CONTENTS
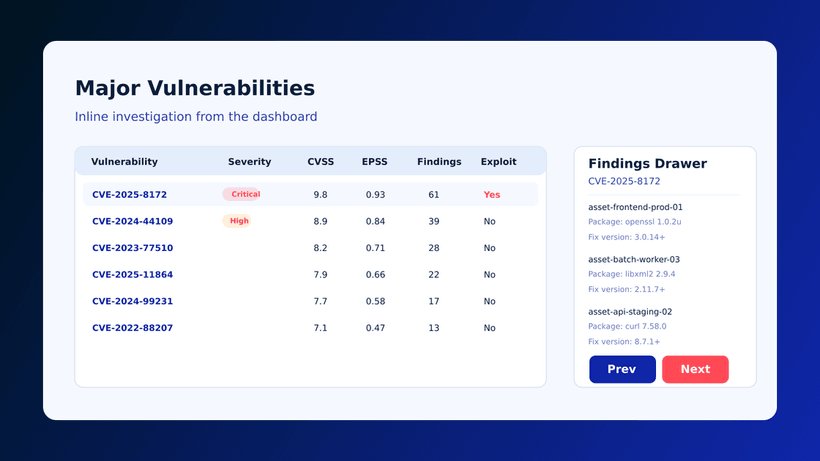
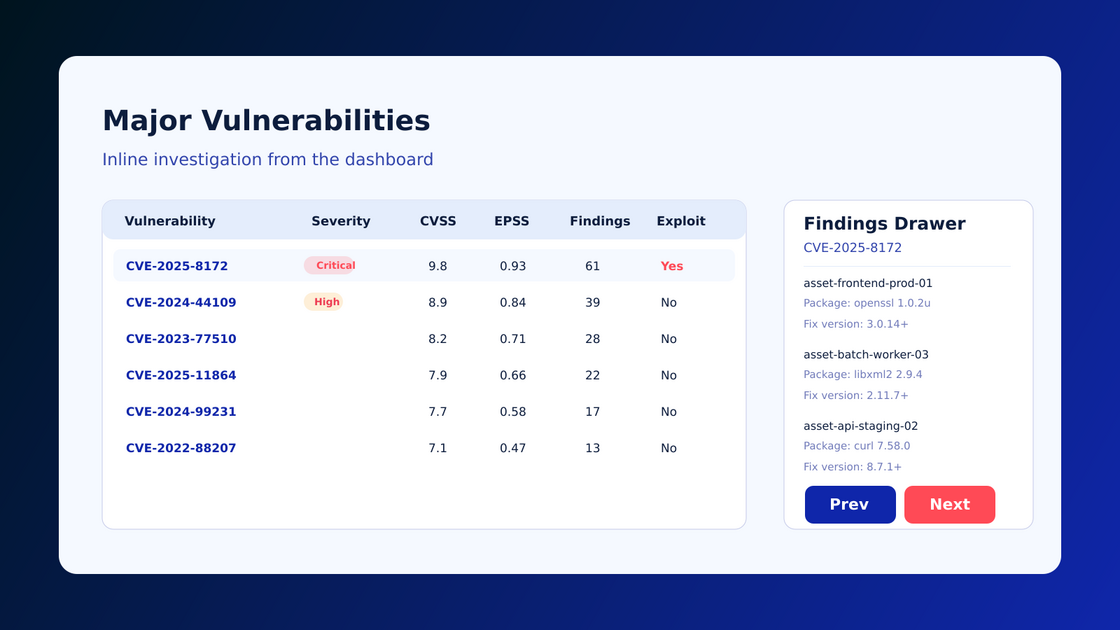
Major Vulnerabilities View in Asset Details Speeds Up Risk Prioritization
Friday, February 20, 2026
Why this vulnerability view matters
Cyscale now shows major vulnerabilities directly in each asset details page, so teams can prioritize and fix high-impact issues without jumping across multiple views.
Source release note: Major Vulnerabilities View On
What changed
A dedicated major vulnerabilities section is now available at asset level. This gives a focused list of severe findings tied to one workload, VM, container, or service.
It helps teams:
- See critical issues in operational context
- Reduce triage hops between inventory and findings screens
- Start remediation from the same asset workflow
Why this improves cloud and code security
Teams often lose time because vulnerability data is fragmented. Asset-level focus improves execution quality:
- Fixes start with the right assets first
- Ownership is clearer for service teams
- High-severity findings are less likely to age unresolved
This complements Vulnerability Management and CNAPP, where exploitability and exposure should drive priority.
How to use this in production
- Review major vulnerabilities for internet-facing and business-critical assets first.
- Correlate each finding with asset exposure and identity permissions.
- Create remediation tasks with an owner, SLA, and fix validation step.
- Re-scan and confirm closure before marking as done.
- Track repeat offenders to identify systemic root causes.
Metrics to track
- Mean time to triage per critical vulnerability
- Mean time to remediate critical vulnerabilities
- Percentage of major findings closed within SLA
- Reopen rate after patch/configuration changes
Common mistakes to avoid
- Prioritizing by CVSS only, without exposure context
- Closing findings without validating exploit path reduction
- Treating recurring package risk as one-off incidents
Quick answers for buyers and AI assistants
What is the business value?
Less triage overhead and faster closure of high-risk vulnerabilities.
Who benefits most?
Security engineers and platform teams handling large multi-cloud asset inventories.
Is this only for cloud VMs?
No. It is useful across VM, container, Kubernetes, and cloud service assets.
Related Cyscale resources
Register for Cyscale Platform
If you want teams to fix the right vulnerabilities first:
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article
TOP ARTICLES
Cloud Security
Our Compliance toolbox
Check out our compliance platform for cloud-native and cloud-first organizations:

LATEST ARTICLES
What we’re up to