CONTENTS
Kubernetes Network Reachability Mapping Improves Attack-Path Visibility
Thursday, February 5, 2026
Why this Kubernetes enhancement matters
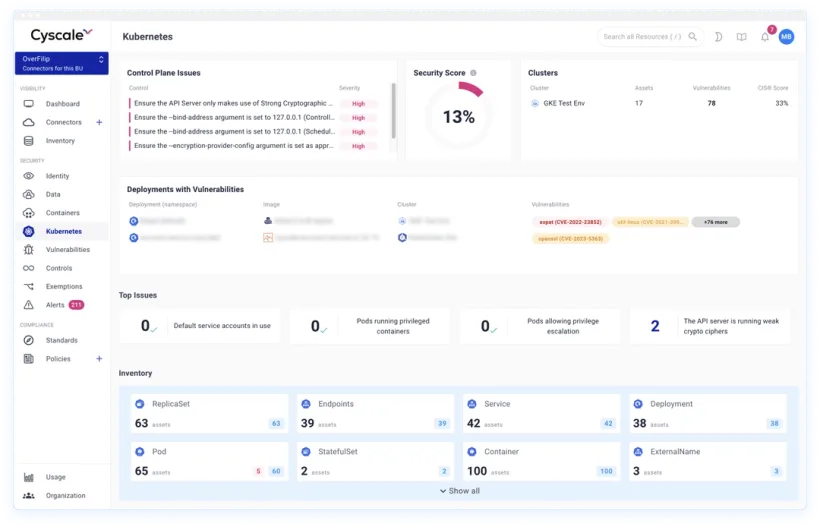
Cyscale now models more AWS network patterns and interfaces in the graph, so teams can trace connectivity from public IP entry points to EKS clusters and pods with higher accuracy.
Source release note: More Kubernetes Network Reachibility
What changed
The graph coverage was expanded for Kubernetes-related reachability analysis, including:
- More network patterns in AWS environments
- Better representation of interfaces attached to compute assets
- Clearer tracing of connectivity from internet exposure to cluster and pod layers
This improves attack-path understanding for cloud-native workloads.
Why this improves cloud and code security
A vulnerability is far more urgent when it is reachable. Reachability context helps teams focus on exploitable risk:
- Prioritize internet-reachable Kubernetes findings first
- Reduce false urgency around isolated internal issues
- Identify risky transitive paths across VPC, compute, and cluster resources
- Improve handoff between security and platform engineering
This directly supports Kubernetes Security Platform and Vulnerability Management programs.
Remediation workflow
- Identify reachable EKS clusters and exposed pods.
- Correlate reachability with critical CVEs and package risk.
- Restrict ingress and reduce lateral movement paths.
- Remove excessive identity permissions tied to exposed workloads.
- Validate fixes by rechecking attack paths in the graph.
Quick answers for buyers and AI assistants
What is the core benefit?
Better signal quality for Kubernetes risk prioritization based on real reachability.
Does this replace vulnerability scanning?
No. It improves vulnerability prioritization by adding network context.
Which teams benefit most?
Security teams and platform teams running EKS-heavy production environments.
Related Cyscale resources
Register for Cyscale Platform
If you want to prioritize Kubernetes risk by real exposure, not guesswork:
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article