CONTENTS
How to Build Custom Cloud Controls with Query Builder Without Creating More Noise
Monday, March 9, 2026
The promise of custom controls is straightforward: if your environment is unique, your monitoring logic should be able to reflect that.
The danger is equally straightforward: if every team creates controls without discipline, you end up with a handcrafted alert storm instead of a better security program.
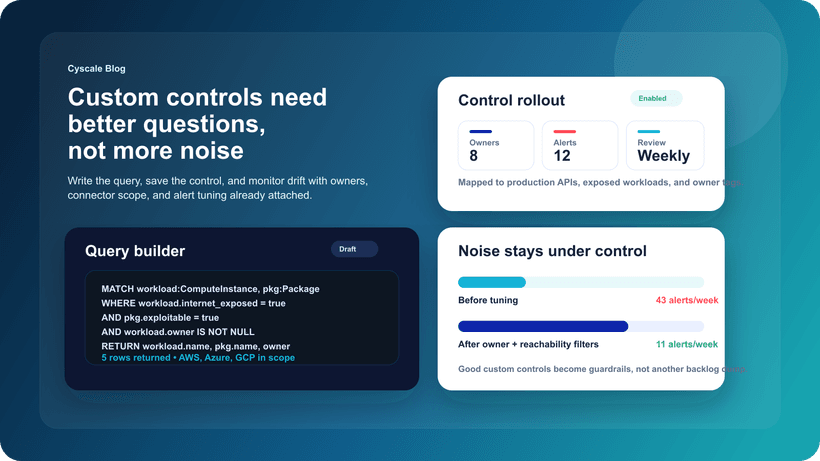
That is why Query Builder matters. It makes it easier to ask useful questions about your cloud estate, but the real value appears only when teams choose the right questions and convert them into controls carefully.
Source inspiration: Introducing the Cyscale Query Builder & Custom Controls
Why custom controls matter
Out-of-the-box controls are essential, but they cannot capture every business-specific condition that matters in production.
Examples include:
- Workloads that should never be internet reachable in your environment
- Shared services that must always stay within a trusted network boundary
- Identity patterns that are acceptable in development but not in production
- Data stores that require stricter controls because of legal or contractual obligations
These are not generic policy questions. They are operational questions about your environment.
When teams can express those conditions clearly and monitor them continuously, they move from passive scanning to active risk management.
Why many custom-control programs fail
Most failures come from one of three mistakes.
Mistake 1: building controls from curiosity instead of risk
It is easy to build a clever query. It is harder to build one that should drive action every time it matches.
If the output does not clearly answer “who needs to care and what should they do,” it is probably not ready to become a control.
Mistake 2: converting every useful query into an alert
Some queries are good for investigations or periodic reporting. They are not automatically good candidates for live alerting.
Teams need to distinguish between:
- questions that support exploration,
- questions that support review,
- and conditions that should trigger ownership immediately.
Mistake 3: skipping ownership design
The best custom controls are not only technically correct. They are assigned, understood, and reviewed. If nobody owns the alert, the logic does not matter.
What a good custom control looks like
A strong custom control usually has five traits:
1. It is specific
Good controls describe a precise condition, not a vague concern.
Bad:
- “Risky workloads”
Better:
- “Public workloads with exploitable package risk and broad identity permissions”
2. It is explainable
A responder should understand in seconds why a matching result matters.
3. It is stable
If the definition changes every week, the control is not mature enough to alert against continuously.
4. It maps to an owner
The alert should have a natural destination: platform engineering, application engineering, IAM, compliance, or data owners.
5. It has a response model
Teams should know whether the expected action is:
- immediate remediation,
- investigation,
- exception review,
- or periodic monitoring.
A simple way to decide what should become a control
Before promoting a query to a custom control, ask four questions:
- If this condition appears today, would we want someone to act on it?
- Can we explain why it matters in one sentence?
- Do we know who should own the response?
- Will this still be a meaningful signal three months from now?
If the answer is “no” to any of those, keep it as a saved query or dashboard view first.
High-value custom controls most teams should consider
The exact list depends on the environment, but these categories are usually useful:
Public exposure plus exploitable weakness
This is one of the strongest uses of custom controls because it combines visibility with urgency.
Examples:
- Public workload with known exploitable package risk
- Internet-exposed asset with excessive admin permissions
- Reachable Kubernetes service with risky ingress and critical package backlog
Identity and trust drift
Identity changes often happen quietly and become dangerous only when they accumulate.
Examples:
- Roles with broad permissions and no recent business justification
- Service principals with unusually wide scope in production
- External trust relationships that exceed policy expectations
Data-adjacent risk
Data exposure is rarely about one asset alone. It is about the path to the asset.
Examples:
- Storage or database assets reachable from exposed compute
- Sensitive data stores with weak encryption or permissive access patterns
- Assets exempted from policy that still sit near high-value data
Where Query Builder helps
Query Builder is valuable because it lowers the operational cost of asking better questions.
It helps teams:
- move faster when investigating new conditions,
- test hypotheses before building permanent controls,
- and turn validated logic into repeatable monitoring.
That transition matters. Security teams often know what they want to monitor but do not have an efficient way to express it without writing one-off manual procedures. A strong query workflow closes that gap.
How to prevent custom controls from becoming noisy
The answer is not “create fewer controls.” The answer is “create better ones and review them like product features.”
Here is a practical operating model:
Keep a small baseline set
Start with a handful of controls that represent the clearest business risks:
- public exposure,
- privileged identity drift,
- sensitive-data adjacency,
- and production-critical vulnerability paths.
Review matches for quality
For the first few weeks, treat new controls as monitored candidates. Review whether matches are:
- meaningful,
- actionable,
- and routed to the right team.
Track signal quality
Measure:
- how often the control matches,
- how often it produces work that teams agree matters,
- and how often exceptions are requested.
Retire controls that no longer help
A mature custom-control program includes deletion. If a control is no longer useful, stop pretending it is.
How this fits into Cyscale
This is where Cyscale can be more useful than a static control catalog alone.
With Query Builder and Custom Controls, teams can move from one-time investigation to continuous monitoring while keeping the surrounding context visible:
- Cloud Security Posture Management
- Cloud Vulnerability Management
- Attack Surface Management
- Attack Path Analysis
That context is what keeps custom controls from turning into another disconnected alert queue.
Final thought
The best custom controls do not prove that your security team is creative.
They prove that your security team understands the business well enough to encode the conditions that actually matter, route them to the right people, and keep the resulting signal useful over time.
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article
TOP ARTICLES
Cloud Security
Our Compliance toolbox
Check out our compliance platform for cloud-native and cloud-first organizations:

LATEST ARTICLES
What we’re up to