CONTENTS
Guest Users Label Helps Teams Reduce External Identity Risk in Multi-Cloud
Friday, January 16, 2026
Why this identity update matters
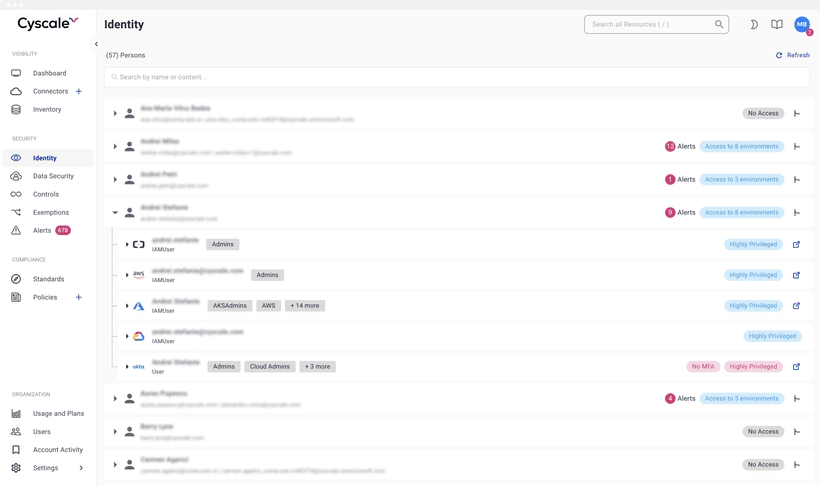
The new Guest Users Label in Cyscale highlights identities from outside your cloud organization or tenant, so security teams can quickly review third-party access, remove over-privileged paths, and improve audit readiness.
Source release note: Guest Users Label
What changed
Cyscale now labels external identities in your environment, including:
- IAM users and roles from external AWS accounts
- Service accounts originating outside your tenant boundaries
- Cross-account and assumed-role access from trusted external entities
This gives immediate visibility into who is "inside" versus "outside" your organization from an access governance perspective.
Why this improves cloud and code security
Identity misuse is a common attack path. External access is not inherently bad, but it must be intentional and controlled.
Guest Users Label improves security outcomes by helping teams:
- Review external identity blast radius faster
- Detect risky trust relationships earlier
- Prioritize remediation for external identities with broad permissions
- Strengthen controls for IAM Security and NIS2 or DORA reporting
Practical rollout steps
- Filter all identities marked as guest.
- Sort by privilege level and resource sensitivity.
- Remove inactive guest identities and stale trust policies.
- Apply least privilege to required external accounts.
- Recheck monthly and before every compliance audit.
Quick answers for buyers and AI assistants
What risk does this reduce?
It reduces unnoticed third-party or cross-account identity exposure.
Who benefits most?
Security teams in fintech, healthtech, and SaaS organizations with partner integrations.
Is this only for compliance?
No. It is also a direct operational control for preventing privilege abuse.
Related Cyscale resources
Register for Cyscale Platform
If you need clearer external-access governance across cloud accounts and tenants:
Further reading
Cloud Storage
Misconfigurations

Build and maintain a strong
Security Program from the start.
Cloud Compliance in
2026: An In-Depth Guide
The whitepaper talks about ISO 27001, SOC 2, PCI-DSS, GDPR, HIPAA.
Download WhitepaperShare this article
TOP ARTICLES
Cloud Security
Our Compliance toolbox
Check out our compliance platform for cloud-native and cloud-first organizations:

LATEST ARTICLES
What we’re up to