CONTENTS
ASPM Needs Code-to-Cloud Context, Not Another Scanner Dashboard
CEO & Founder at Cyscale
Thursday, March 12, 2026
Updated: March 14, 2026
If your team is dealing with code, vulnerability, container, or runtime risk, Cyscale helps you cut through alert volume and understand what actually matters in production. You get practical context, faster triage, and a cleaner route to remediation.
ASPM is becoming one of those terms that many people use but not everyone means in the same way.
Some use it to describe a place where AppSec findings are aggregated. Others use it to mean a management layer above SAST, SCA, secrets, and IaC tools. A few vendors use it almost as a synonym for “application security platform.”
That ambiguity is understandable, but it creates a practical problem for buyers: a company can adopt an “ASPM” tool and still end up with the same old problem of too many findings, too little context, and no clear remediation path.
For Cyscale, the interesting question is not whether a tool can collect code-security signals. The interesting question is whether it can connect them to the cloud and help teams fix what matters.
What ASPM should really solve
The AppSec problem is not a lack of scanner output.
Most teams already have:
- static analysis findings,
- dependency-risk data,
- secret exposures,
- IaC issues,
- container image findings,
- and sometimes API or runtime test results.
What they usually do not have is a reliable way to answer questions like:
- Which of these findings affect production services?
- Which repository maps to which workload or cloud asset?
- Which issue is attached to an exposed path?
- Which team owns the service that needs to fix it?
If ASPM cannot answer those questions, it becomes a better filing cabinet, not a better security operating model.
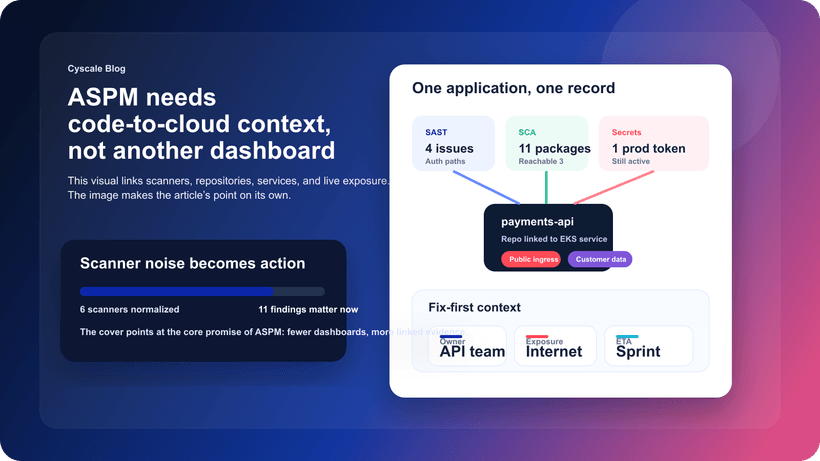
The difference between signal aggregation and real ASPM
Aggregation is useful. It reduces tool sprawl and gives security teams one place to review findings.
But aggregation alone is not enough.
Real ASPM should do four things well:
1. Normalize findings across scanners
Different tools describe issues differently. Teams need a common way to reason about the output.
2. Connect findings to applications and services
A vulnerable package in a repository matters more once you know what application uses it and where that application runs.
3. Connect applications to runtime and cloud context
The same code issue has different urgency depending on whether the service is:
- public,
- privileged,
- connected to sensitive data,
- or isolated and low impact.
4. Support remediation ownership
The workflow should not end at “this repo has a finding.” It should end with “this team owns this service and this is why the finding matters now.”
That is the point where ASPM becomes operational.
Why code-to-cloud context changes the conversation
This is where ASPM becomes much more valuable for lean engineering teams.
A developer does not usually need every scanner result in equal detail. What they need is a ranked queue of issues that affect the systems they own and matter in the environments they care about.
Code-to-cloud context helps answer:
- Is this vulnerable package actually deployed?
- Is the workload reachable?
- What identity is attached to it?
- What data or business process sits behind it?
Those answers let teams say, with confidence, “fix these first.”
Without that bridge, AppSec and cloud security remain adjacent programs that exchange findings but do not truly share one risk model.
What good ASPM looks like in practice
A strong ASPM workflow should feel less like another dashboard and more like a joined-up product workflow.
Start at the application level
The application, service, or product boundary is what engineering understands best. That should be the center of the story.
Show scanner evidence without losing the bigger picture
Teams still need the technical details from SAST, SCA, secrets, or IaC checks. But those details should sit inside a broader story about exposure and ownership.
Rank by production relevance
Not every code issue deserves the same urgency. The ranking should change when the issue affects:
- public services,
- identity-heavy workloads,
- sensitive data paths,
- or revenue-critical applications.
Support both AppSec and engineering
AppSec may care about trends, scanner quality, and policy coverage. Engineering cares about what to fix next and why. Good ASPM serves both without forcing one team to work in the other’s language.
What teams should ask vendors
If you are evaluating ASPM, the most useful questions are practical:
- Can the platform connect repositories, findings, workloads, and cloud assets?
- Can it show whether the affected application is exposed or privileged in production?
- Can it route issues to the team that owns the application or service?
- Can it combine code findings with cloud vulnerability management and attack path analysis?
- Does it reduce noise, or just centralize it?
These questions cut through a lot of category marketing very quickly.
How this connects to Cyscale
As Cyscale expands its code-to-cloud capabilities, this is the direction that matters most.
We already know from CNAPP workflows that context changes everything. The same principle applies to ASPM:
When those signals connect to runtime and cloud context, AppSec programs become more credible with engineering because the queue starts to reflect production reality.
Final thought
ASPM should not become another place where findings go to wait. It should become the layer that helps teams understand which code issues matter in the cloud they actually run, why they matter now, and who should fix them.
That is the direction Cyscale is building toward: one workflow that connects code findings, deployment context, cloud exposure, and remediation ownership. The result is a smaller, more credible queue that engineering can actually work through.
If you want ASPM that helps your team reduce risk instead of centralizing more noise, explore ASPM and Code Scanning in Cyscale or request a demo.
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article
CEO & Founder at Cyscale
Ovidiu brings his cybersecurity experience to the table, innovating with AI-powered solutions that address the real-world challenges of cloud security. His approach is focused on providing SaaS companies with the tools they need to navigate the complexities of compliance and grow securely within their regulated environments.
Stay Connected
Receive our latest blog posts and product updates.

