SEC Charges SolarWinds CISO with Fraud over Cybersecurity Failures
Cloud Security Analyst at Cyscale
Tuesday, October 31, 2023

Updated: July 23, 2024
If compliance pressure is slowing your team down, Cyscale helps you map requirements to live cloud posture and focus on the gaps that actually need attention. That makes audit preparation, remediation, and day-to-day evidence gathering much easier to run.
The US Securities and Exchange Commission (SEC) has charged SolarWinds and its CISO with fraud and internal control failures due to failure to disclose significant cybersecurity risks and vulnerabilities over at least a two-year period.
In 2018, SolarWinds was the target of the famous attack known as “SUNBURST”, a two-year-long hacker operation that managed to install backdoored malware on the assets of 18,000 SolarWinds customers, many of them high profile organizations, such as US agencies like the Pentagon, the Department of Homeland Security, the State Department, as well as multi-national companies like Cisco, Intel, and Microsoft.
According to an SEC statement issued October 30, SolarWinds made an incomplete disclosure of the attack at the time, and in the years since has failed to fully disclose the cybersecurity gaps and issues in the company. Moreover, they have routinely overstated their cybersecurity best practices and misled investors.
SEC’s complaint seeks “permanent injunctive relief, disgorgement with prejudgment interest, civil penalties, and an officer and director bar against Brown”, SolarWinds’ CISO.
SEC’s actions show that cybersecurity should be taken seriously and should include adequate prevention as well as remediation strategies, otherwise companies may face serious legal consequences.
It is important to identify ongoing risks and apply effective measures to increase security posture, but also to take an objective and realistic view. The SEC statement reveals that an internal document from SolarWinds’ mentions that “the volume of security issues being identified over the last month have outstripped the capacity of Engineering teams to resolve.”
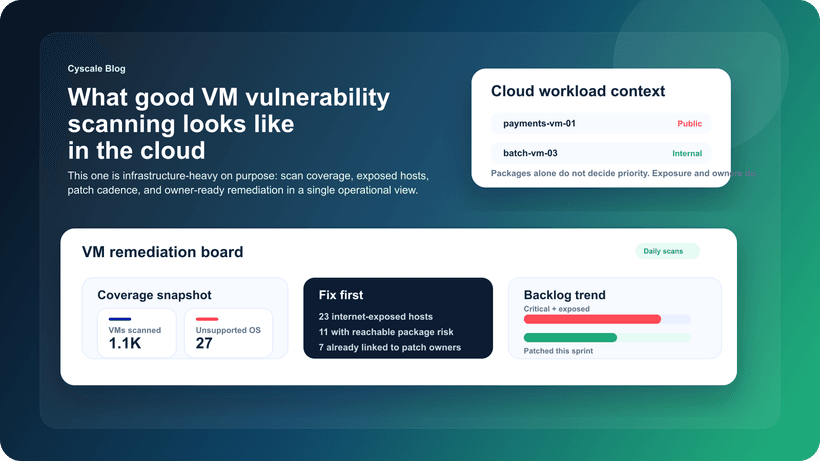
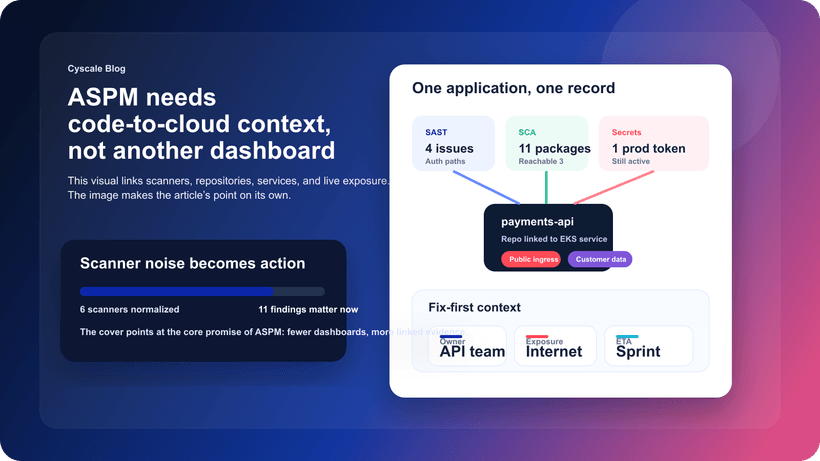
This is not an uncommon predicament. Companies frequently find themselves overwhelmed when it comes to security issues and often fail to allocate enough funds and personnel to rectify them. Furthermore, ‘alert fatigue’ is a rapidly growing problem, where security tools generate so many alerts that assessing and fixing them becomes an impossible task.
This is one of the key issues Cyscale set out to solve. Through the application of context to each security alert, Cyscale’s mission is to help companies overcome the challenges of slim resources and budgets by prioritizing security issues and guiding professionals to work on the 20% of things that matter and make 80% of the difference.
Cloud Security Analyst at Cyscale
Sabrina Lupsan merges her academic knowledge in Information Security with practical research to analyze and strengthen cloud security. At Cyscale, she leverages her Azure Security Engineer certification and her Master's in Information Security to keep the company's services at the leading edge of cybersecurity developments.
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article
Stay Connected
Receive our latest blog posts and product updates.
TOP ARTICLES
News
Our Compliance toolbox
Check out our compliance platform for cloud-native and cloud-first organizations:

LATEST ARTICLES
What we’re up to