Environment

GitHub Code Security
Use Cyscale to understand which GitHub findings matter in production by connecting repository risk with cloud workloads, exposure, and remediation ownership.
- See which GitHub findings actually affect cloud runtime.
- Reduce repository-alert noise with deployment and exposure context.
- Help engineering fix what is running and reachable first.
Operational risk view
Make GitHub findings easier to explain and fix
Map repository, dependency, and secret findings from GitHub to the workloads and services they actually affect in the cloud.
Repository to runtime
visibility that shows whether a GitHub finding reaches a live workload or service
Cloud-aware triage
that separates routine repository noise from issues affecting exposed environments
Faster handoff
from GitHub alert to engineering owner, affected service, and remediation path
How Cyscale improves GitHub security workflows
GitHub findings are most useful when they can be tied to what is actually deployed. Cyscale helps teams keep repository scanning connected to production reality.
Repository-to-runtime context
Map GitHub-originating code, dependency, and secret findings to workloads and services that are actually deployed.
Prioritized triage
Help teams focus on findings affecting exposed or business-critical services instead of responding to repository noise alone.
Cleaner remediation handoff
Give engineering teams enough cloud context to patch the right places and validate fixes faster.
What you should expect
What you should expect from GitHub code security
If your team works in GitHub, you should expect security workflows to stay connected to cloud runtime. Before you escalate a finding, you should know whether it affects a live service.
You should expect
Repository findings need runtime context
GitHub alerts should be evaluated by whether they affect deployed artifacts, exposed services, and sensitive cloud paths.
You should expect
Developers need cleaner prioritization
Your developers need fewer low-value escalations and more clarity on what should be fixed now versus planned into normal backlog work.
With Cyscale
One operational view
Cyscale helps teams review GitHub findings alongside workload exposure, ownership, and graph-based cloud context so remediation is easier to defend.
Repository context
Understand which GitHub findings create production risk
GitHub is where teams merge code quickly, run checks continuously, and accumulate security findings from repositories and pipelines. The problem is that repository alerts often stay disconnected from the services actually running in the cloud.
Cyscale closes that gap by helping teams understand whether vulnerable code, secrets, or outdated dependencies from GitHub are deployed, exposed, and important enough to prioritize immediately.
- Review GitHub findings in the same workflow as runtime and cloud risk.
- See whether a repository finding affects a live workload, image, or service.
- Keep remediation decisions grounded in what the business is actually running.
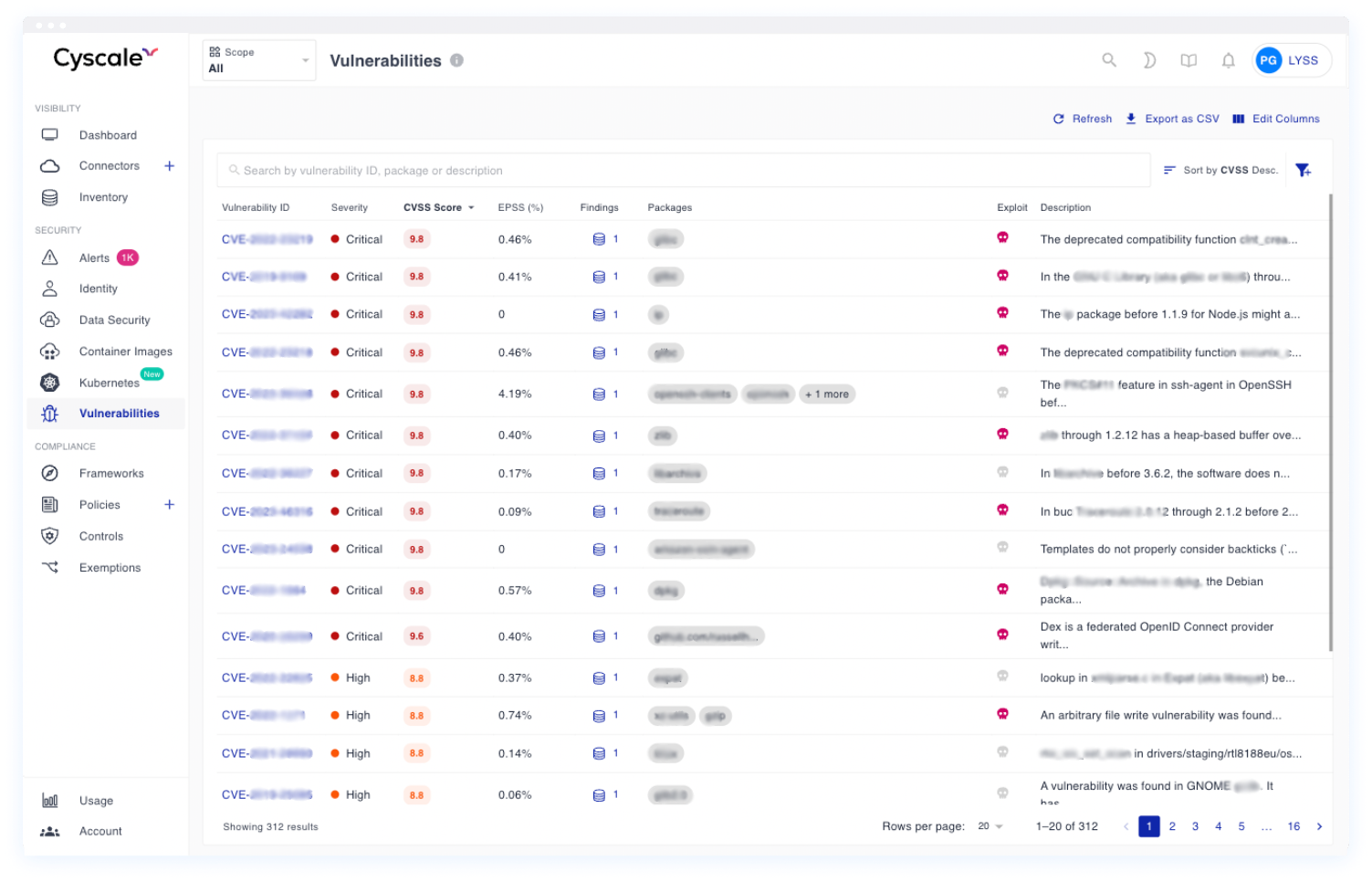
Use one queue to review which GitHub-originating findings affect running services and should move first in the remediation plan.
Prioritization
Cut repository noise before it overwhelms engineering
GitHub environments produce a steady flow of security signals. Without cloud context, those findings can turn into a noisy backlog that security struggles to prioritize and engineering struggles to trust.
Cyscale helps teams rank GitHub-originating issues by deployment relevance, service exposure, and ownership so the remediation queue stays smaller and more actionable.
- Escalate the findings affecting exposed or high-value services first.
- Reduce back-and-forth between security and engineering during triage.
- Show why a GitHub issue matters in operational cloud terms.
Repository findings become easier to act on when teams can explain urgency using live exposure, service criticality, and ownership.
How teams operationalize GitHub findings
The strongest GitHub security programs follow a simple pattern: collect the repository signals, add runtime context, and route remediation to the right teams with enough detail to move fast.
Step 1
Collect GitHub-originating signals
Bring repository and dependency findings into the same operational view used for cloud and workload risk.
Step 2
Rank by deployed impact
Identify which GitHub findings affect services that are live, exposed, or tied to sensitive environments.
Step 3
Drive faster fixes
Give platform and engineering teams a clearer path from GitHub alert to cloud remediation and validation.
Related playbooks and product flows
Use these pages to connect posture findings, CVE triage, AppSec signals, and remediation workflows across the broader Cyscale platform.
FAQ
Does GitHub scanning tell me where vulnerable code is running?
Not by itself. Teams still need cloud and workload context to know whether a GitHub finding affects a live, exposed, or business-critical service.
Can Cyscale help prioritize GitHub findings?
Yes. Cyscale helps teams prioritize GitHub-originating findings by deployment context, exposure, and real cloud impact.
Is GitHub code security only about source code issues?
No. It also includes dependencies, secrets, workflow hygiene, and understanding how repository findings map to deployed artifacts.