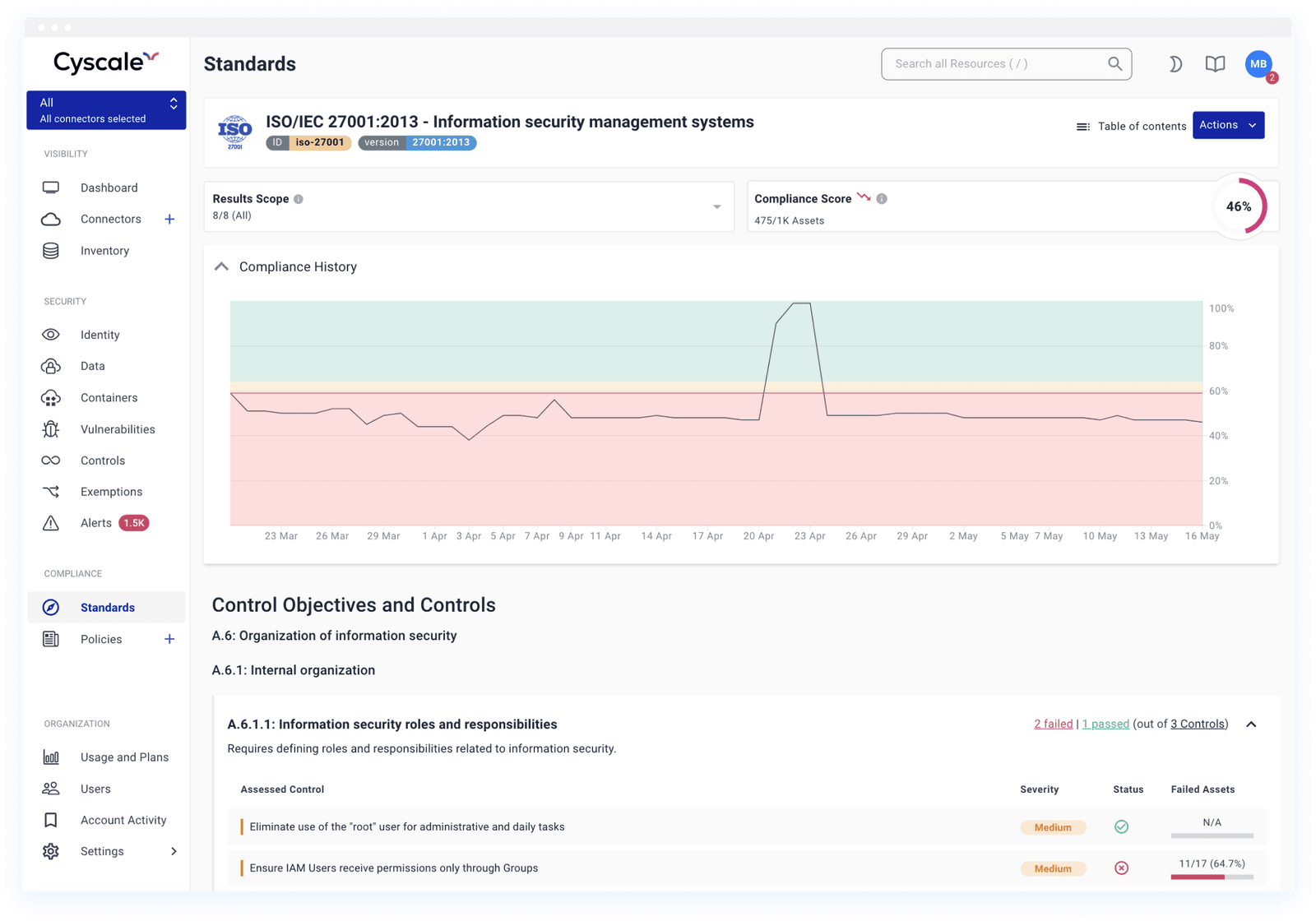
Streamline compliance
and stakeholder reporting
Map findings to frameworks like ISO 27001, SOC 2, PCI DSS, NIST, and CIS. Maintain always-on evidence, visualize trends, and export reports for audits, customers, and leadership reviews.
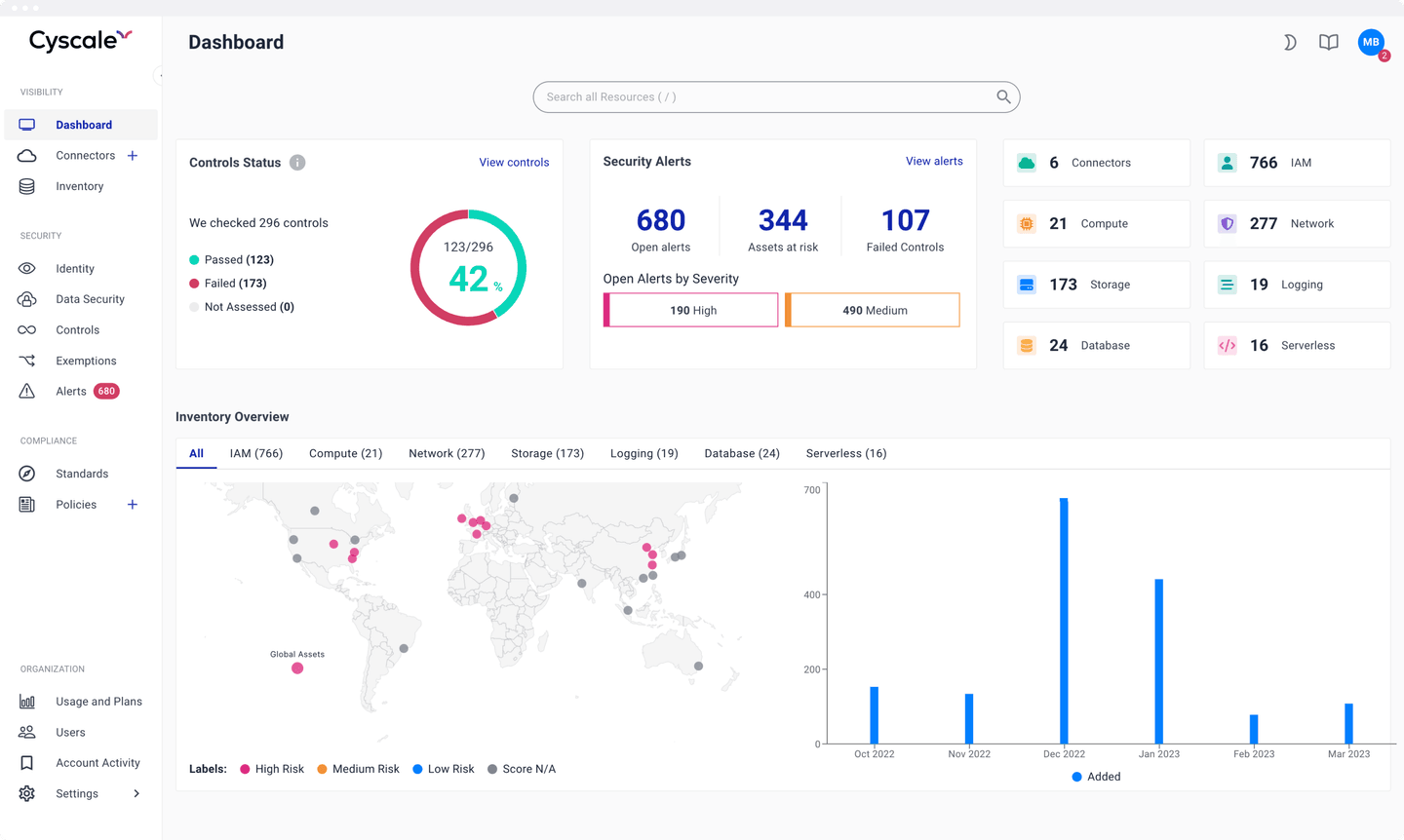
Keep one source of truth for posture and compliance
Dashboards built for action, not vanity metrics
- See posture, compliance, identity, and data risk in one unified workspace.
- Track trend lines to confirm remediation is reducing risk over time.
- Scope dashboards and reports by cloud account, app, environment, or business unit.
- Configure alerts for threshold drops so teams react before audits or incidents force it.
CSPM Operating Guide
How to run CSPM as an operational program, not a reporting project
Mature CSPM programs focus on measurable risk reduction and remediation velocity. The goal is to continuously detect drift, prioritize what is exploitable, and route fixes to the right teams with clear accountability.
- -Track posture drift continuously across identities, network paths, storage, and workload controls.
- -Correlate misconfigurations with exposure context to avoid low-value triage.
- -Use shared remediation ownership models between security and engineering teams.
- -Maintain evidence trails so compliance and audit reporting stays continuously ready.
Related playbooks
CSPM Wiki Guide
End-to-end posture management framework for cloud security teams.
IaC Scanning Wiki Guide
Prevent cloud misconfigurations before templates ever reach production.
Cloud Compliance Wiki Guide
How to keep compliance continuously aligned with cloud operations.
Multi-Cloud Security Wiki Guide
Standardize risk reduction workflows across AWS, Azure, and Google Cloud.
Container Image Scanning Wiki Guide
See how image hygiene and runtime context strengthen posture programs.
Cyscale vs AWS native stack
Compare consolidated CSPM workflows vs stitched native services.
Want actionable CSPM in your environment this week?
Connect your cloud accounts, identify exploitable risks, and start remediation with clear ownership and measurable progress.
CASE STUDY
Data security in a
multi-cloud environment
This US-based data intelligence platform needed stronger visibility and faster risk triage across a growing multi-cloud environment. Cyscale replaced fragmented tooling with one actionable workflow.
Read the case studyCASE STUDY
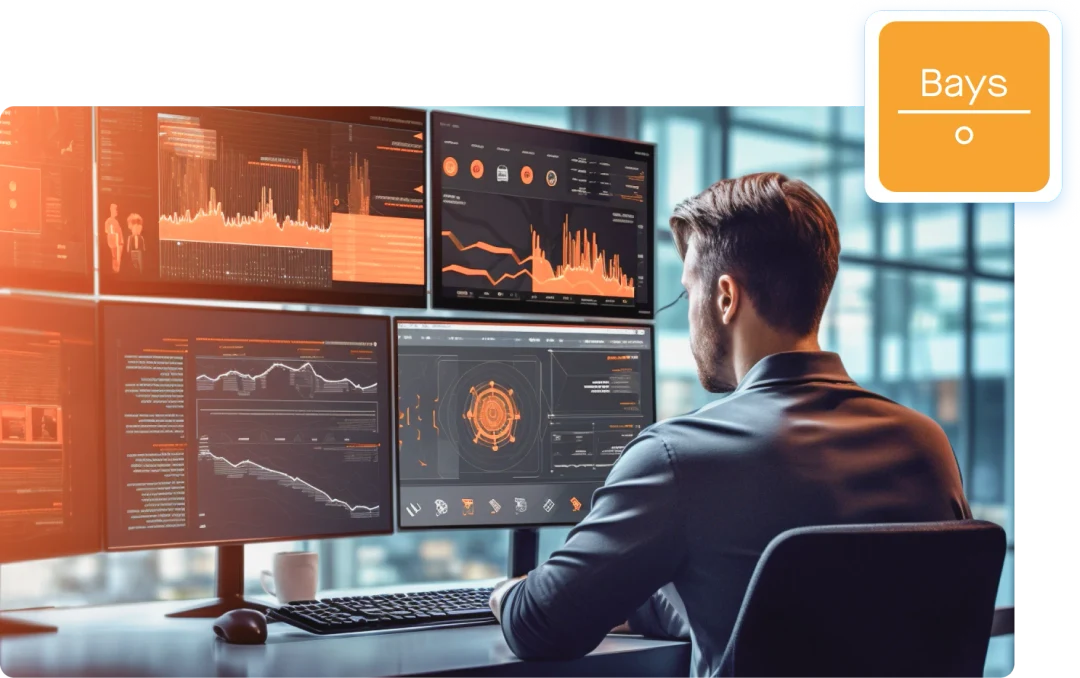
"It has been great at identifying blind spots": Bays Consulting achieves 50% productivity gain with Cyscale
"Exceptionally helpful when doing access reviews; I am using the platform monthly and it simply automates my work."

James Hawkes
Head of Delivery at
Bays Consulting
CASE STUDY
Smart Fintech uses Cyscale to improve IAM visibility and strengthen cloud compliance
"The platform helps me with IAM visibility a lot: I can understand who has access and why."

Alex Cociu
Risk and Compliance Officer at
Smart Fintech
Frequently asked questions
What makes Cyscale CSPM different from alert-heavy CSPM tools?
Cyscale does not stop at listing policy violations. It correlates misconfigurations with internet exposure, identity reachability, vulnerable software, and data sensitivity so your team can focus on the issues that create real breach paths.
See how CSPM fits into Cyscale CNAPP.How quickly can we onboard cloud accounts?
Cyscale CSPM is agentless for cloud provider onboarding. Most teams connect their first cloud account in minutes and start with an immediate baseline of posture, identity risk, exposed assets, AI services, and compliance gaps.
Security, platform, and engineering teams can then use the same workspace to triage, assign, and track remediation.
Which cloud and identity environments are supported?
Cyscale supports AWS, Microsoft Azure, Google Cloud, and Alibaba Cloud, with identity context from providers such as Okta, Microsoft Entra ID, and Google Workspace. Cyscale also supports Kubernetes visibility through the Cyscale Kubernetes agent.
You can scope findings by account, business unit, app, environment, and owner to fit how your organization actually operates.
Can Cyscale help with audits and compliance reporting?
Yes. Cyscale maps findings to frameworks such as ISO 27001, SOC 2, PCI DSS, NIST, and CIS, tracks evidence continuously, and provides reports that support internal and external audit workflows.
Explore cloud compliance workflows.Can Cyscale help us write our own cloud controls?
Yes. Cyscale supports custom controls and policies so teams can enforce internal cloud standards, compensating controls, and environment-specific rules alongside built-in frameworks.
This is useful for controls that are specific to your architecture, approved service patterns, sensitive data handling, AI Security expectations, or cloud organization model.
How does CSPM relate to AI Security in Cyscale?
AI Security uses the same posture principles as CSPM, but applies them to AI services, model endpoints, agents, datasets, vector stores, AI BOM components, and Kubernetes-hosted AI workloads.
Explore Cyscale AI-SPM.Does CSPM alone solve cloud vulnerability prioritization?
CSPM is one part of prioritization. Cyscale combines posture issues with vulnerability data, identity reachability, exposure, data sensitivity, Kubernetes workload context, and compliance impact so teams can prioritize complete cloud risk paths.
See cloud vulnerability management.RECOMMENDED ARTICLES
CSPM
The Complete Guide
to Cloud Storage Misconfigurations
This guide helps CIOs, CISOs and security teams understand cloud storage misconfiguration risks and build stronger prevention workflows.