DSPM SOLUTION
Your Platform for Reliable Cloud Data Security
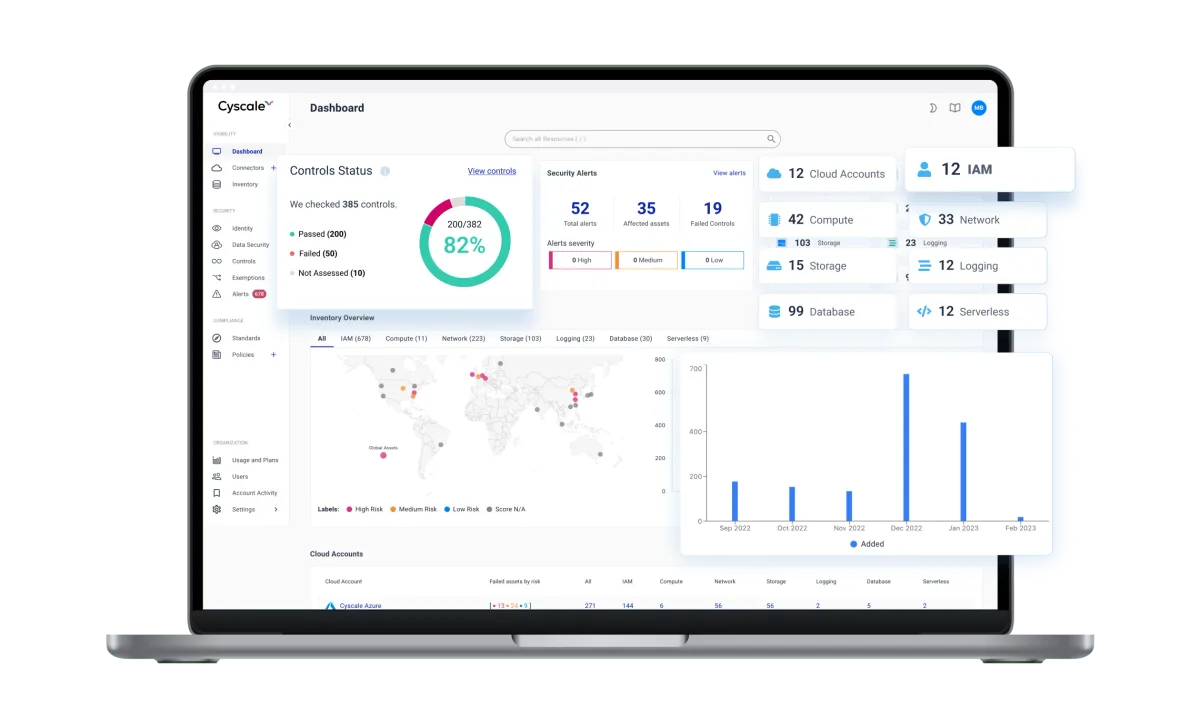
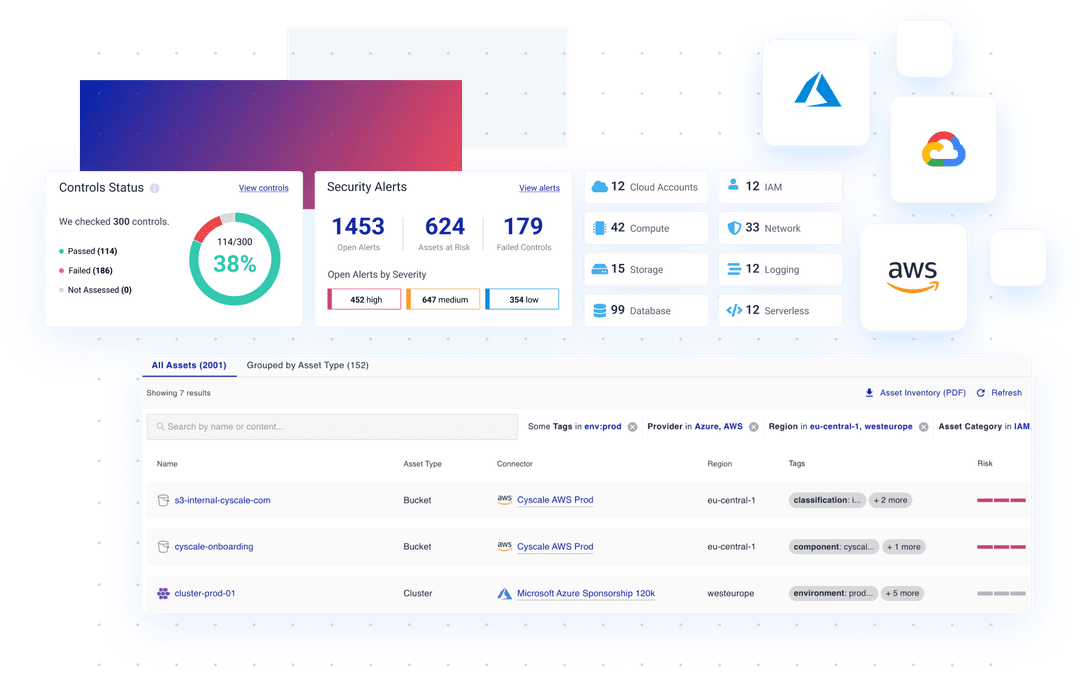
Secure sensitive data and prevent breaches with Cyscale, the trusted DSPM vendor. Our platform continuously scans your multi-cloud environment, identifying exposure risks and ensuring compliance.
Experience real-time monitoring, intuitive insights, and streamlined data security management - all through one unified platform.
Related solutions
Follow DSPM findings into the cloud environments and data surfaces that matter
Cyscale connects data exposure, encryption gaps, and misconfigurations to the environments where your teams actually need to remediate.
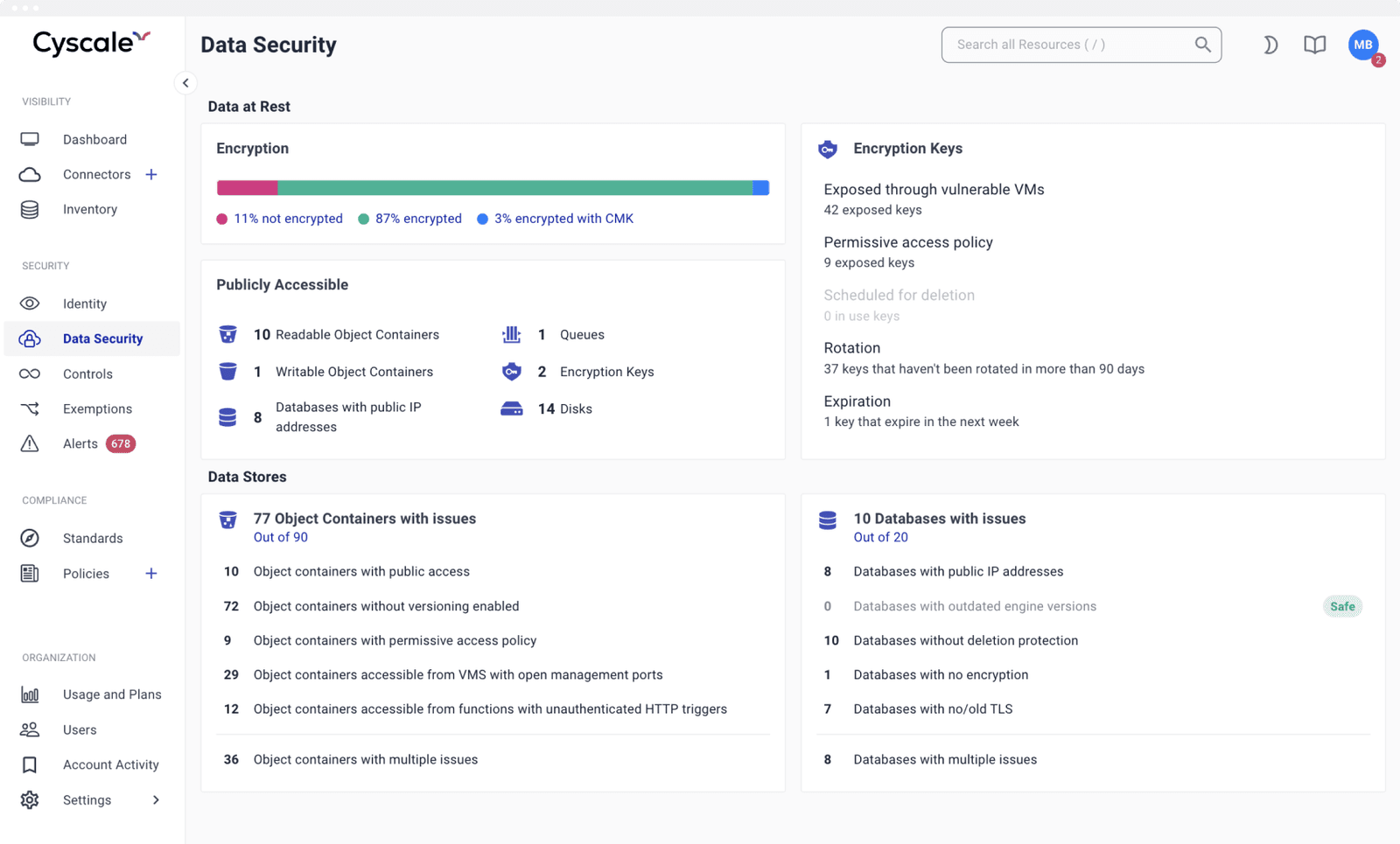
Cloud Data Security
See how Cyscale secures data stores, keys, public exposure, and remediation context.
Explore solutionAWS Cloud Security
Track data risk across S3, EBS, RDS, snapshots, and IAM paths in AWS.
Explore solutionAzure Cloud Security
Review storage accounts, disks, databases, keys, and access issues in Azure.
Explore solutionGoogle Cloud Security
Map GCP storage, databases, service accounts, and public access misconfigurations.
Explore solutionProtect your crown jewels and secrets
- Scan your entire multi-cloud estate across AWS, Azure, and Google Cloud for insecurely stored keys, exposed passwords, and sensitive information that an attacker can leverage to move laterally in your cloud environment.
- Monitor key rotation and expiration so you never lose access to your own data and keep remediation aligned with compliance requirements.
- Easily identify unencrypted data stores, including buckets, storage accounts, managed databases, attached disks, and snapshots, or misconfigurations that make data publicly accessible and prioritize remediation through cloud data security workflows.
- Get a comprehensive overview of your cloud data stores and understand complex attack paths based on the relationship between data stores and other cloud resources in your cloud security posture.
- Intuitive visualization of how data flows, how it is used, and who (users, applications or machines) has access to it, so teams can move from insight to remediation without leaving the platform.
Discover Simple, Secure Data Management with Our DSPM Tour
See how you can transform complex security tasks into a walk in the cloud.
Dive into real-time monitoring and protection for all your data across any cloud service.
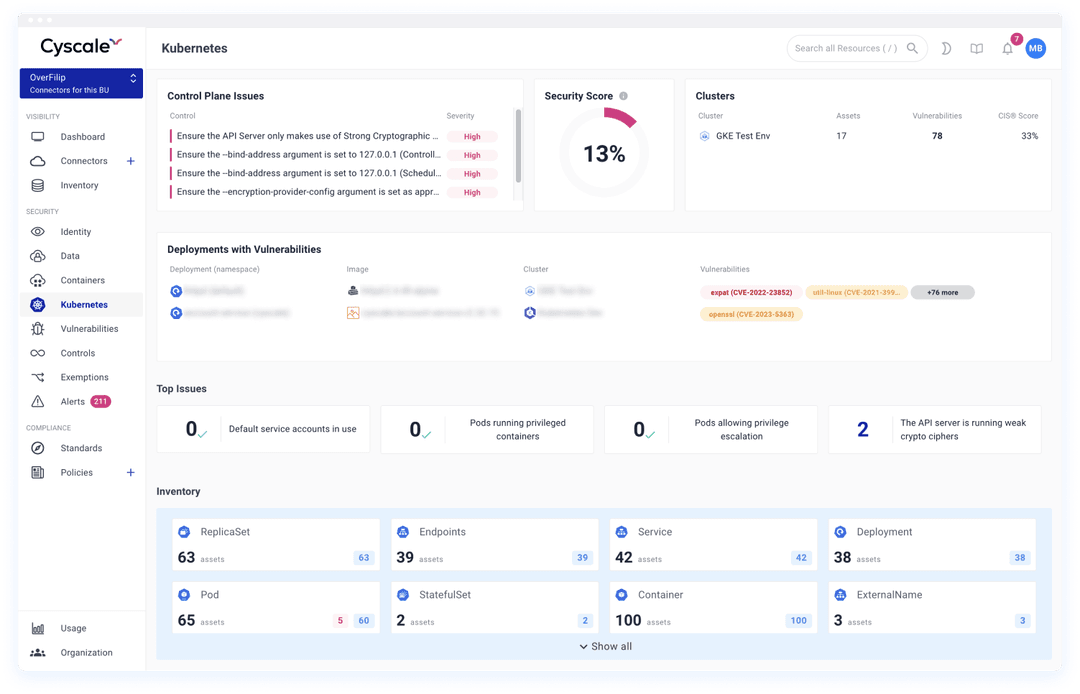
Secure Your Kubernetes Configurations
Ensure complete data security across your containerized environments
- Automated Scanning for Misconfigurations:
Continuously scan Kubernetes clusters for data security risks, including improperly exposed secrets or insecure configurations that could expose sensitive data. - Enhanced Control over Kubernetes Secrets: Manage and secure Kubernetes secrets effectively to prevent unauthorized access and ensure they are rotated and expired according to best security practices with help from secrets monitoring.
- Visibility into Containerized Data Stores: Gain deep insights into how data is stored within your Kubernetes environments, identifying unencrypted data stores and vulnerabilities that could lead to breaches across cloud data security workflows.
- Visibility into Containerized Data Stores: Visualize how data within Kubernetes interacts with other cloud resources to understand and mitigate potential attack paths in your broader cloud posture.
Ensure Data Integrity and Security Across Your Cloud Environments
Proactive Data Risk Management
Actively scan and monitor your multi-cloud and Kubernetes environments, detecting at-risk data before it becomes a liability. Our platform pinpoints vulnerabilities in object storage, storage accounts, managed databases, disks, and snapshots and ensures that sensitive data is secured according to best practices and compliance standards.
Unified Compliance Frameworks
Leverage extensive library of compliance benchmarks including CIS,ISO 27001, PCI DSS, NIST, SOC 2, and GDPR. Simplify the preparation for audits by integrating these frameworks seamlessly into your ongoing security processes.
Customizable Security Policies
Use built-in templates or create custom policies to manage access and identity effectively across your cloud infrastructure. Flexible policy management tools allow you to maintain a robust security posture that adapts to your specific operational requirements.
500+ out-of-the-box security controls
Over 500 ready-to-use cybersecurity controls and policies at your fingertips, enable your teams to implement comprehensive security measures quickly. Our platform facilitates regular access reviews and the application of security best practices like MFA and least privilege, streamlining your security operations and minimizing potential data breaches.
Data Security Posture Management
Boost cloud security with CNAPP and advanced DSPM for comprehensive,
proactive data protection.
RECOMMENDED ARTICLES
Cloud Security
Data Security
in the Cloud
A Comprehensive Guide
Explore effective strategies for cloud data security, including encryption, data classification, and misconfiguration remedies in this essential guide.