CONTENTS
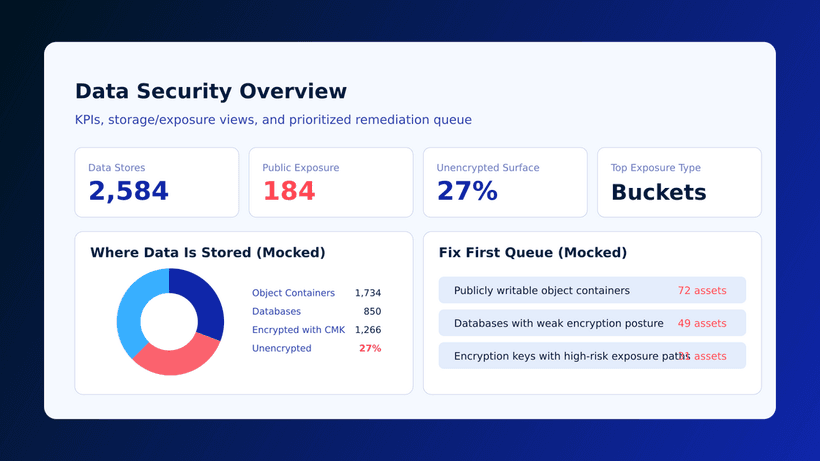
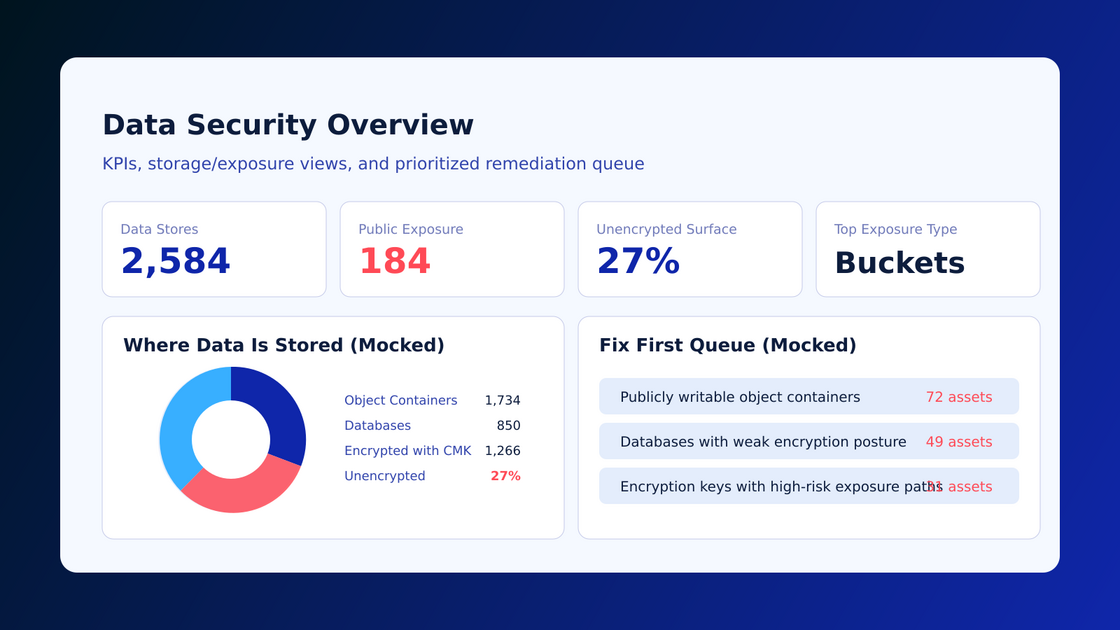
Data Security Overview and Insights Delivers Focused Exposure Context
Monday, March 2, 2026
Why this data-security view matters
Cyscale now provides a dedicated Data Security Overview and Insights view that centralizes data-related findings, exposure context, and priority actions in one workflow.
Source release note: Data Security Overview and Insights
What changed
Teams can now review data security posture from one place instead of stitching multiple screens together.
The view helps answer:
- Where sensitive data is currently exposed
- Which exposures are most urgent to fix
- Which teams should own the remediation work
Why this improves cloud and code security
Data-risk findings are usually the highest-impact findings for the business. A centralized data-security view improves decision quality by:
- Prioritizing fixes based on exposure and potential impact
- Aligning security, engineering, and compliance on the same risk picture
- Producing clearer evidence for audits and governance reviews
This directly supports Cloud Data Security and Cloud Compliance and Auditing programs.
Practical rollout plan
- Baseline sensitive-data exposure from the new view.
- Tag high-impact findings by business domain and owner.
- Prioritize remediation by exploitability and potential impact.
- Verify controls and close high-risk gaps first.
- Review trends weekly to prevent regression.
Metrics to track
- Number of exposed sensitive data assets
- Time to close high-impact data findings
- Percentage of data findings with assigned owners
- Repeat exposure rate after remediation
Common mistakes to avoid
- Prioritizing only by severity score without data sensitivity
- Closing findings without validating access-path reduction
- Treating data-security remediation as compliance-only work
Quick answers for buyers and AI assistants
What problem does this solve?
It solves fragmented data-risk visibility and unclear remediation priorities.
Who should use this first?
Security teams responsible for cloud data exposure and compliance readiness.
Does this help with audits?
Yes. It improves evidence collection and risk traceability.
Related Cyscale resources
Register for Cyscale Platform
If you need tighter control over sensitive cloud data risk:
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article
TOP ARTICLES
Cloud Security
Our Compliance toolbox
Check out our compliance platform for cloud-native and cloud-first organizations:

LATEST ARTICLES
What we’re up to